WhatsApp adds Incognito Chat for private Meta AI conversations
The company launched Incognito Chat with Meta AI, a feature that lets users hold AI conversations the platform itself cannot read. The rollout will reach WhatsApp and the …

Signal responds to phishing attacks with new in-app security warnings
Signal is adding new protections for users following recent phishing and social engineering attacks. In March, the FBI and CISA issued a warning stating that Signal had become …
KDE gets over €1 million investment to strengthen security and core infrastructure
European governments and public institutions have been shifting away from proprietary software for years, and the financial infrastructure supporting open-source alternatives …

Microsoft’s agentic security system found four critical Windows RCE flaws
Microsoft responded to growing competition in AI security by announcing that its new agentic security system helped researchers discover 16 new vulnerabilities in the Windows …
Sandyaa: Open-source autonomous security bug hunter
Source code auditing has traditionally relied on static analyzers that flag long lists of potential issues, leaving engineers to sort bugs from noise. A new open-source …
The hidden risk of non-human identities in AI adoption
An employee with persistent, unsupervised admin access across critical systems, with no audit trail, no clear owner, and no regular access reviews, would raise immediate …

Researchers open-source a Wi-Fi cyber range for security training
Wireless security training programs lean heavily on generic network labs, with Wi-Fi appearing as a checkbox alongside Bluetooth, Zigbee, and cellular. Hands-on environments …
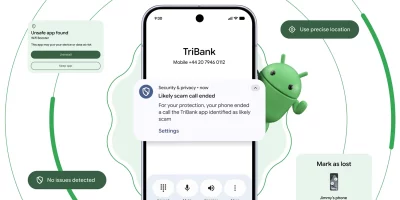
Android pushes new scam, theft, and AI protections in 2026 update wave
Phone scammers spoofing bank caller IDs have driven an estimated $980 million in annual losses worldwide, according to Europol. Android’s 2026 security roadmap takes …

Fedora Hummingbird brings the container security model to a Linux host OS
Container image security pipelines have spent the past several years pushing toward minimal footprints, hermetic builds, and continuous CVE remediation. The Fedora Project is …
Microsoft May 2026 Patch Tuesday: Many fixes, but no zero-days
Microsoft has marked May 2026 Patch Tuesday by releasing fixes for 120+ CVE-numbered vulnerabilities, none of which (for a change) are actively exploited or have been publicly …

Stealthy hackers exploit cPanel flaw in active backdoor campaign (CVE-2026-41940)
Security researchers at XLab have outlined an active attack campaign targeting CVE-2026-41940, the recently disclosed vulnerability in cPanel & WHM, and have linked it to …

Amazon Quick authorization bypass let users reach blocked AI chat agents
Enterprises running Amazon Quick, the AWS business intelligence and agentic AI service, rely on a feature called custom permissions to restrict who inside an account can use …
Featured news
Resources
Don't miss
- Sandyaa: Open-source autonomous security bug hunter
- The hidden risk of non-human identities in AI adoption
- Researchers open-source a Wi-Fi cyber range for security training
- Android pushes new scam, theft, and AI protections in 2026 update wave
- Microsoft May 2026 Patch Tuesday: Many fixes, but no zero-days