Stellar Cyber advances agentic AI for SOC to reduce noise and speed investigations
Stellar Cyber has introduced agentic AI to cut alert noise and speed investigations, changing how SOC teams operate. The enhancements advance its autonomous SOC platform, shifting teams from reactive alert handling to outcome-driven security operations.
AI that works with analysts, not instead of them
Security teams face an unsustainable reality: overwhelming alert volumes, fragmented tools, and increasingly sophisticated adversaries.
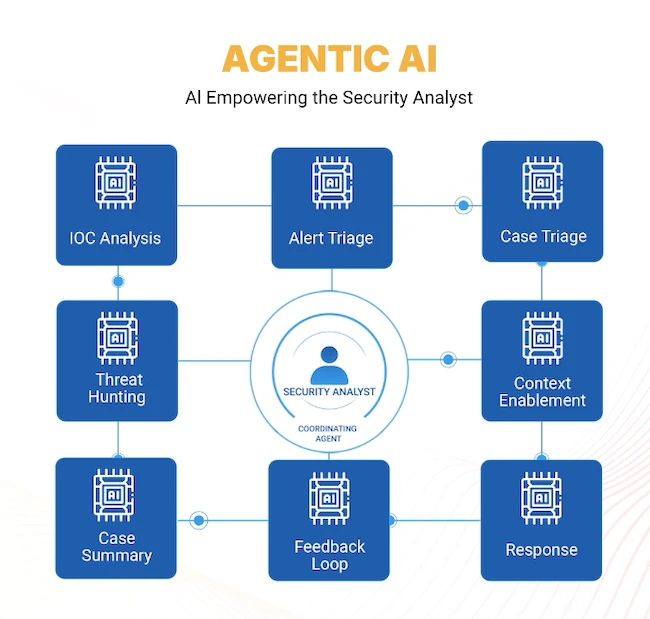
Stellar Cyber’s platform introduces coordinated agentic AI reasoning embedded directly into analyst workflows, enabling AI to analyze signals, prioritize threats, and recommend actions while keeping humans firmly in control.
“Security operations have reached a tipping point,” said Aimei Wei, CTO of Stellar Cyber. “The volume and complexity of alerts are simply beyond what human analysts can manage alone. Our approach is to combine machine-speed analysis with human judgment. AI handles the data and correlation at scale, while analysts remain in control of decisions that matter.”
Eliminating alert noise and accelerating investigation
One of the most significant new capabilities is automated alert triage, which evaluates incoming alerts, enriches them with contextual intelligence, and determines likely true or false positives before analysts ever see them.
Early adopters are seeing dramatic improvements in operational efficiency, including:
- 60–80% reduction in analyst triage time
- Up to 70% reduction in alert noise
The system uses an AI-driven Verdict Signal Check (VSC) model combined with human-in-the-loop oversight, ensuring that automation improves accuracy without sacrificing transparency or control.
In parallel, AI-generated case analysis now automatically summarizes high-severity incidents, reconstructs attack timelines, identifies affected assets, and recommends response actions.
This transforms incident investigation from manual data review into machine-assisted security reasoning.
Phishing response in minutes instead of hours
Phishing remains one of the most persistent operational challenges for SOC teams.
Stellar Cyber’s automated phishing analysis capabilities dramatically reduce analyst workload by evaluating user-reported emails, filtering out benign messages, and escalating only high-confidence threats into investigation workflows.
Tasks that previously required hours of manual analysis can now be completed in minutes.
A SOC built for real-world operations
Beyond AI automation, Stellar Cyber is also introducing enhancements designed to improve the operational experience of security teams.
New capabilities include:
- Custom case queues that allow SOC teams to organize investigations based on escalation level, SLA priority, or customer tier
- Improved detection coverage for web application exploitation and VPN credential abuse
- Modernized dashboards with responsive layouts and drag-and-drop customization
- Expanded integrations across the Open XDR ecosystem
These improvements are designed to reduce friction in daily SOC operations while improving visibility and collaboration.
A different approach to AI in security operations
Unlike many vendors that apply AI to isolated parts of the security stack, Stellar Cyber embeds Multi-Layer AI across the entire SecOps lifecycle — from data ingestion and correlation to investigation and automated response.
The platform unifies SIEM, NDR / OT, ITDR / UEBA, detection, investigation, triage, and response within a single open architecture.
“This is about transforming the daily life of the SOC analyst,” said Subo Guha, SVP of Product at Stellar Cyber.
“We are eliminating repetitive work so analysts can focus on high-value decisions. Cleaner signals, faster investigations, and automated workflows allow security teams to scale operations without scaling headcount.”
Stellar Cyber will demonstrate how AI improves SOC productivity without removing human oversight at RSAC 2026, Booth 327.