BitDefender impersonated by rogue antivirus
BitDefender has detected a new rogue antivirus utility that attempts to trick users into installing it by posing as a BitDefender product. Suggestively named ByteDefender, the malicious application acts like a fully-fledged rogue antivirus with a twist.
Unlike average rogue AV products, the ByteDefender sibling does not rely on the classic drive-by method used by most products of its kind, but rather piggybacks on the popularity of the BitDefender products and their distinct visual identity to lure users into voluntarily downloading it. The website distributing it is located at hxxp://www.bytedefender.in (URL specifically invalidated to avoid accidental infection) and abusively built using the BitDefender layout. The domain name has been registered in Ukraine. Even the boxshots have been crafted in such a manner to trick the user into thinking that they are installing the genuine security product.

The infection scenario is simple, yet efficient: the user looking for a BitDefender product may typo-squat the genuine address and gets redirected to the malicious webpage. Because of the similar webpage structure, the user may download and install the rogue AV.
Once installed on the system, this piece of scareware would start popping out fake infection alerts in an attempt at pursuing the user into purchasing the “full version” and get rid of the mentioned threats.

Figure 1: “infections found” during the scan process

Figure 2: “Infection” report
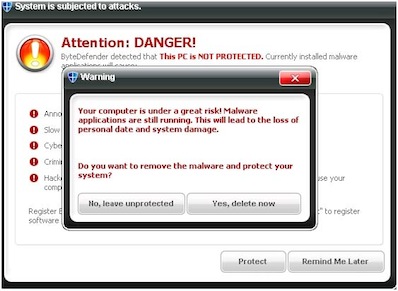
Figure 3: Buy now
Interesting enough, the payment processor for the ByteDefender Rogue AV is the trustworthy company Plimus, who has suspended sales on grounds of abuse.
“Cyber-criminals know no boundaries when it comes to distributing and marketing their rogue security products. Sensational events, Trojanized applications or websites and carefully forged – yet useless – “security products’ are only a few of the multitude of methods to capitalize on unwary users”, said Catalin Cosoi, senior Researcher at BitDefender.
As for the technical part, the ByteDefender rogue AV is shielded by a modified UPX packer with multiple layers of obfuscation that not only that deters static analysis, but also prevents it from running inside a virtual machine. It unsuccessfully tries to kill Windows services known to belong to specific AV vendors, thus opening a door for its own files.

Author: Bogdan Botezatu, BitDefender.
