Trojan spyware promoted as Steam keygen
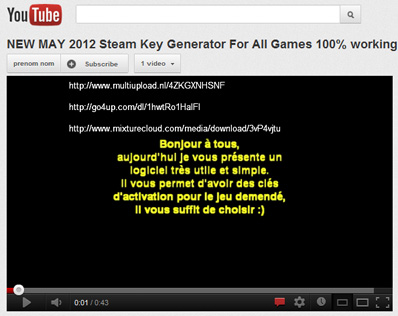
Scouring the Web for “legitimate” key generators, or keygens, is a risky business at the best of times. We make it a point that whoever the source is must have irrefutable proof that their keygen among other keygens like it is the real deal. And what better place to look for irrefutable proof than on YouTube, right?
Or maybe not.
To users looking for keygens for their Steam games, read on: we found something that will make you think twice and probably leave you steering clear of key generators forever.
Here’s the tip off. Visiting any of the three website addresses flashed on the above YouTube clip (Note: still live) leads to public portals where the purported keygen, steam Game Key Generator.exe, can be downloaded.
![]()
After running the file, users will not see any visible activities on their desktops. In the background, however, steam Game Key Generator.exe installs 7.0.1428.crx, a Google Chrome extension file found to be a Trojan spyware, that is hosted on theonlyone(dot)goodluckwith(dot)us. This .CRX file is then installed onto Chrome upon user consent.
For those who aren’t familiar with Chrome extensions, these are “zipped bundle of files—HTML, CSS, JavaScript (JS), images, and anything else you need—that adds functionality to the Google Chrome browser”, and they can be viewed in Tools > Extensions.
This particular extension disguises itself as the legitimate browser plugin, avast! WebRep, a website rating tool of security software company, AVAST Software. The individual or group behind the said plugin used such an approach to hide the file’s malicious activities from unsuspecting users.

Below are our technical findings regarding this Trojan spyware:
This fake plugin executes two JS files contained in itself: webProtection.js and background, js.
Using webProtection.js, it looks out for the following strings, which are notably related to online games/gaming and email accounts, in domains the user is currently visiting:
- accounts.google
- darkorbit
- dofus
- gameforge
- login.live
- metin2
- minecraft.net
- remboursetonforfait
- steamcommunity
- steampowered.
It does this in order to listen for “submit” or “click” events being done by users so it can log their user names, passwords, and complete URL of domains they are in.
It closely monitors the gameforge and google strings, as it is found to save the domain and log-out pages of websites containing such strings into a cookie.
Using background, js, it then sends this cookie to theonlyone(dot)goodluckwith(dot)us/request(dot)php?, including information on Chrome browser versions users are running. To save and retrieve information to and from cookies, this spyware uses the non-existent site, hochgmaoldgcdkfolpcifkifhpibhmmh(dot)com.
This fake plugin is set to get updates from theonlyone(dot)goodluckwith(dot)us/update.xml.
We are fortunate enough to also retrieve the updated version of this .CRX file, which is version 7.0.1429. On top of routines I have listed above, this has the following new ones:
- It monitors YouTube connections using the string youtu.
- If a connection is detected, it “auto-likes” the specific videos with the following IDs: Uj_FeciQWcg, xrnJe5FyEek, cjv-jYuuSp4.
It is important to note that the individual or group appears to have created a number of YouTube profiles just to further proliferate the bogus keygen. As of this writing, these clips have hundreds of clip views and likes. I dread to think that the higher these numbers go, the more users will likely believe that this keygen is authentic.

Author: Jovi Umawing, Communications and Research Analyst in the GFI Security Labs in the Philippines.