New infosec products of the week: May 25, 2018
Prioritizing open source security alerts
WhiteSource launched its next-generation Software Composition Analysis solutions – Effective Usage Analysis. The technology provides details beyond simply which components are present in the application, delving deeper with actionable insights on how components are being used, highlighting their impact on the security of the application.

Passwork introduces new password manager
Passwork.me is a new password manager designed to enhance security when working with corporate passwords. Through this password manager, the company can safely store all their passwords and employees can search the right passwords quickly. The administrator controls all the user rights as well as keeps track of any changes or actions taken by the members.

High-reliability packet capture in enterprise networks
DAG Cards natively support a wide range of open source applications including Wireshark, Bro, SNORT, Suricata, and any libpcap application through DAG-enabled libraries. Both the 9.5G4 and 9.5G4F feature standard DAG Card functionality such as interrupt free, zero copy, packet capture direct-to-memory and onboard, hardware-based, filtering, duplication and steering. They also provide on-board processing for a host of enterprise and encapsulation protocols, such as MPLS and VLAN for load balancing, classification and filtering.

Automated threat detection & investigation app for the Palo Alto Networks Application Framework
SecBI unveiled its Autonomous Investigation app for the Palo Alto Networks Application Framework. SecBI’s Autonomous Investigation technology uses network traffic analysis (NTA) based on unsupervised machine learning to detect complex and stealthy cybersecurity threats. Security analysts are presented with the full scope of the suspicious incident’s kill chain, including visibility to all affected users and devices, as well as infection points and malicious communications, enabling fast and complete remediation.

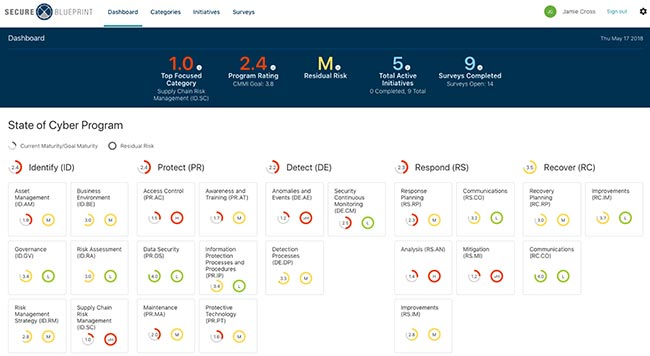
Measure a cyber program’s maturity and residual risk
Kudelski Security announced the U.S. availability of Secure Blueprint. This product provides a centralized system for program management as well as easy-to-use dashboards that deliver a dynamic representation of cyber program maturity, enterprise risks and other information about which CISOs need to engage key stakeholders, allowing them to plan and prioritize cybersecurity investments.
Cognito Recall delivers AI-assisted threat hunting
Vectra announced a major expansion of the Cognito platform with Cognito Recall. It collects, analyzes and stores as much metadata as needed for forensic investigations and compliance mandates like GDPR. It also empowers AI-assisted threat hunting using indicators of compromise and provides a chain of forensic evidence behind every cyberattack.

Exponential‐e launches Cyber Security Operations Centre
Exponential‐e launched its Cyber Security Operations Centre (CSOC), capable of monitoring for compliance to multiple standards, from best practice through to PCI-DSS and ISO 27001. The very nature of this type of monitoring lifts a heavy burden when adhering to regulations such as GDPR.

Cato unveils SD-WAN with cloud-based threat hunting system
The Cato Threat Hunting System leverages traffic context, unobscured network and endpoint visibility to pinpoint threats and reduce dwell time. It represents the first time that threat hunting is done without deploying a dedicated and costly data collection infrastructure within the enterprise.
