Product showcase: Cynet 360 Security Platform
Resource-constrained companies that want to protect their internal environments from cyberattack face an impossible challenge: they need to spend a lot of money to buy multiple point solutions to complement their firewall and antivirus. Of course, this means breaking budgets as well as hiring staff that doesn’t exist. In reality, most of them eventually stay without an effective cyber defense.
Cynet addresses this challenge that most organizations face, by consolidates network and endpoint protection in one place. They built the platform to be simple and easy to deploy and use; provide broad visibility across the network, endpoints, files and users; protect against a very wide range of attacks including common attacks as well as complex multi-layered attacks; and provide a team of security experts available 24/7 that complements whatever expertise you have in place.
Cynet supports four deployment methods: On-premise, IAAS, SAAS and hybrid mode. Using a unique technology, deployment of Cynet takes a few minutes across any number of endpoints.
Key features
Cynet’s features are broad and comprehensive. Cynet unifies a number of disparate capabilities into a single platform. These capabilities cover visibility, prevention, detection and response:
- IT hygiene: Cynet quickly maps the entire IT infrastructure by scanning assets including endpoints, users, files and network traffic to render a dashboard of security issues uncovered.
- Prevention: The platform leverages various prevention capabilities including UBA, deception and traditional endpoint protection.
- Detection: Cynet’s detection suite includes traditional endpoint security, EDR, UBA, deception and network analytics. This integrated approach helps to spotlight malicious behavior, exploitation, ransomware, lateral movement, brute force, user login anomalies, DNS Tunneling, privilege escalation, credential theft and more.
- Response: Cynet includes various analysis, response and remediation capabilities, across endpoints, files, users and networks.
- Automated response: For each alert Cynet creates, users can create an automatic remediation rule, to improve the incident response process and the prevention of a real-time threat.
- Vulnerability management: Cynet will sniff out Windows vulnerabilities, unauthorized and outdated applications and security policy violations.
- 24/7 Complementary support: Cynet includes CyOps – a 24/7 operations team – at no additional cost.
IT hygiene (visibility)
Cynet starts by mapping the entire IT infrastructure by scanning assets including endpoints, users, files and network traffic to render a dashboard of security issues uncovered and a full endpoint manifest.
Dashboard with security health check
Then, Cynet integrates an organization’s network with the endpoint analysis while showing risky areas with hyper links for a deeper look at each endpoint:

Network map
Prevention
Cynet’s approach to prevention starts with configuration: you set up the system stop the threats you need to automatically prevent:
Prevention configuration
Cynet also enhances endpoint protection with whitelisting. Cynet protects vital components of the operating system by allowing access only to approved files, processes and communications.
Detection
Cynet brings together detection, correlation and automation with its analysis across endpoints, for users, files and networks. Cynet’s detection suite includes traditional endpoint security, EDR, UBA, deception and network analytics. This pre-integrated approach helps to spotlight malicious behavior, ransomware, lateral movement, brute force, user login anomalies, DNS Tunneling, privilege escalation, credential theft and more.
Cynet puts alerts into a prioritized, single view delineating actionable information:
Alerts screen
For each alert you can dive expend the view for additional information.
Single alert
Response
In cases of attacks which are not prevented, or which require further analysis, Cynet has various analysis remediation actions available that are either automatic or pull people where needed.
From an automated perspective, you can send files into a sandbox, pull and verify if files were deleted as well as check for in memory attacks. If these operations aren’t sufficient, Cynet allows you to send to their SOC for further review. In addition, once identified, Cynet provides advanced and comprehensive response capabilities for the hosts, users, files or networks including killing or quarantining malicious files, disabling users and run commands, shutting down process or restart hosts or blocking traffic.

Response menu
Automated remediation
For each alert Cynet creates, the user can create and customize his own automatic remediation rule, to improve the incident response process and the prevention of a real-time threat.
As part of this, Cynet provides a comprehensive rule creation mechanism that allows the user to customize the action according to the organization’s needs, such as: which group to apply the rule to, whom to exclude, etc.

Automatic remediation menu
Vulnerability management
Cynet will sniff out Windows vulnerabilities, unauthorized and outdated applications and security policy violations. Cynet first exposesunauthorized applications such as BitTorrent, BitHit and so on.
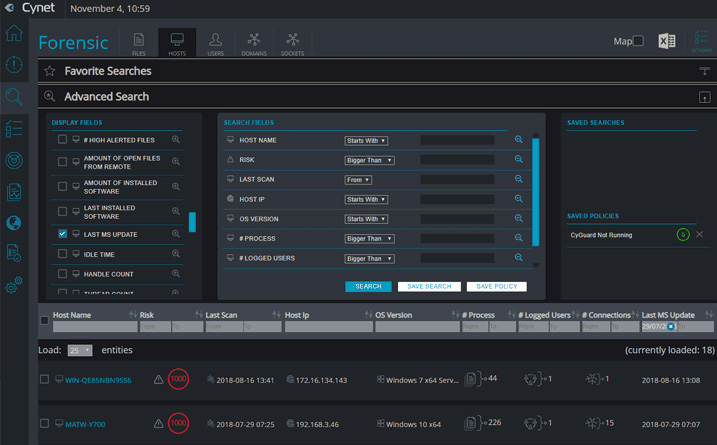
Cynet’s Forensics feature allows users to search across files, hosts, users and sockets. Every object is clickable to easily understand its history. For example, you can search for common security issues such as users that have not replaced a password, what files are called upon startup, what applications are running on your endpoints and look for unauthorized access to applications using network visibility.
Hosts not updated over a specific period of time
Complementary 24/7 cyber SWAT team
Cynet includes CyOps – a 24/7 operations team – at no additional cost. This proactive and comprehensive service is designed to fill the gaps in expertise customers lack. In the event of something requiring your attention – an urgent alert, forensics, attack – Cynet staff will get on the phone or email you. Their service covers also:
- Forensics
- Malware analysis
- Threat hunting
A free trial of Cynet 360 is available for 14 days. You can deploy Cynet on one endpoint or all endpoints in your network within minutes.