Product showcase: Cynet 360, 2020 Fall Platform Update
We are in dire need of approaches that simplify and consolidate the cybersecurity toolset so that companies can afford the coverage required and to make effective breach protection accessible to those other than world-class experts.
Cynet was formed specifically to consolidate multiple threat prevention and detection controls into a single offering for two primary reasons. First, keeping all the controls on a single platform allows for far better results than integrating and managing technologies from multiple providers. Second, it greatly simplifies the technology stack (not to mention affordability improvements). Then, Cynet goes beyond these benefits by automating many of the common workflows required to respond to cyber threats that would otherwise require high level skills, time and effort.
The Cynet 360 platform is built on three pillars: Extended Detection and Response (XDR), Response Automation and Managed Detection and Response (MDR). These three components together provide what Cynet calls Autonomous Breach Protection – essentially breach protection on autopilot. Let’s look at each of these components.
XDR
While XDR is considered a new technology – it’s something Cynet has been doing since its inception. XDR technology essentially combines signals from multiple control points as part of a single platform to provide better results than when deploying multiple siloed controls and then trying to figure out the stream of alerts and data from each. Many analyst firms are touting XDR as “the next big thing in cybersecurity.”
The Cynet XDR combines prevention, detection and data from:
- Endpoint protection – Next-Generation AntiVirus (NGAV) for basic endpoint malware prevention and detection and Endpoint Detection and Response (EDR) for more advanced endpoint protection, detection and response
- Network Traffic Analysis (NTA) for identifying malicious activity on your network
- Entity and User Behavior Monitoring (EUBA) to detect anomalous user behavior
- Deception technology to trick successful intruders into exposing their presence before damage can be done
Response automation
Cynet automates many tasks associated with threat detection response and cross-environment remediation including infected hosts, compromised user accounts, malicious processes and attacker-controlled network traffic.
Many solutions can detect threats and then automatically prevent them from executing and causing damage. This is wonderful and helpful, but only represents the first step in addressing a threat. We must assume that the threat discovered is likely only the tip of the iceberg and is likely only a piece of a larger, coordinated attack. This is where the cybersecurity skill gap becomes dangerous.
The Cynet Incident Engine triggers an automated investigation following certain high-risk alerts, fully disclosing its root cause and scope and applying all the required remediation activities. This is offered on a single platform, out of the box, ready to bring your cybersecurity to the next level on day one. This, my friends, is the most amazing and useful cybersecurity breakthrough I’ve seen in some time.
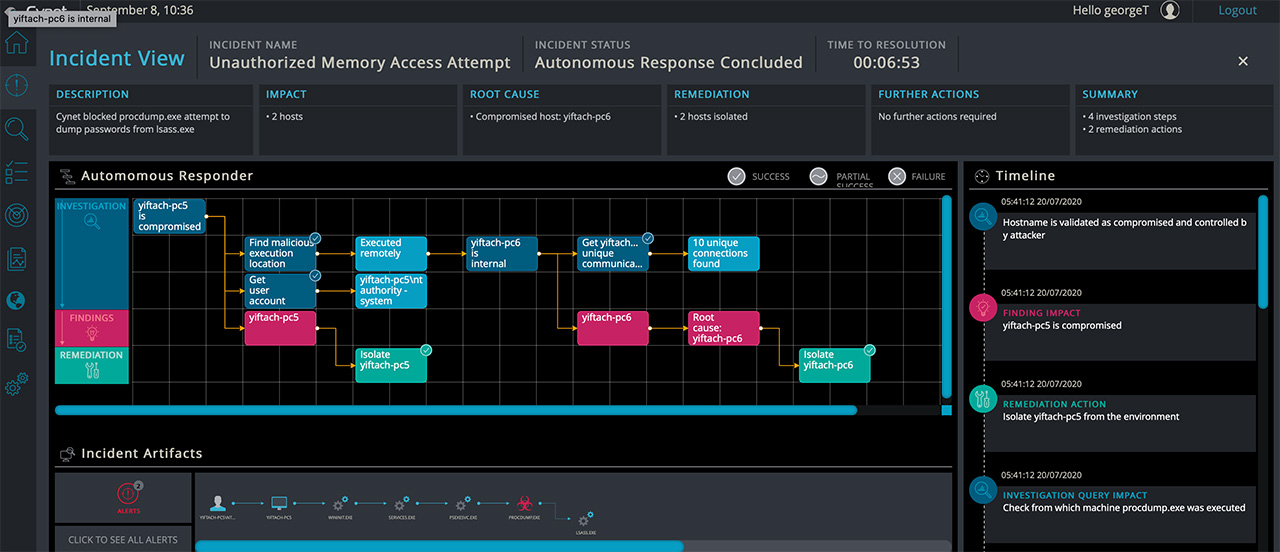
On certain high-risk alerts, customers can click the Incident View button:
This leads to a page that displays the full set of investigation steps and remediation actions that the Incident Engine performed as soon as the threat was detected.
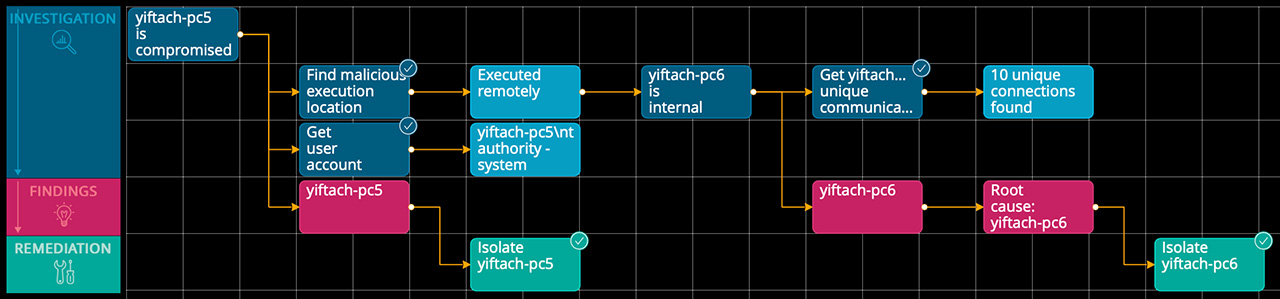
As shown in the screenshot below, a simple workflow diagram shows the series of investigation queries and results (blue) that lead to findings (red) that are addressed with remediation (green). The Timeline on the right shows a more detailed description of every step, while the Incident Artifacts displays the attack flow. The full incident is summarized in the upper text boxes.
In the following example, we see an Unauthorized Memory Access Attempt alert that was triggered by an attempt to dump credentials – a common attack scenario. The initial alert indicates that Cynet neutralized the attempt and that the credentials were not accessed. The Incident Engine then does its thing – it isolates the compromised host against from which the attack was launched and reveals a lateral movement. It turns out that the attack was actually launched remotely from another host in the environment, which is the true root cause. This finding is concluded by isolating the root cause host as well.
This off-the-shelf automated root cause analysis, impact investigation and remediation actions took Cynet’s platform just under seven minutes to fully perform, all in the background, saving literally hours of analyst effort. Or, it performed a series of tasks to find and remediate threats that some organizations would not have known were necessary or how to do them.
MDR – CyOps
Cynet calls their MDR team of cybersecurity experts CyOps and includes 24×7 monitoring for all clients to ensure any real attacks are not overlooked. They also provide ad-hoc threat investigations and forensic analysis and guide their clients through any necessary remediation steps. CyOps is automatically included in the Cynet platform – at no additional cost.
This type of service is typically quite expensive and oftentimes only available from third party providers. With CyOps intimate understanding of the Cynet platform, they can provide far superior service than MDR teams that some vendors contract with to support their platform.