ThreatNG Cloud and SaaS Exposure Module empowers users with a proactive outside-in perspective
ThreatNG announced its agentless Cloud and SaaS Exposure Module as a part of its External Attack Surface Management (EASM) and Digital Risk solution.
The ThreatNG “Cloud and SaaS Exposure” Module supports the following vendors and technology categories:
- Amazon Web Services (AWS)
- Microsoft Azure
- Google Cloud Platform (GCP)
- Analytics
- Business intelligence (BI)
- Customer relationship management (CRM)
- File sharing
- Human resources
- Security
- Video telephony
Requiring only a domain and organization name, ThreatNG users can perform outside-in discovery, assessment, reporting, and monitoring of their Cloud and SaaS footprint, uncover exposed open cloud buckets, bring to light unsanctioned implementations (Shadow IT), and call to attention brand impersonations (Cybersquats) without using agents, credentials, API connections, browser plugins, and any other means that require prior knowledge.
ThreatNG further empowers its users by providing a holistic approach by extending discovery and assessment of all Internet-exposed online applications, repositories, APIs, platform-as-a-service (PaaS), infrastructure-as-a-service (IaaS), and vendor technologies interconnected with Cloud and SaaS implementations.
“As more critical data and functions are migrating to the cloud, it becomes much more important for organizations to have visibility of all their digital assets exposed to the public and address all potential risks and threats. Our Cloud and SaaS Exposure module empower users with a proactive outside-in perspective,” said Eric Gonzales, founder of ThreatNG. “We are so confident in our technology’s capability that we are willing to provide organizations of all sizes with a free discovery and risk assessment of their Cloud and SaaS environments.”
Cloud and SaaS environments are continuously evolving. With new instances appearing, this constant change makes it challenging to keep an accurate inventory of sanctioned implementations and maintain good cyber hygiene overall. This growing cloud and SaaS sprawl feeds into the ever-increasing problem of Shadow IT (unsanctioned implementations) and Cybersquats (brand impersonations).
This uncontrollable sprawl has also led to increased security risks and exposures, a growth in phishing attacks abusing SaaS platforms, and cloud assets compromised more than on-premise assets (Verizon 2022 Data Breach Investigations Report).
Cloud and SaaS impersonations (Cybersquats) and exposed data within open cloud buckets are growing problems with organizations of all sizes and their third parties. Still, they are out of scope within most External Attack Surface Management (EASM), digital risk protection, and security rating services.
ThreatNG unites these solution capabilities and empowers users to seamlessly bring cloud and SaaS into the fold of asset inventory, security & governance, subsidiary security monitoring, third-party security assessments, and brand protection through their innovative external discovery and assessment requiring only a domain and organization name.
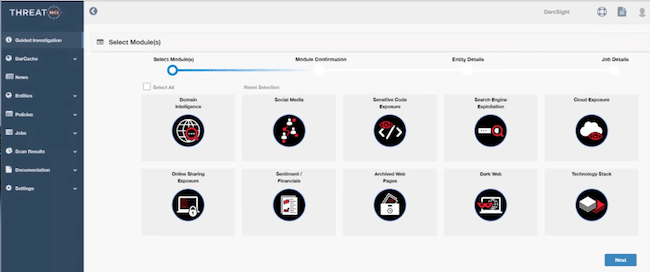
Support for all of the above is available now and accompanied by all of the following investigation modules provided to all ThreatNG users:
- Domain intelligence
- Technology stack
- Sensitive code exposure
- Online sharing exposure
- Search engine exploitation
- Sentiment and financials
- Archived web pages
- Social media
- Dark web