Attackers exploited another Gladinet Triofox vulnerability (CVE-2025-12480)
Attackers have exploited yet another vulnerability (CVE-2025-12480) in the Gladinet Triofox secure file sharing and remote access platform, Mandiant revealed on Monday.
CVE-2025-12480 exploitation and attack details
Gladinet’s Triofox solution is used by medium and large businesses to securely share files and allow users to access them without a VPN.
CVE-2025-12480 is an Improper Access Control flaw allowing unauthenticated attackers to access the solution’s configuration/setup page.
According to Mandiant’s threat analysts, as early as August 24, 2025, a threat cluster they track as UNC6485 exploited CVE-2025-12480 by conducting an HTTP Host header attack.
They set the Host value to localhost, which allowed them to bypass access controls on the configuration page, and used the page to run the initial Triofox setup process to create a new native administration account (“Cluster Admin”).
This account was then used to upload malicious files and execute them by leveraging the built-in antivirus feature.
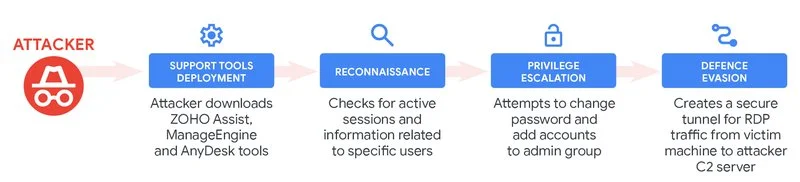
“The executed payload was a legitimate copy of the Zoho Unified Endpoint Management System (UEMS) software installer. The attacker used the UEMS agent to then deploy the Zoho Assist and Anydesk remote access utilities on the host,” the threat analysts explained.
“The attacker used Zoho Assist to run various commands to enumerate active SMB sessions and specific local and domain user information. Additionally, they attempted to change passwords for existing accounts and add the accounts to the local administrators and the ‘Domain Admins’ group.”
The attackers’ post-exploitation activity (Source: Mandiant/Google Cloud)
Attackers are having a field day with Gladinet zero-day and n-day vulnerabilities
The attackers exploited CVE-2025-12480 on a server running Triofox v16.4.10317.56372, which was released in April 2025 to fix CVE-2025-30406, a deserialization vulnerability affecting Triofox and Gladinet’s MSP-friendly file sharing platform CentreStack.
According to its NVD entry, CVE-2025-30406 was exploited as a zero-day beginning in March 2025. By April, Huntress had identified multiple successful attacks, and noted that similarities in the attackers’ tradecraft suggested the same group was also behind the exploitation of a CrushFTP vulnerability (CVE-2025-31161) around the same period.
In October 2025, Huntress researchers raised the alarm once again: an unauthenticated Local File Inclusion zero-day vulnerability (CVE-2025-11371) in Gladinet CentreStack and Triofox was being exploited by attackers in the wild. The vulnerability was fixed in CentreStack and Triofox v16.10.10408.56683, released on October 14.
Organizations using either of the two solution are advised to upgrade to the latest available release.
Mandiant’s threat analysts also recommend:
- Auditing admin accounts
- Verifying that Triofox’s Anti-virus Engine is not configured to execute unauthorized scripts or binaries
- Checking for the presence of attacker tools and indicators of compromise (which they shared)
- Monitoring for anomalous outbound SSH traffic.
UPDATE (November 12, 2025, 08:05 a.m. ET):
The headline and the text of this article has been amended to clear up that CVE-2025-12480 had already been patched (in Triofox v16.7.10368.56560, released on July 26, 2025) when Mandiant’s incident responders spotted it being leveraged by attackers.
CVE-2025-12480 was, therefore, not a zero-day vulnerability at the time (as initially stated by Help Net Security).
In related news, Rapid7 researchers have also analyzed CVE-2025-12480 in the context of Gladinet’s CentreStack solution, and found that it was also affected and received a patch in v16.7.10368.56560.
“In addition to demonstrating the vulnerability against CentreStack, our analysis also shows an alternative exploitation strategy to achieve RCE, compared to the exploitation strategy detailed in the Mandiant report,” they said.
“The exploitation strategy detailed in this analysis is premised on the access control bypass vulnerability CVE-2025-12480, that leads to administrator account takeover. From there an attacker can reconfigure the servers local storage and perform an arbitrary file read, leaking the unique cryptographic keys used to sign .NET ViewState payloads. After leaking the cryptographic keys, the attacker can achieve arbitrary code execution via .NET deserialization.”

Subscribe to our breaking news e-mail alert to never miss out on the latest breaches, vulnerabilities and cybersecurity threats. Subscribe here!