Push Security adds malicious browser extension detection to block threats in employee browsers
Push Security has announced new malicious browser extension detection and blocking capabilities within its browser-based security platform. The feature enables organizations to automatically block known-bad extensions from running in employee browsers.
Attackers are increasingly turning to malicious browser extensions as a preferred method of compromise. Recent campaigns such as ShadyPanda, ZoomStealer, and GhostPoster, along with breaches impacting vendors including Cyberhaven and Trust Wallet, highlight the growing risk posed by compromised extensions.
“Browser extensions represent one of the most under-monitored attack vectors in modern enterprises,” said Jacques Louw, chief product officer at Push Security. “For modern organizations running different operating systems and browsers across their workforce, it’s hard to know what’s running, let alone what is malicious.”
A growing and miscalculated threat
Nearly every major app now has a browser extension counterpart, alongside thousands of AI overlays, screen recorders, spell checkers, and design tools. The Chrome Web Store alone hosts more than 100,000 extensions, making it clear that this is an expanding attack surface that many organizations do not fully understand.
“Compounding the issue, most malicious extensions do not begin as malicious,” said Louw. “Attackers frequently create initially benign extensions and later push malicious updates, or take over existing extensions with large install bases, by hacking extension devs, or simply by purchasing the extension legitimately. Once a malicious update is deployed, every browser running the extension can be compromised when their browser next updates.”
“Simply blocking extensions altogether is unrealistic for most organizations,” he continued. “Security teams need visibility and enforcement without disrupting productivity.”
Extension code is routinely analyzed as part of the extension upload and approval process; however, attackers routinely evade detection using obfuscated and dynamically compiled code. Extensions are often flagged only after malicious activity is observed in the wild and, more frequently, after a breach has occurred. Even when removed from the store, extensions may remain active in user browsers, underlining the importance of being able to detect and block extensions independently of the web store.
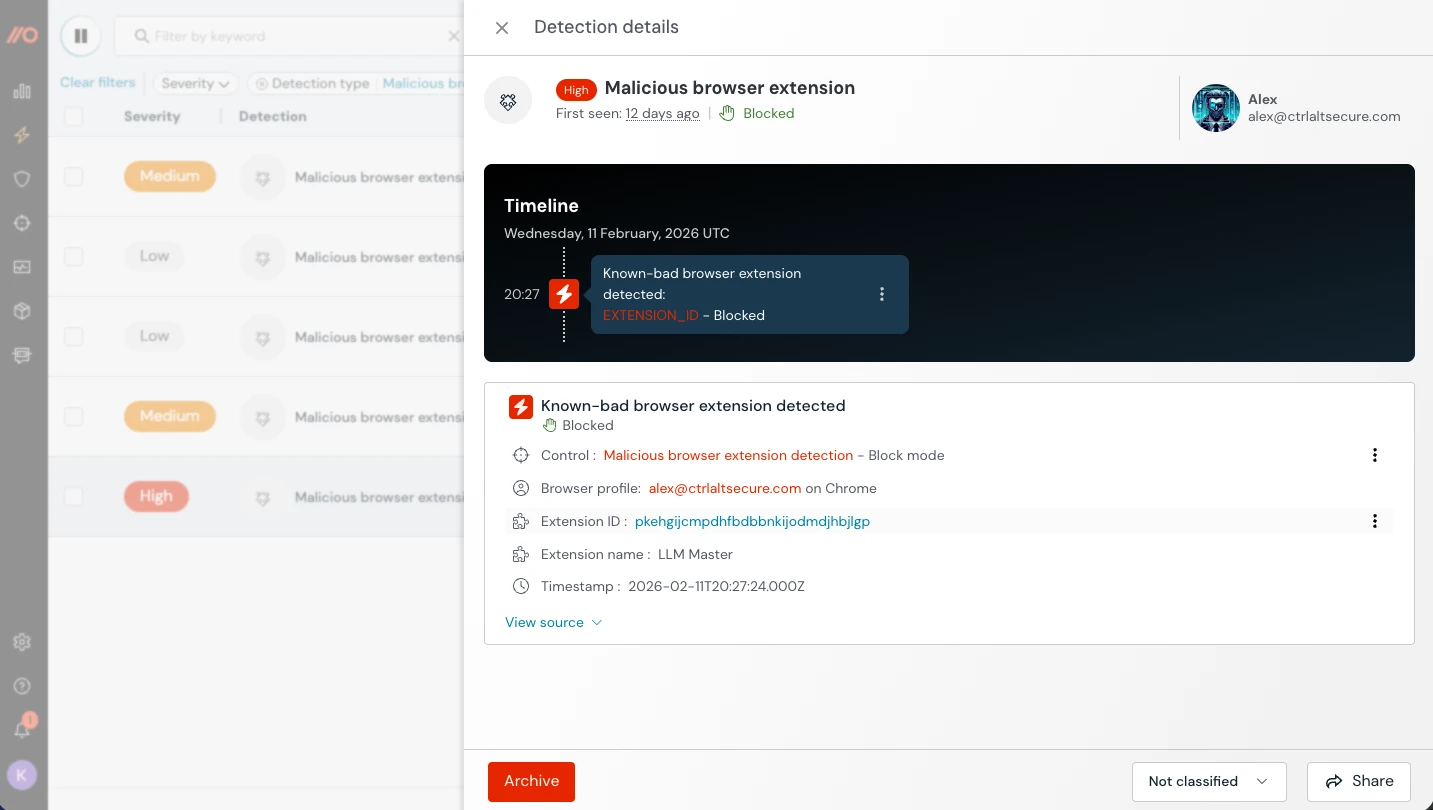
Push’s new capability enables organizations to automatically block known malicious extensions from running in employee browsers, derived from Push’s continuously updated intelligence database of reported malicious extensions. Customers can enforce policies in monitor or block mode via the Push admin console. When a malicious extension is detected, the platform generates severity-based alerts and can automatically disable the extension in affected browsers.
Beyond blocking known-bad extensions, Push provides real-time visibility into all extensions running across an organization’s workforce, including metadata such as publisher history, permissions, deployment method, and update activity. This enables security teams to seamlessly manage extensions across browsers and operating systems from a single platform, identify risky extensions, implement allowlists or blocklists, and monitor for suspicious changes such as changes in ownership or permissions.
The new feature expands Push’s browser-based security platform, which also protects against adversary-in-the-middle (AiTM) phishing, credential stuffing, session hijacking, and other browser-native attack techniques.