HR, recruiters targeted in year-long malware campaign
An attack campaign targeting HR departments and job recruiters has been stealthily compromising systems, Aryaka researchers have discovered.
By avoiding analysis environments and leveraging a specialized module designed to kill antivirus and endpoint detection software, the Russian-speaking attacker(s) behind this campaign have managed to keep their activity largely under the radar.
“We currently lack telemetry to determine how widespread the campaign is,” Aditya K. Sood, Aryaka’s VP of Security Engineering & AI Strategy, told Help Net Security.
“However, available artifacts indicate that the activity has likely been running silently for over a year, which may suggest a targeted and low-noise operation.”
Resume-themed ISO file starts the infection process
While the attack begins with a resume-themed ISO file delivered through recruitment channels, the initial infection vector remains unknown.
It is likely that the attachment links were distributed through spam emails, Sood told us, and the ISO file would be downloaded from Dropbox or a similar cloud storage service.
“Once mounted, the ISO appeared as a standard local drive, making its contents appear legitimate and encouraging the user to interact with the file,” Aryaka researchers explained in a report shared with Help Net Security.
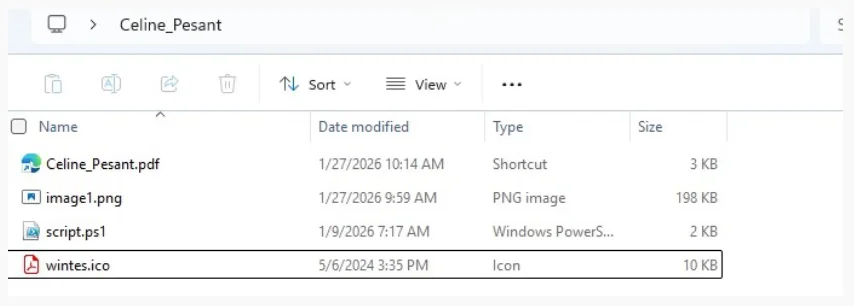
ISO file content (Source: Aryaka)
The PDF is actually a Windows shortcut (.lnk) file with a hidden extension and, if run, launches Windows Command Shell to then launch Powershell, which finally runs the script.ps1 file from within the mounted ISO.
The PowerShell script extracts hidden data from the image1.png file and uses it to “create” and execute another PS script in memory. That script downloads a file named SumatraPDF.zip from the attackers’ domains (such as “resumebuilders.us” and “thresumebuilder.com”) and extracts it into a temporary directory.
Within this archive are two files: SumatraPDF.exe and DWrite.dll. The former loads the latter via DLL sideloading, and the PS script attempts to launch the executable by using multiple execution methods.
Stealth above all
The malicious DWrite.dll starts collecting basic system information and initiates communication with the C2 server, which tells it to start a number of checks looking for evidence of virtual machines, debuggers, sandbox environments, analysis tools, and emulated systems running on the machine. If evidence of any of these are found, it will terminate the execution.
It will also terminate if it detects that the target machine is located in Russia or a CIS country.
“To further reduce defensive visibility, Windows Defender SpyNet policy registry keys are modified to disable cloud protection and automatic sample submission,” the researchers explained.
“In addition, the HypervisorEnforcedCodeIntegrity registry value is queried to determine whether Memory Integrity is enabled, which may influence later components that rely on driver-related functionality.”
Additional actions are triggered to mask the “noise” made by the execution of this payload.
Finally, after additional payloads/modules are downloaded from the C2 server, they are launched using process hollowing.
A new EDR killer
The researchers managed to identify additional infrastructure linked to this threat actor, which revealed that they also use the DWrite.dll to download a previously undocumented BlackSanta EDR killer.
BlackSanta loads vulnerable kernel-mode drivers like RogueKiller Antirootkit (v3.1.0) and IObitUnlocker.sys (v1.2.0.1), which allow it to access and tamper with the system memory and processes.
“Rather than functioning as a simple auxiliary payload, BlackSanta acts as a dedicated defense-neutralization module that programmatically identifies and interferes with protection and monitoring processes prior to the deployment of follow-on stages. By targeting endpoint security engines alongside telemetry and logging agents, it directly reduces alert generation, limits behavioral logging, and weakens investigative visibility on compromised hosts,” the researchers found.
They could not determine the exact malware ultimately delivered because the C2 server was unavailable; however, analysis of previous infections indicates that it likely deploys information-stealing modules.

Subscribe to our breaking news e-mail alert to never miss out on the latest breaches, vulnerabilities and cybersecurity threats. Subscribe here!