VulHunt: Open-source vulnerability detection framework
Binarly has published VulHunt Community Edition, making the core scanning engine from Binarly’s commercial Transparency Platform available to independent researchers and practitioners.
What VulHunt does
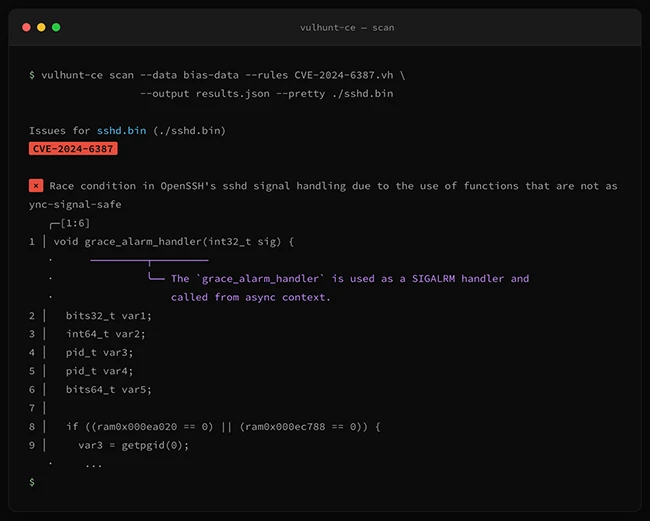
VulHunt Community Edition is a framework for detecting vulnerabilities in compiled software. It operates against multiple binary representations simultaneously, working across disassembly, an intermediate representation layer, and decompiled code. Targets include POSIX executables and UEFI firmware modules.
The detection logic is expressed in Lua rules. Each rule specifies metadata such as the author and rule name, filtering criteria like target platform and processor architecture, and a set of scopes that define what to look for in the binary. Scopes can operate at the project level, against individual functions, or against call sites. The documentation includes worked examples covering buffer overflows, authentication bypasses, and UEFI module vulnerabilities.
Rules run against binaries without requiring source code. The engine accepts single binary files, Binary Ninja databases, and BA2 archives, which are multi-component archive formats used within the Binarly toolchain.
The BIAS layer underneath
VulHunt sits on top of the Binary Analysis and Inspection System, internally called BIAS, which Binarly developed as the underlying analysis substrate. BIAS provides the analysis environment that VulHunt rules query against. The community edition ships the BIAS core as part of the open-source release, with the codebase split primarily between C++ and Rust.
What the Community Edition covers
VulHunt supports POSIX binary scanning, UEFI module scanning, a basic dataflow engine, function signature support, type library support, and module support. Supported architectures are x86, x86-64, ARM, and AArch64. It also includes integration with the Binarly Transparency Platform, allowing researchers to push rule sets, trigger scans, retrieve findings, and download BA2 archives from the same CLI.
Rules written by community contributors run on Enterprise deployments without modification, making community-developed rule packs directly portable to commercial environments.
MCP server and AI agent integration
VulHunt can operate as a Model Context Protocol server, exposing its analysis capabilities to AI assistants over a streaming HTTP connection with Server-Sent Events transport, or alternatively over stdio. This allows an LLM to call into the VulHunt engine during analysis sessions.
To support structured agent workflows, Binarly ships a set of Claude Skills alongside VulHunt. These are structured instruction files that teach an AI agent how to use VulHunt’s MCP tools for specific analysis tasks.
VulHunt Community Edition is available for free on GitHub.

Must read:
- 40 open-source tools redefining how security teams secure the stack
- Firmware scanning time, cost, and where teams run EMBA

Subscribe to the Help Net Security ad-free monthly newsletter to stay informed on the essential open-source cybersecurity tools. Subscribe here!
