Claude Code source leak exploited to spread malware
A source code leak involving Anthropic’s Claude Code tool quickly escalated into a cybersecurity threat, as attackers seized on the exposed files to lure developers into downloading malware disguised as “unlocked” versions of the software.
Leaked Claude Code source code used as lure
On March 31, 2026, Anthropic accidentally exposed online the source code of its Claude Code tool. The leak was detected by security researcher Chaofan Shou, whose post on X drew widespread attention.
The leaked map file contained about 513,000 lines of unobfuscated TypeScript in 1,906 files, revealing the client-side agent framework. Within hours, the code was downloaded, mirrored on GitHub, and redistributed, with some repositories gaining tens of thousands of stars and forks.
While monitoring GitHub for threats, Zscaler researchers identified a repository titled “Leaked Claude Code” published by a user named idbzoomh1.
Its README.md file claims the material was obtained from a .map file embedded in an npm package and then reconstructed into a functional fork, described as having “unlocked” Claude Code’s enterprise features and no message limits.
“The malicious ZIP archive in the repository’s releases section is named Claude Code – Leaked Source Code (.7z),” the researchers said.
“The archive includes ClaudeCode_x64.exe, a Rust-based dropper. On execution, the ClaudeCode_x64.exe drops Vidar v18.7 and GhostSocks. Vidar is an information stealer and GhostSocks is used to proxy network traffic.”
Before it was removed, the link to the malicious repository appeared near the top of Google search results for users looking for “leaked Claude Code”.
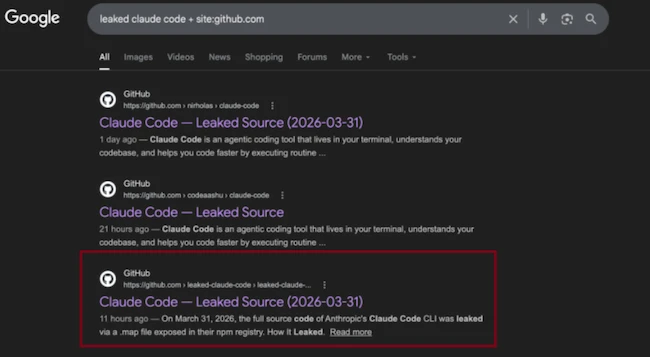
Google search results for leaked Claude Code on GitHub returning a malicious repository (Source: Zcaler)
During their analysis, Zscaler observed the threat actor uploading two separate versions of the malicious ZIP archive to the repository’s releases section within a short timeframe.
The same GitHub repository was also identified under a different account (my3jie), containing identical code and appearing to be linked to the same threat actor.
A hot tool makes for a good lure
The popularity of Claude Code makes it a good lure for scammers, malware peddlers, and other attackers.
Earlier this month, Push Security warned about fake/cloned Claude Code install pages that were pushing malware and were popping up in Google Search results.
After pointing out that leaked proprietary source code is not “open source”, the researchers advised users against downloading, forking, building, or running code from any GitHub repository claiming to be the “leaked Claude Code.”
“Verify every source against Anthropic’s official channels only,” they counseled, and shared indicators of compromise linked to this campaign.