cybercrime

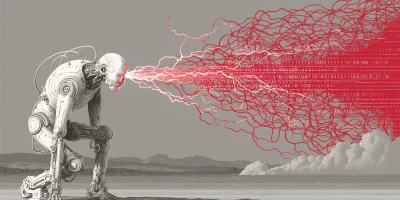
AI is helping low-skill hackers pull off advanced cyberattacks
Anthropic has published an analysis of cyber-related misuse of its AI systems, examining 832 accounts that were banned for malicious cyber activity between March 2025 and …

Malware campaign targeting Minecraft users infects over 116,000 systems
A Malware-as-a-Service (MaaS) operation named WeedHack is targeting Minecraft users and allows threat actors to gain remote access to victims’ screens, webcams, and …

64,000 accounts exposed in breach of GTA V cheat service Atlas Menu
Atlas Menu, a cheat service for Grand Theft Auto V and Counter-Strike 2, has been added to the Have I Been Pwned database following a data breach that exposed tens of …
Sophos uncovers AI-powered malware lab built for EDR evasion
A threat actor used AI technologies to build a malware-testing framework for developing and refining endpoint detection and response (EDR) evasion techniques, according to …

Sensitive government personnel data posted online, Spanish police arrest suspect
The Spanish National Police arrested a man in Granada for allegedly leaking personal data belonging to members of several sensitive state institutions. According to police, …

Cybercriminals sail away with data from 6 million Carnival customers
Carnival Corporation, one of the world’s largest cruise operators, confirmed a data breach weeks after the ShinyHunters hacking group claimed it had stolen millions of …

A single typo could derail your World Cup plans
Cybercriminals are spoofing Fédération Internationale de Football Association (FIFA) websites ahead of the 2026 FIFA World Cup, the FBI warns. The attackers are registering …

Oil shipments, drone makers, and a poisoned code library targeted in recent APT campaigns
Geopolitical pressure drove much of the state-sponsored cyber activity recorded between October 2025 and March 2026, according to ESET’s latest APT Activity Report. …

Police arrest suspect in Ajax football club hack that exposed 300,000 fan records
The Dutch National Police arrested a man suspected of hacking into the computer systems of AFC Ajax, a football club from Amsterdam. “On the morning of Tuesday, May 26, …

AI chatbot recommendations lure users to cryptojacking malware sites
Cybercriminals are using AI chatbot interactions alongside poisoned search results to direct users to malicious download sites in an active cryptojacking campaign, Microsoft …

Hackers are knocking on office doors pretending to be IT staff
The Silent Ransom Group (SRG) is targeting law firms using social engineering techniques and an unusual tactic for cybercriminals: showing up at victims’ offices in person …

Fake ChatGPT and Claude installers on GitHub are dropping Deno RAT malware
Attackers are hosting counterfeit installers and plugins on GitHub and SourceForge that pose as widely used software, including ChatGPT, Claude, AutoTune, Kontakt, Ableton …
Featured news
Resources
Don't miss
- Cisco SD-WAN 0-day exploited, no patch available (CVE-2026-20245)
- June 2026 Patch Tuesday forecast: Where are the CVEs?
- AgentGG: Open-source agentic SAST scanner
- Thieves can pull off keyless car theft in under a minute and here’s how to stop them
- OAuth marketplace apps keep access after publishers vanish