Attackers use MS Teams, fake mailbox repair utility to breach organizations
A threat group has penetrated corporate networks by impersonating IT helpdesk staff on Microsoft Teams, tricking employees into downloading malware and surrendering their credentials to a fake “Mailbox Repair Utility”.
The attack, from start to finish
UNC6692 is a newly identified threat group, documented by Google’s Threat Intelligence Group (GTIG) following a campaign that began in late December 2025.
The group started the attack attack by flooding targeted employees’ inboxes with spam emails, then reached out to them via Microsoft Teams while posing as an IT helpdesk employee offering to help.
From there, the social engineering only grew more elaborate. Victims were instructed to click a link to install a local patch to prevent email spamming.
“Once clicked, the user’s browser opened an HTML page and ultimately downloaded a renamed AutoHotKey binary and an AutoHotkey script, sharing the same name, from a threat actor-controlled AWS S3 bucket,” GTIG researchers explained.
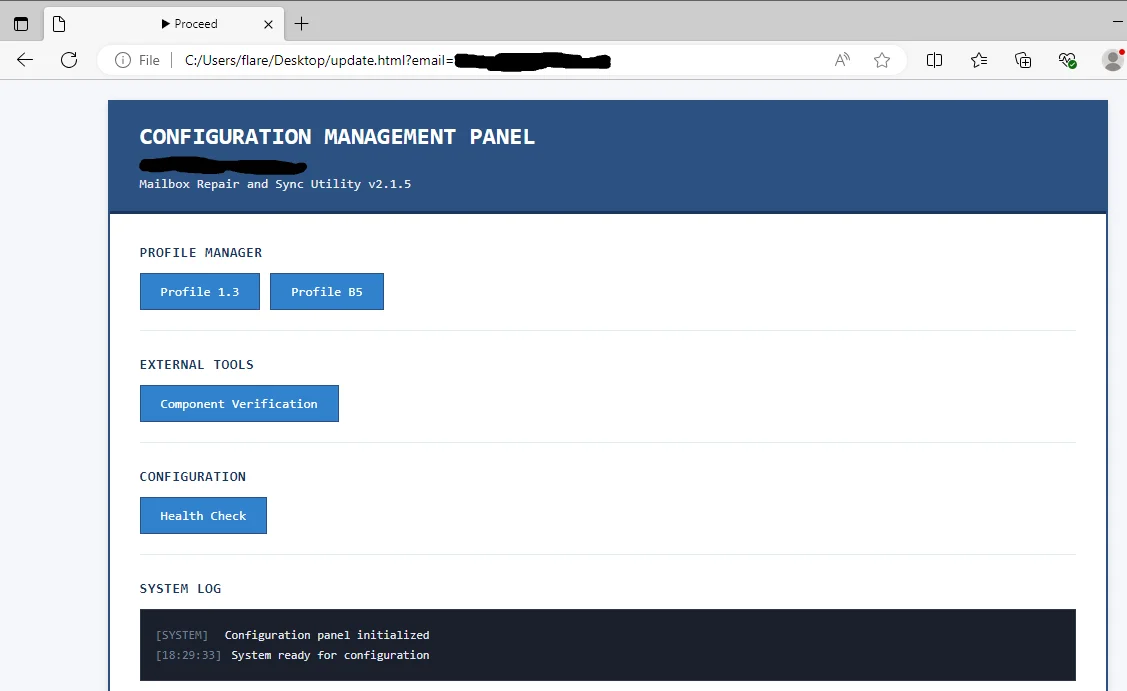
The HTML page masquerades as an official “Mailbox Repair and Sync Utility,” complete with professional-looking interface elements and a “Health Check” button that triggered a credential prompt.
The fake “Mailbox Repair and Sync Utility” (Source: GTIG)
Mimicking the behavior of a legitimate authentication system and reinforcing the victim’s belief that what they were interacting with was real, the page rejected the first two password attempts. After a third, “successful” attempt, the victim watched a progress bar tick through fake diagnostic tasks while their credentials were sent to an attacker-controlled server.
Simultaneously, the AutoHotKey binary covertly executes the AutoHotKey script, triggering the download of Snowbelt, a malicious Chromium browser extension/backdoor, which initiates a headless (i.e., invisible to the user) Microsoft Edge instance.
“Using the Snowbelt extension, UNC6692 downloaded additional files including Snowglaze [a Python tunneler that masks malicious traffic], Snowbasin [a Python bindshell that operates as a local HTTP server and is used for remote command execution and data staging], AutoHotkey scripts, and a ZIP archive containing a portable Python executable and required libraries,” the researchers noted.
Post-compromise, UNC6692:
- Enumerated local administrator accounts and used those credentials to pivot to a backup server
- Extracted the memory of a core Windows security process storing usernames, passwords, and authentication hashes, then exfiltrated the dump to be cracked offline
- Used the resulting password hashes to authenticate to the network’s domain controllers
- Deployed the FTK Imager tool to create forensic images of the Active Directory database and other sensitive credential stores, then exfiltrated those files from the network via Limewire.
A familiar playbook
Google’s researchers did not attribute the campaign to a known nation-state or criminal organization, but have noted that many other intrusions in recent years relied on the same social engineering trick for initial compromise: email bombing and IT helpdesk impersonation via Microsoft Teams.
They also pointed out the group’s use abuse of legitimate cloud services for payload delivery, C2 infrastructure, and data exfiltration.
“This ‘living off the cloud’ strategy allows attackers to blend malicious operations into a high volume of encrypted, reputably sourced traffic, making detection based on domain reputation or IP blocking increasingly ineffective,” they explained.
“As threat actors continue to professionalize these modular, cross-platform methodologies, the ability to correlate disparate events across the browser, local Python environments, and cloud egress points will be critical for early detection.”

Subscribe to our breaking news e-mail alert to never miss out on the latest breaches, vulnerabilities and cybersecurity threats. Subscribe here!