Android pushes new scam, theft, and AI protections in 2026 update wave
Phone scammers spoofing bank caller IDs have driven an estimated $980 million in annual losses worldwide, according to Europol. Android’s 2026 security roadmap takes direct aim at that pattern with a verified call system built in partnership with banks, alongside a wider set of protections covering app behavior, device theft, location data, and on-device AI processing.
Verified financial calls
A new feature called verified financial calls will check incoming calls against the official app of a participating bank or financial institution. When a call arrives that appears to come from the bank, Android queries the installed app to confirm whether a call is actually being placed. If the app reports no active call, the system ends the connection. Banks can also designate certain numbers as inbound-only, which means any outgoing call from those numbers gets terminated automatically.
“We’ll begin rolling this out on Android 11+ devices with Revolut, Itaú, and Nubank in the coming weeks, before expanding it to more banks later this year,” Eugene Liderman Director, Android Security & Privacy Team, explained.
Live Threat Detection and Chrome download checks
Live Threat Detection, Android’s on-device AI system for flagging suspicious app behavior, gains new warnings for SMS forwarding and accessibility overlay abuse. A capability called dynamic signal monitoring will watch application-system interactions in real time and push down updated detection rules to address new threats. It arrives on Android 17 devices, with protections shipping in the second half of 2026.
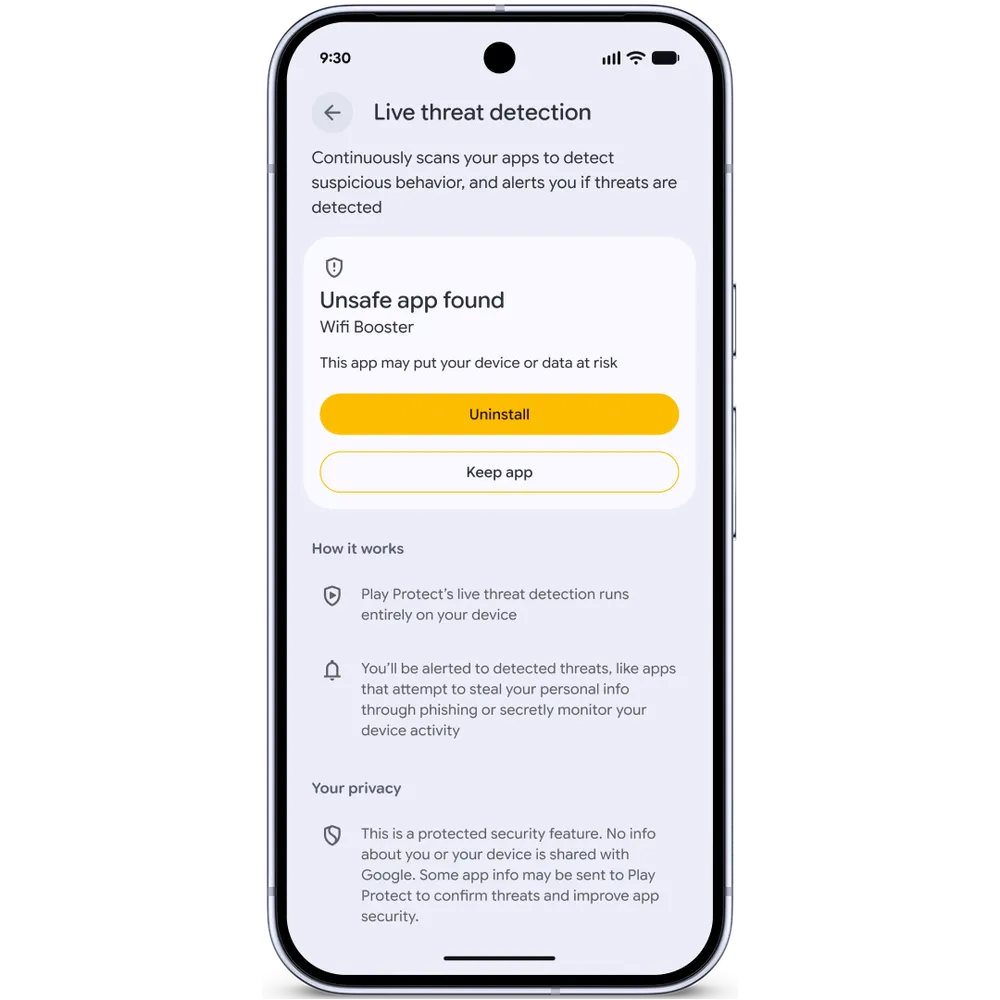
Live threat detection can notify you that an unsafe app was found (Source: Google)
Chrome on Android adds another download-time check. With Safe Browsing enabled, the browser will evaluate APK files for known malware and block downloads of harmful packages.
Advanced Protection, the one-toggle hardening mode introduced last year, picks up several additions. Android 17 removes accessibility service access from any app that is not labeled an accessibility tool, disables device-to-device unlocking and Chrome WebGPU support, and integrates scam detection for chat notifications.
USB protection is available on Pixel devices running Android 16 and later, and Intrusion Logging is rolling out to all devices on the Android 16 December update and newer. Android Enterprise support for Advanced Protection arrives later in the year.
Theft protection expanded
Find Hub’s Mark as lost feature in Android 17 will require biometric authentication to unlock a phone after it has been flagged, blocking thieves who may have observed the PIN. Marking a device as lost also hides Quick Settings and disables new Wi-Fi and Bluetooth pairings.
Following a Brazil pilot, default-on theft protections will be enabled on all new Android 17 devices and on phones reset or upgraded to the latest OS. In Argentina, Chile, Colombia, Mexico, and the UK, the protections extend to any device running Android 10 or higher, activating Remote Lock and Theft Detection Lock automatically.
Android 17 also reduces the number of allowed PIN guesses on supported devices and lengthens wait times between failed attempts. The IMEI can be accessed from the lock screen on Android 12 and later to help law enforcement and carriers verify ownership.
Location, contacts, and AI processing
Android 17 adds a one-time location button for sharing precise location during a specific task in an open app, along with a top-of-screen indicator showing recent location access. A redesigned contact picker lets developers request access to individual contacts and specific fields, with permissions kept temporary.
Android 17 introduces AISeal with pKVM for AI workloads, a hardware-backed isolation layer that pairs with Private Compute Core and Private AI Compute to process ambient data in a verified environment.
Other changes include automatic three-hour hiding of one-time passwords from most apps to block OTP theft, a carrier-configurable default-off setting for 2G connectivity, and the rollout of post-quantum cryptography across Android’s data protection stack. Android OS verification, launching on Pixel devices with Android 17, will allow users to confirm their phone is running an official build, backed by a public append-only ledger for Google-signed apps and GMS APIs.