The hidden smart fridge risks that emerge years after purchase
Household refrigerators are built to last more than a decade. The software, cloud services, and mobile apps that control them are not. A new analysis from Erik Buchmann at Leipzig University maps what happens when those two timelines collide, and the findings reach further than the kitchen.
The study examines three current models on the market: the Bosch KGN36HI32, the Samsung RF27T5501SG, and the LG GSX960NEAZ. Each adds network connectivity, mobile control, and in some cases cameras, voice assistants, and touchscreen apps to a core appliance whose mechanical components are expected to keep working for over ten years.
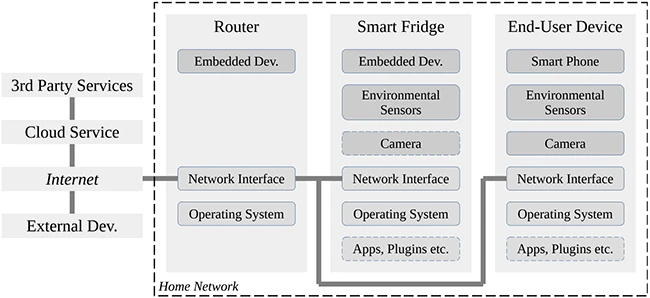
IT architecture (Source: Research paper)
Even basic cooling can depend on the cloud
Even cooling can become a long-term risk when the appliance ships with a stripped-down control panel and routes temperature adjustments through a smartphone app and a vendor cloud account. The Samsung RF27T5501SG, for example, requires owners to install the SmartThings app and register for a Samsung cloud account to access many functions.
If any link in that chain goes away, a working compressor and a working sensor array may still leave the owner with an appliance they can no longer configure as intended. A parallel case from earlier IoT history saw tens of thousands of internet radios stop working after a service provider shut down.
Three families of long-term risk
Buchmann groups the risks into compliance, economic, and operational categories.
Compliance risks come from changes in law and regulation after purchase. Privacy rules can restrict where personal data flows, trade and sanctions regimes can cut off specific vendors or regions, and product categories can be reclassified entirely. Germany banned a children’s smart toy three years after launch once authorities determined it functioned as a covert listening device.
Economic risks track the business decisions of the companies that keep the ecosystem running. Vendors can degrade older services to push customers toward newer products, switch to subscription pricing, discontinue a cloud platform, or go out of business and void existing warranties. Seven of the eight use cases identified in the study depend on services run by parties other than the owner.
Operational risks accumulate through technical aging. Devices lose compatibility with newer phones and home networks, security updates stop arriving, and expertise and spare parts for older interfaces become hard to source. Protocols considered secure at purchase can be deprecated within a few years.
The security cost of multimedia features
Buchmann’s protection-needs analysis produces a finding that has practical consequences for anyone using a fridge as a smart-home hub. Because the appliance handles configuration data, credentials, and operating system updates, every other service it runs inherits the same elevated security requirement. Streaming music or browsing recipes on the door panel is therefore tied to the same protection level as the device’s most sensitive functions. A weakness in a casual feature can expose the rest.
Thomas Uhlemann, Cybersecurity Evangelist at AV-Comparatives, told Help Net Security that the problem compounds once vendor updates stop. “As soon as a vendor stops shipping updates, the appliance freezes in time, but the threat landscape around it does not. Outdated TLS implementations, deprecated cipher suites, unpatched Wi-Fi stacks, hard-coded credentials in old firmware: all of these become permanent residents on the same LAN as everything else the household relies on.”
In AV-Comparatives’ lab work, Uhlemann says two failure modes recur. “An appliance with a weak or unauthenticated local API, still common in older smart kitchen firmware, gives an attacker who has already gained a foothold elsewhere a stable pivot point. The fridge does not need to be the entry vector to be the problem; it only needs to be reachable.” The second is protocol decay, where a device keeps speaking to its cloud backend over TLS configurations that current browsers would reject, or advertising internal network topology through legacy services.
The conclusion from the lab matches the conclusion from the paper. “The security posture of a home network is set by its weakest long-lived device,” Uhlemann says. A well-configured router and current endpoint protection raise the baseline, “but they cannot retroactively fix a device whose manufacturer has walked away from it.”
It’s annoying, not catastrophic
There’s some good news in here. For a regular household, none of the risks rise to the worst harm category in the analysis, things like serious illness from food poisoning or steep fines. The realistic worst cases are food that spoils, digital features that stop working for good, privacy exposure, and the appliance becoming an expensive paperweight. Buchmann adds that the math changes in higher-stakes settings, like a hospital using a connected fridge to store medication.
The lesson extends beyond fridges
Any consumer product that pairs long-lived hardware with software dependencies inherits the same structural problem. Smart televisions, connected ovens, networked thermostats, and home security panels all sit on the same fault line. The catalog of risks Buchmann assembles can be applied to any of them with minor adjustments to the asset inventory.
Anyone shopping for a smart appliance has a new question to weigh at the store: what will it still do once its supporting ecosystem moves on?
Bosch, LG and Samsung did not respond to a request for comment by the time of publication.

Download: 2026 SANS Identity Threats & Defenses Survey