Mobile device security is sacrificed for workforce efficiency
While mobile devices are an integral part of the workplace, the cyber security practices and budgets in most organizations are not keeping pace with the growing number of devices that must be managed and kept secure.
According to a new survey by Raytheon, 52 percent of organizations and employees frequently sacrifice security practices to realize the efficiency benefits of mobile connectivity.
The report was conducted by information security industry leader Ponemon Institute. The comprehensive report is based on 618 respondents who implement enterprise security, manage mobile technologies and platforms, and set mobile strategy. Fifty-seven percent of respondents identified themselves as senior executives/managers.
According to the research, on average one-third of employees use mobile devices exclusively to do their work and this is expected to increase significantly to an average of 47 percent of employees in the next 12 months. Even in light of this anticipated growth, 64 percent surveyed claimed that they do not currently or expect to have sufficient budget to mitigate or curtail mobile device cyber security threats.
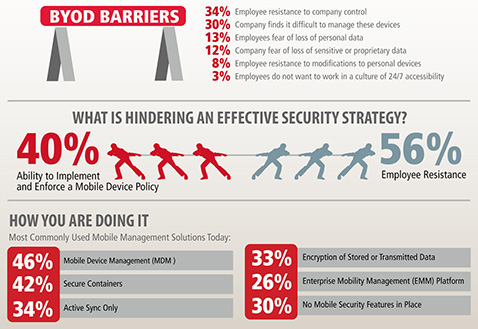
Despite the increasingly high levels of cyber security risks with mobile devices, the top two methods being used today – Mobile Device Management (MDM) and secure containers – are not sufficient. In fact, half of those surveyed are not satisfied with their organization’s current mobile security solutions, and 57 percent agreed that implementing a virtualization-based solution, which keeps data off of the actual device, should be considered.
“This survey points to the fact that there is a struggle to find the right balance between the cyber security needs of an organization and the efficiencies demanded by employees to do their jobs,” Ashok Sankar, senior director of product management and strategy at Raytheon Cyber Products. “Mobile devices are becoming a dominant workplace tool, and organizations must adopt a mobile strategy with data security technologies that enable employees to work effectively without putting sensitive information at risk.”