Scandinavian users hit with fake post office emails, ransomware
“Scandinavian PC users are the latest group to be targeted with Cryptolocker ransomware.
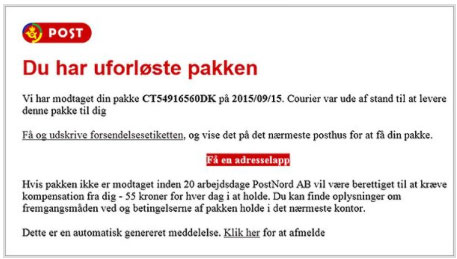
According to Heimdal Security, the threat comes via email. The malware peddlers are impersonating the Norwegian, Swedish and Danish postal services, and are trying to trick users into believing that there has been a failed delivery of a package.
They are instructed to click on the link in the email, supposedly to download the document needed to claim the package at the post office, but what they’ll get is an executable.
Those users who fail to find this suspicious and run the file will have all their files encrypted (both on the computer and on connected devices), and will be faced with a ransom message.
“Cyber criminals have been deceiving unsuspecting Internet users for a few years by using the post office emails scam. People fall for it, because the post office is one of the most familiar institutions for them, which they trust,” Heimdal’s Andra Zaharia explains.
The emails are usually written in the victim’s language, and are equipped with the logos and images associated with that country’s postal services (e.g. in Denmark: Post Denmark and PostNord).
The delivered malware is Cryptolocker2.
“The attackers behind this scam have refined their tactics to keep their anonymity by using multiple hosting providers around Europe to hide their traffic. A DGA (Domain Generation Algorithm) is also employed for the same purpose,” Zaharia shared.
“Cryptolocker2 has its own set of evasion tactics that it uses in order to trick traditional antivirus products into not detecting it. These include new ways to avoid anti-debugging and sandbox actions, but also a new right-escalation method to force access to legitimate windows processes through injection.”
When the campaign was first noticed earlier this week, the delivered malware variant had an extremely low AV detection rate – only one out of 56 AV engines used by VirusTotal flagged it as malware. Three days later, the numbers are better (34 out of 55), but the danger is still present.
Anyone can fall for this type of scheme, although it has been most successful with home users and employees of small-to-medium size businesses.
Users of all kinds should educate themselves about the danger, and first and foremost should stop clicking on links contained in emails whose senders they haven’t verified. Keeping you computer and security software regularly updated is a good idea, although will not provide complete security. Regularly backing up your files and not keeping that backup connected to the computer is the best thing you can do in the long run.”