Know your enemy: The most popular hacking methods
Outsiders want to become insiders with the least possible effort, and insiders help them do so – mostly accidentally, according to Balabit.
54% of the survey respondents said that, according to their experience, organisations are still afraid of hackers breaking into their IT network through their firewall. At the same time over 40% of them said that they already clearly see that first-line defence tools, such as firewalls are just not effective enough to keep the hackers away.
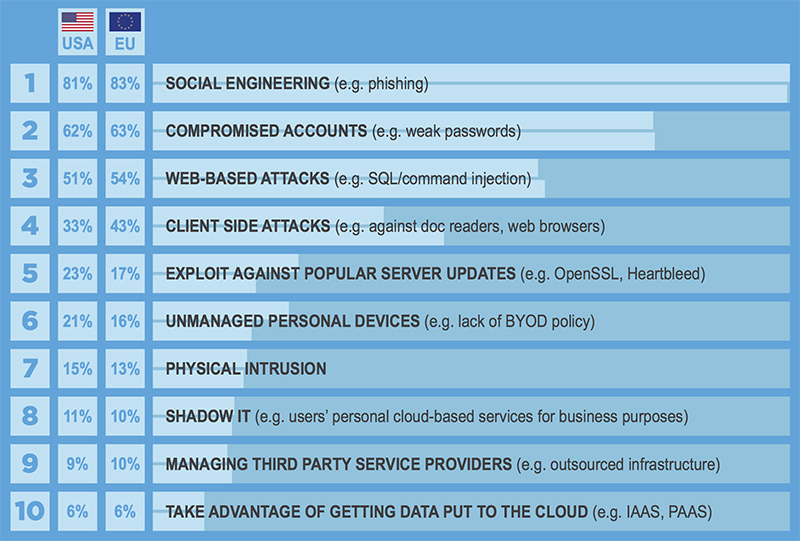
Balabit surveyed which methods or vulnerabilities IT security experts think that attackers are using the most – or taking advantage of – when they want to get sensitive data in the shortest time. Here are the most popular hacking methods:
Social engineering
Most of the attackers aim to get a low level insider user account and escalate its privileges. Trying to identify an existing corporate user and trying to break its password is a slow process and leaves so many footprints behind (e.g. lots of additionally generated logs as a result of the automated attacks) that greatly increases the risk of being noticed that something suspicious is happening. Therefore, hackers mostly use social engineering attacks when users “voluntarily” give their account and password.
“Traditional access control tools and anti-malware solutions are necessary, but these only protect companies’ sensitive assets while hackers are outside of the network. Once they manage to break into the system, even gaining a low level access, they can easily escalate their rights and gain privileged or root access in the corporate network. Once it happens, the enemy is inside and poses a much higher risk as they seem to be one of us,” said Zoltán Györkő, CEO at Balabit.
Compromised accounts
Compromised accounts, especially weak accounts are dangerous because users commonly use weak passwords, sometimes the same password is used both for corporate and private accounts. In case a hacker can gain such a user’s account and password in a less secured system (such as through a private social media account), it can easily be used to log into the company network.
Web-based attacks
Security issues of web based applications such as SQL injections still rank as very popular amongst hacking methods, mainly because applications are the #1 interface for company assets for many insider and outsider users therefore providing a huge attack surface.
Unfortunately the quality of application codes are still questionable from a security point of view, and there are many automated scanners from which attackers can easily detect vulnerable applications.
The other hacking methods listed can also have the same results for attackers but might be a bit more complicated or time-consuming, for instance, writing an exploit takes time and requires good coding skills.
The additional most popular hacking methods are ranked as follows:
- Client side attacks (e.g. against doc readers, web browsers)
- Exploit against popular server updates (e.g. OpenSSL, Heartbleed)
- Unmanaged personal devices (e.g. lack of BYOD policy)
- Physical intrusion
- Shadow IT (e.g. users’ personal cloud-based services for business purposes)
- Managing third party service providers (e.g. outsourced infrastructure)
- Take advantage of getting data put to the cloud (e.g. IAAS, PAAS).