Phishing underground: Exploiting the human vulnerability
At the RSA Conference in San Francisco, PhishLabs exposed the murky evolution of a thriving, sophisticated phishing underworld.
Their report is based on more than one million confirmed malicious phishing sites residing on more than 130,000 unique domains, and the movement of more than 90 threat actor groups and organizations actively deploying spear phishing.
Key findings
- Spear phishing remains the primary initial attack vector used by APT actors. However, 22 percent of spear phishing attacks analyzed in 2015 were motivated by financial fraud or related crimes.
- The number of organizations targeted with Business Email Compromise (BEC) spear phishing attacks grew tremendously in 2015 as threat actors refined BEC techniques and sought new victims.
- 90 percent of consumer-focused phishing attacks targeted financial institutions, cloud storage/file hosting sites, webmail and online services, ecommerce sites, and payment services.
- While financial institutions and payment services continue to be the most highly targeted organizations, their share of overall phishing volume declined in 2015.
- There was a distinct increase in the percentage of phishing attacks targeting cloud storage and file hosting sites, webmail and online services, and ecommerce sites.
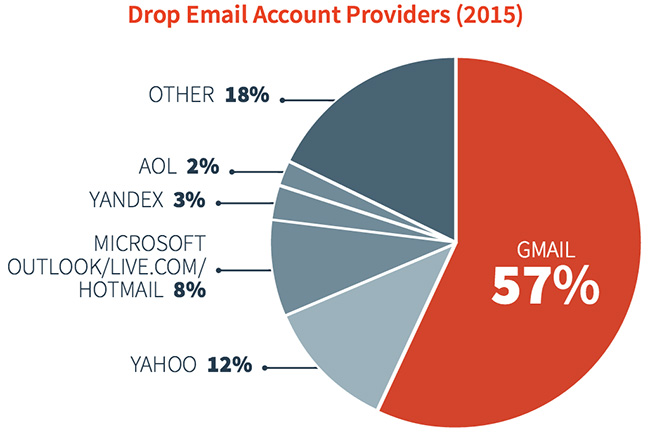
- Gmail is used for more than half of all data drop email accounts, making it the top webmail service used by attackers to receive credentials stolen via phishing.
- During the holiday season, online services and ecommerce companies were heavily targeted while attacks targeting other sectors declined.
- Social media is a primary promotion and distribution channel for consumer-focused phishing kits and related goods or services.
- Techniques to evade automated detection of phishing attacks and to prevent analysis of attack components are becoming more commonplace, even among less sophisticated threat actors.
“Our research clearly shows that phishing attacks are the weapon of choice for adversaries across the spectrum,” said John LaCour, Founder and CEO of PhishLabs. “Most successful hacks today start with a phishing attack. It is critical for organizations to understand the true risk of phishing and how they can fight back to protect their business.”
