The advent of GDPR could fuel extortion attempts by criminals
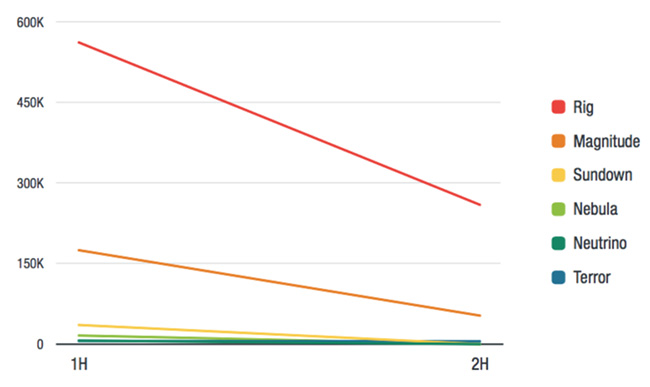
The number of exploit kit attacks is, slowly but surely, going down, and malware peddlers are turning towards more reliable tactics such as spam, phishing, and targeting specific, individual vulnerabilities.
That’s the good news. The bad news is that everything else is on the rise: BEC scams, ransomware, stealthy crypto-mining, the number of enterprise records compromised in data breaches.
2017 threat landscape
Trend Micro has released its annual security roundup the past year, and it shows several interesting trends that will likely continue into 2018:
BEC scams. BEC scams more than doubled in the second half of 2017 over the first half, and BEC incidents cost companies billions of dollars. This particular scam is very effective, relatively simple to pull off and can net criminals substantial sums, so it’s no wonder that it’s so popular.
Also, even though these scams have received much attention from the press, there’s seemingly a never-ending pool of potential victims who still don’t know about them, and readily fall for it. No company or industry is safe: the scammers go after tech companies, real estate firms and home buyers, art galleries and dealers, transportation companies, and so on.
The meteoric ascent of stealthy crypto-mining. Criminals going after cryptocurrency can choose between a variety of tactics: they can create apps carrying mining malware, compromise websites and make them quietly serve mining scripts, trick ad networks into delivering miners, deliver malware that steals cryptocurrency wallets, and so on. Also, they can compromise cryptocurrency exchanges and IPO offerings, or trick users into handing them their funds through simple scams.
Another interesting discovery is that compromised IoT devices are used less to fuel DDoS attacks, and more to for cryptocurrency mining, despite the fact that processing power of small IoT devices is limited. Still, the criminals count on “strength in numbers.”
Ransomware still going strong. 2017 witnessed the emergence of over 300 new ransomware families. Their names are many and varied: some are as plain and direct as “Blackmail,” “Locked,” or “Payment”; some evoke more popular threats (“WannaSmile,” “LockCrypt,” “Spectre,” “CoNFicker”); and other seem randomly chosen words and variations (“Bubble,” “Zero,” “Oops”)
You probably haven’t heard about most of them, as the number of their infections is dwarfed by the real, widespread threats: WannaCry, Cerber, and Locky.
“Overall, the total WannaCry detections towered over both Cerber and Locky, two of the biggest ransomware players in terms of longevity, and even the rest of the ransomware families combined,” the researchers shared.
Other ransowmare attacks of note in 2017 were Bad Rabbit and the attack that resulted in a South Korean web hosting provider paying $1 million to the attacker, who leveraged a Linux variant of the Erebus ransomware.
2018 threat landscape
Cyber criminals have made a definite move towards extorting organizations and are refining and targeting their attacks for greater financial return.
“The 2017 roundup report reveals a threat landscape as volatile as anything we’ve seen, with cybercriminals increasingly finding they’re able to gain more — whether it’s money or data or reputation damage — by strategically targeting companies’ most valuable assets,” says Jon Clay, director of global threat communications for Trend Micro.
The company’s researchers believe that, with the advent of GDPR, it’s likely that some criminals will try to extort money from enterprises by first determining the GDPR penalty that could result from an attack, and then demanding a ransom of slightly less than that fine, which CEOs might opt to pay.
Another definitive trend is the extremely obvious attackers’ preference for spam email as the main ransomware propagation mechanism.

Between that and BEC scams, the need for effective spam blocking solutions and security awareness training on phishing and social engineering tactics seems quite obvious.