Social Mapper: A free tool for automated discovery of targets’ social media accounts
Trustwave has released Social Mapper, an open source tool that automates the process of discovering individuals’ social media accounts.
How Social Mapper works
The tool takes advantage of facial recognition technology and searches for targets’ accounts on LinkedIn, Facebook, Twitter, Google+, Instagram, VKontakte, Weibo and Douban.
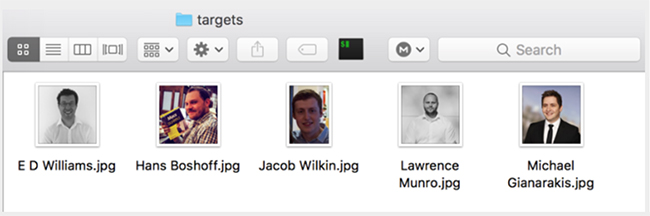
It accepts input in several forms: an organisation’s name, searching via LinkedIn; a CSV file with names and URLs to images online; or a folder full of images named after the subject:
The mapping process is performed in three stages.
First the tool creates a list of targets based on the provided input, then it performs the online search. But it doesn’t rely on APIs to do that – instead, it opens a Firefox browser window, logs into the aforementioned social media sites, then begins searching for the targets by name.
“It pulls out the top results from this search (usually between 10 and 20) and starts downloading the profile pictures and performing facial recognition checks to try and find a match,” says Jacob Wilkin, a security analyst with Trustwave SpiderLabs and author of the tool.
“It’s possible to tweak the way it performs via various parameters when the tool starts with options such as: if the program should keep searching after an initial match is found for a better one, and to change the thresholds of the facial recognition to remove more false positives at the risk of missing legitimate profiles.”

He also noted that this stage can take a while. For example, to compile a list for 1,000 targets can take over 15 hours (and a large amount of bandwith).
Then, finally, the tool provides the data in a useful format: a CSV file with links to the profile pages of the targets and a visual HTML report.
Use cases
After this initial reconnaissance process, the collected information can be used to create fake social media profiles to “friend” the targets and trick them into download malware, phish them (either via the service or via mobile phone), create custom phishing sites to steal their credentials, and more.
Social mapper is intended for ethical hackers: penetration testers and red teamers. But, of course, it can be also used by hackers and scammers.
Wilkin has presented the tool at the Black Hat USA 2018 Arsenal.