Deception for proactive defense
This article is fourth in a five-part series being developed by Dr. Edward Amoroso in conjunction with the deception technology team from Attivo Networks. The article provides an overview of using deception as part of a proactive defense, including strategies for deception deployment, post-compromise, incident response, and mitigation against returning attackers.
Proactive and balanced defense
For many years, enterprise cyber security was primarily reactive. That is, a network perimeter was established to prevent attacks, and if a breach occurred, then response activities were initiated. Typical cyber response activities would include perimeter adjustments, vulnerability remediation, and damage containment. The methodology of prevent, detect, and respond (in that order) has thus driven cyber security design for most teams.
This methodology is fine, so long as balance exists across the tasks. For example, it is obviously better to prevent something than to deal with its consequences, but this is not always possible. Each task thus plays a role in enterprise security. The problem is that in many recent cases, the emphasis has tilted toward response – often called a “shift right” in the methodology. Such reactive emphasis stems from the incredible advances that have occurred in offense methods.

Tendency to shift right in cyber defense lifecycle
One consequence of this shift is an increase in passive methods that are activated post-compromise. Sadly, this is unacceptable for mission-critical operations, where damage to critical infrastructure cannot be allowed. The good news is that many security teams today are opting to shift back toward a more balanced view of the cyber defense lifecycle. Deception, as we will explain in this article, plays a central role in this more proactive and balanced approach.
Cyber deception, as most practitioners understand, involves strategically using landmines and lures with breadcrumbs to trap an attacker. The deception can be viewed as reactive, because it prompts behavior for monitoring, but it can also be viewed as proactive, because it diverts breach activity away from production resources. In addition, good deception allows security teams to be alerted quickly when policy violations are detected.
Deception provides balance because it is useful during all aspects of the prevent, detect, and respond lifecycle. For example, during all these tasks, deception captures attacker TTP (Tactics, Techniques, Procedures) information and valuable forensics. The resulting threat intelligence helps isolate infected systems, block attackers, identify early indicators, and support the security operations center (SOC) hunt team in their response work.

Deception in all phases of the cyber defense lifecycle
The result of deploying deception is that enterprise security teams can be both proactive and reactive in their defensive approach to modern cyber threats. Organizations can also keep the pressure on the adversary during all phases of their attack lifecycle and leverage threat intelligence that is collected during early reconnaissance information, which is vital to derailing and remediating cyber attacks.
Deception deployment
Strategies for deploying deception are driven by an organization’s architecture, environment, and risk appetite. Modern deception technology platforms provide excellent options for covering a diversity of enterprise needs. For example, deceptive traps can be easily embedded into environments such as user networks, data centers, public and private clouds, remote office locations, and in other specialized environments.
Design options also cover a range of targets, from legacy devices to the most modern architectures in the cloud with server-less and container deployments. Additional deception services for application, data, and database deception can be deployed into the enterprise, thus increasing the attractiveness of the investment, and providing maximum detection benefits for organizations with the lowest risk thresholds.
From a practical perspective, however, decisions about the best locations for deception should follow a risk management process. That is, an enterprise should be utilizing knowledge and insights about their actual cyber security risks to drive proper placement of deception. Other considerations include factoring in the protection of legacy assets that may, for technical or business reasons, not readily receive the latest and best security updates.
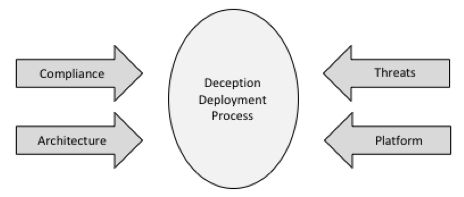
Factors driving deception deployment
In the future, one might expect more subtle decision-making about deception deployment. This decision-making will be influenced by risk appetite thresholds, existing security control effectiveness, and analytics for threat tracking, reporting, and accountability. As deception use matures, these considerations will become more important in the protection of organizational assets, both from the lens of IT risk management as well as digital risk management strategies.
Post-compromise incident response and forensics
In addition to the advantages that deception offers across the entire cyber defense lifecycle, one of the most powerful advantages of deceptive lures, traps, and breadcrumbs is the effective support offered for incident response and forensics compromise. The Attivo Networks ThreatDefend platform provides a live window into the TTPs of an adversary that believes it has reached a real enterprise target.
It makes sense that an attacker will feel empowered – perhaps letting their guard down – once they have achieved access into what appears to be a live and realistic target infrastructure. If deception is in place, the adversary will have the mistaken impression of having gotten past security controls to reach a valued resource. The perception of success may serve to embolden an adversary to demonstrate their tactics to the deceptive collection system.
What happens more specifically is that an attacker assumes that the usual gauntlet of security controls is in place when targeting an asset. For example, if the target is a back-end database, then the attacker expects that they must traverse layers of protection in the network, edge, and hosting before they gain access to the targeted database. If they reach a deceptive decoy that presents the expected database interface, the adversary will assume they have defeated the earlier gauntlet of controls.

Adversary confidence in an advancing breach (real vs. deception)
The advantage of having an adversary behave in a less constrained manner while caught in the deception environment is that it provides an often-unachievable view into attacker TTPs and offers more accurate visibility into attacker activity for forensic analysis. Many cyber experts now believe that behavioral analysis in a realistic deception environment provides the best possible view of modern attack methods.
For this reason, enterprise security teams use deception into their post-compromise response toolkit to support incident response, automated handling, threat hunting, and returning adversaries. Many have also found the Attivo Networks DecoyDocs functionality insightful when trying to establish attribution. When a DecoyDoc is taken, the organization gains knowledge of the documents being stolen, and the geolocation where the document is opened.
Mitigation against returning attackers
One challenging problem for cyber defenders is that once an adversary has successfully compromised a target, they will be likely to return to that target at some later time. For example, FireEye researchers report that an average of 56% of attackers will return. If a defensive team changes the protection posture, they may well thwart an adversary’s subsequent attempts.
Unfortunately, however, many enterprise security teams lack detailed insight into attacks and TTPs. The result is that they therefore don’t change their security posture post-attack. In many cases, they also face time and resource constraints that limit their ability to identify and mitigate backdoors left by the intruder or to understand how the perpetrator bypassed their security controls. These are unfortunate cases, as they increase risk considerably.
The Attivo Networks ThreatDefend platform includes tools for understanding exposed credentials and system configuration issues which could create entry points for an adversary. With continuous visibility, an organization can proactively shut down these paths. Attivo also uses machine-learning to prepare deceptions for deployment. This improves understanding of endpoints coming on and off the network. It is often hard for a security team to know when unauthorized devices are added, so a visual mapping illustrate these changes.
Attivo Networks has also added tools for vulnerability simulation, which is important for penetration and compliance testing. The Attivo Networks platform efficiently proves security control resiliency and provides the recoding required for incident tracking and reporting. Collectively, this approach to continuous assessment provides organizations valuable tools for shutting down security exposures and for insight into ways to build a more proactive defense.
An advantage of deception for building a proactive, preemptive defense is its ability to develop a behavioral profile of an intruder, along with insight into how an attacker successfully infiltrated their networks. Leveraged correctly, one can fortify their defenses, slow an attacker, and more easily detect and derail a returning attacker. In many cases, behavioral trends or tendencies might be the only clues left by an attacker across multiple attack campaigns.
Law enforcement has embraced adversary intelligence for years, but now with commercial platforms such as from Attivo Networks, this capability is available to organizations of all sizes. Attivo Networks delivers deception technology for early and accurate threat detection and empowers security teams with the technology to build a proactive defense designed to make attacks harder, slower, and more costly.
Stay tuned for Article Five, my final article in this series, which will explain how deception fits into information risk management strategies and how organizations can answer C-level ROI questions for justifying deception.