Targeted threat intelligence and what your organization might be missing
In this Help Net Security podcast recorded at Black Hat USA 2019, Adam Darrah (Director of Intelligence), Mike Kirschner (Chief Operating Officer) and Christian Lees (Chief Technology Officer) from Vigilante, talk about how their global threat hunting and dark web cyber intelligence research team extends the reach of a company’s security resources, and lives within the underground community to remain ahead of emerging threats.

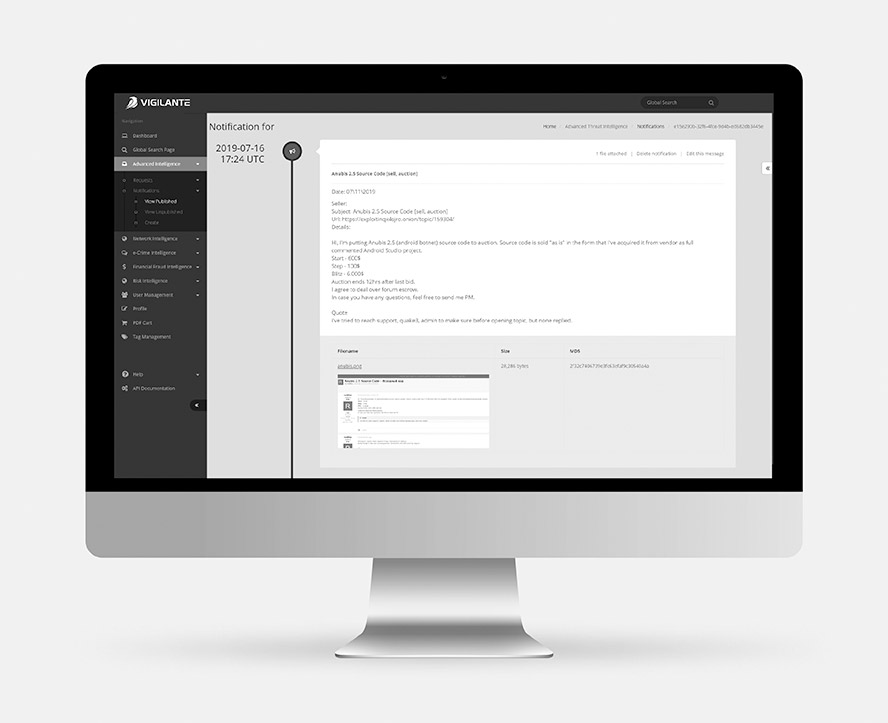
Where many other solutions rely on machine learning (ML) to access and assess data, Vigilante is integrated into dark web communities and places where ML cannot infiltrate to offer a blend of open source and human intelligence. They do the heavy lifting to engage, triage and curate intelligence that is targeted to your specific needs.
Here’s a transcript of the podcast for your convenience.
Good afternoon. Welcome to today’s podcast. My name is Adam Darrah and we’re happy to be here today as part of a new cybersecurity company called Vigilante. I’m Adam Darrah, the Director of Intelligence and discussing issues today we have Mike Kirschner, our Chief Operating Officer and Christian Lees, our Chief Technology Officer.
We’ll take a few minutes to introduce each member of our team and then go on to talk about our perspective on targeted threat intelligence and what an organization might be missing if they don’t have proverbial boots on the ground in the dark web. But first let’s go ahead and turn some time over to Mike and Christian to introduce themselves.
Mike Kirschner: My name is Mike Kirshner and the Chief Operating Officer for Vigilante. I do want to highlight that this organization is not a new organization. We’ve really been in operation for many years. The organization itself is parented originally through InfoArmor, and we have really been in place for the last six or seven years, delivering targeted threat intelligence to enterprises around the globe. We’re excited though to be finally splitting ourselves off and isolating ourselves from the parent, operating independently and are excited to move forward that way.
Christian Lees: Second to what Mike said. Christian Lees. I’ve been with the organization since its inception back in 2009 and then a security professional for, my goodness, over twenty-five years!
Adam Darrah: Excellent. We appreciate both of you being here today. We’re excited to bring the story of Vigilante out to the podcast community. But Mike, first question over to you: how important is utilizing threat intelligence? Can you explain how small or even mid-sized companies can get started if they haven’t already?
Mike Kirschner: Sure. Well, I think the first thing we need to do really is define terms. Threat intelligence as a term in many cases has been a little bit hijacked, and I think the audience may feel as though it is simply another feed of IOCs. From our perspective, threat intelligence really represents any sort of targeted content and contextualized content that would represent a risk or a threat to an organization. From that perspective it could be compromised content and data, it could be intellectual property that has been exposed and/or is being leveraged inappropriately in the underground, it could be extortion attempts or exploits that are being targeted toward an individual organization. So, in all these cases we are leveraging the combination of automation and human operatives to add a very broad approach to the market, a highly contextualized, highly targeted approach to the market, and then delivering that at scale to a very broad – from small and midsize business businesses to very large enterprises – very broad spectrum of enterprises.

Adam Darrah: Christian what do you think?
Christian Lees: I think, excellent summary absolutely. In retrospect of the years that we have done this, I’ve found that the most fruitful cooperation comes from organizations that continuously understand their environment, have the ability to not only talk about risk but define their own risk and their appetite for risk, and understanding the actual landscape of their own network, and can actually cooperate with us and have more meaningful investigations.
Considering that we are largely a human intelligence team, we leverage human members to gain access to very unique data streams. So, the organization has to be prepared to really define what threats are out there, and an understanding of their environment is very helpful.
Of course, we have a lot of data that can just be directly ingested through our API. But having that collaborative partner is really helpful, and intelligence and TI. Small organizations can certainly invest in their own environment by looking at open source intelligence, but they also have to be ready to triage that, homogenize that, and correlate that. And that’s a pretty big cost, so having a team like Vigilante is very helpful for companies, in my opinion.
Adam Darrah: Yeah. I want to talk a little bit more about that. Specifically, what makes Vigilante different from the other threat intelligence companies that are out there? I’ve heard similar themes, talking with other colleagues in the industry, all of them are incredibly smart, incredibly capable. They have excellent capability and insight into the industry. How would you explain the difference between us and the advantage a client could get working with us?
Mike Kirschner: I think there are a couple of keys when we look at this. First of all, as Christian mentioned, there really are a variety of, well let’s boil it down to three primary themes, when it comes to trying to target particular areas that are meaningful for an organization.
The first would be visibility or education, understanding what your threat risk or threat landscape looks like in terms of targeting that organization. Then, creating access with a team of individuals that can both engage as well as capture content that would be meaningful for an organization and then taking action. I think, figuring out what are we going to do with this content.
The advantages that Vigilante brings to the table really are, as I pointed out earlier, the combination of leveraging automated tools to capture content, enable some of this education and visibility to take place, and then the human team of operatives that can engage with individuals in the underground and really has been cultivating their cyber personas for a decade plus in these trusted arenas, to be able to then capture that pre-emptive intelligence that allows an organization to take that action to defend itself, to move forward in a way that can defend its own assets or its own individual employees, for that matter.
Christian Lees: I also think it’s worth noting that a lot of organizations today are sold whole solutions and there really is not, in my humble opinion, a silver bullet. There’s not typically a single pane of glass. I know that’s what we want. I also think it might also be, Mike I’d be curious of your thought on this. I think it’s also worth noting that the security industry is under a tremendous amount of stress in terms of very capable security seasoned professionals, and a lot of times I would assume that many organizations try to build threat vectoring and threat intelligence, and oftentimes you get 60, 80 percent of the way through and they had some kind of turnover in manpower.
One of the benefits of Vigilante is that, like you mentioned, we have a very vetted ecosystem of threat intelligence that we continuously maintain, it hypothetically never goes away. We’ve spent the man-hours in getting this environment and leveraging that as opposed to building it internal. The ROI is nearly immediate.
Mike Kirschner: I think you’re right. And I think one of the other advantages is just that consistency. We do see a tremendous amount of turnover evolution with security teams as they grow and evolve. The opportunity for us to maintain that consistent thread of deliverables for this group and for them to be able to rely on our team, to be able to extend their reach, is critical with any organization.

Adam Darrah: Thank you very much. Pivoting off of what Vigilante can do, let’s talk about what Vigilante sees out in the threats face. Christian, there is a lot of information out there leaking and lurking, whether it’s an S3 bucket or a direct breach with data dumped by hackers. As you see it, what are the biggest problem areas for an organization in regard to security and privacy today?
Christian Lees: This is technology evolving, and there is this mass exodus from on-prem to third- party services, and just the ease of lighting your data into a third-party shared tenant service is astonishing. And the ease of exposing that data is just mind boggling. I will say firsthand, having been in this business for quite a number of years, the last two years it seems to have exploded, the amount of misconfiguration, the amount of data that appears to be associated to a brand and unknowingly exposed or at risk, is just its own problem. And whether it’s misconfigured elastic engines, or MongoDB, or S3 buckets, it’s a huge tremendous problem. Organizations need assistance in that area. It’s a very scary world we live in today.
Adam Darrah: Yes. Mike over to you. Talk to us a little bit about what it means to have humans at the heart of an organization’s threat hunting efforts and the difference targeted intelligence can make. And where does automation play a role? You mentioned earlier, automation and human intelligence. Talk to us a little bit more about how those things can coexist and what we’re doing to push forward.
Mike Kirschner: Sure. Look let’s start with the automation piece. Christian just mentioned S3 buckets as one example. I think this rush to the cloud that organizations have really embraced over the last few years, is creating a lot of this opportunity or exposure. I shouldn’t call it opportunity necessarily, but it is an opportunity for us to again educate and create awareness around some of the risks associated with platform, with overall process and the way that organizations are kind of embracing third-party services.
To that end, the value that the human intelligence side of things really brings is, as we begin to identify issues and identify specific threats to an organization that are typically tied back to an actor or an actor group, the ability to engage with that actor, understand their motivations, engage with that actor group, try to understand what kind of content they’re after. What does their history and their track record look like in terms of the ways that they have leveraged information in the past, exploited organizations in the past, in order to help these individual enterprises that are in the crosshairs of these organizations, defend themselves, engage with law enforcement in the event that that’s necessary, and/or leverage our team to extend their reach in order to either recover assets or identify specific areas of exploitation or risk. Those are things that machine learning and artificial intelligence just can’t afford an organization. That’s the value that the human team brings.
Targeted intelligence I think is important. Again, as we define terms, Christian did a good job of kind of highlighting some of the areas here. We have this massive flood of data. Alert fatigue is a significant issue, really understanding, triaging those risks, understanding what is it, how do I apply my resources effectively?
Our ability to very specifically target these issues, triage these issues on behalf of the client and then alert them when there’s something that they can actually take action against is meaningful, and that’s how we would typically define targeted intelligence. Intelligence that’s specific to their organization, that they can take immediate action to defend themselves against and/or do something with.
Adam Over the last year, as we’ve all been working together with InfoArmor and now Vigilante, one of my observations has been that the most meaningful engagements happen when there is a robust feedback loop between the intelligence team, us, and a company’s intelligence team. After you’ve established trust, and after you’ve established a solid relationship that’s built on discretion, then we get into a very robust feedback loop. Over the past year we’ve seen some meaningful results because of that relationship and Vigilante feels very strongly about maintaining a regular cadence. We are very aware of alert fatigue and we appreciate our client’s commitment to feedback, and we do pivot, we adjust accordingly.
Christian Lees: Do you think, just very quickly, in terms of automation, I know that there’s a lot of brands out there selling whole suites around automation. Is it fair to outline that automation is just incapable in our environment in terms of bypassing that kind of area? Great and open source but on the other side of the spectrum, there’s just not an automation tool out there, and it really does require manpower.
Mike Kirschner: Yeah. In very close source communities, to Adam’s point, this really comes down to relationship. It’s a relationship between individuals in a trusted environment, and that’s just not something that automation can necessarily enable. That’s the combination of our ability to leverage the dissemination of information through automation, whether it’s via an API or through some other integration point, is meaningful in terms of being able to scale this to a very broad audience. The SMB market, for instance, is very underserved at this point, but being able to enable this continent scale is huge. On the other side of that coin then, the ability to curate that data through those relationships is very meaningful from the perspective of being preemptive about the way that we can enable time to action.
Adam Darrah: I just want to make another observation that one of our goals is, the client should feel as though they are being served. They know who to call. They have a person to call. They have a person to email. They know us. They trust us and we put a lot of value in personal relationships with our operative teams, amongst our internal team, and definitely between our intelligence staff, sales, and our clients. It means a lot to us.
It’s been a real pleasure today introducing the world to Vigilante and want to alert the community to our web site vigilante.io for more information about the topics we’ve discussed today. And to more fully understand what we do and how we can serve you and your needs.