Cybersecurity breach experience strengthens CVs
It is in businesses’ best interest to hire cybersecurity leaders who have suffered an avoidable breach, because of the way it changes how security professionals think, feel and behave, according to Symantec.
The findings reveal that suffering a breach – and coming out the other side – significantly reduces security leaders’ future workplace stress levels, while improving their likelihood to share knowledge.
“It might sound counter intuitive at first,” comments Darren Thomson, CTO, Symantec EMEA, “but if I offered you two CISO candidates with an identical skillset, but one of them has managed through a breach and finds dealing with regulation less stressful, is less likely to suffer from burnout, and more willing to share the lessons they’ve learned during their career, who are you going to pick?”
Cyber security professionals that have experienced an avoidable breach are:
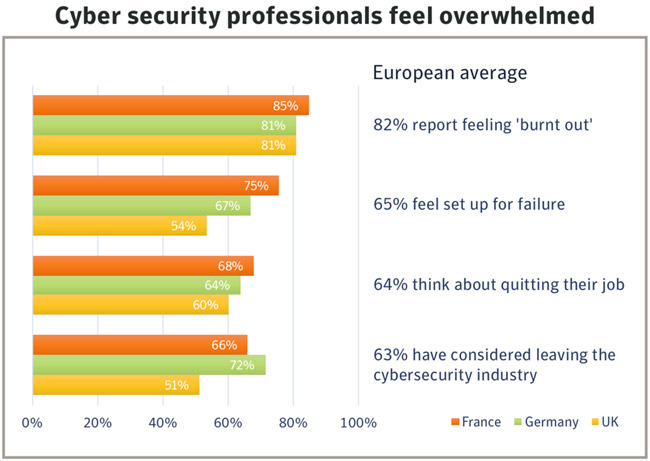
- 24% less likely to report feeling ‘burnt out’
- 20% are less likely to feel indifference toward their work
- 15% less likely to feel personally responsible for an incident that could have been avoided
- 14% less likely to feel ‘set up for failure’
- 14% more likely to share their learning experiences
- 14% less likely to think about quitting their job
Learning from ‘failure’
Perhaps the most positive findings are that those who have experienced a breach are 14% more likely to share their experiences with their peers. This is a crucial change in behavior as the research also reveals a lack of strategic and operational information sharing across the industry.
Large scale security incidents are career defining moments, but due to a lack of peer to peer information sharing it’s hard to learn from others’ experiences.
- 54% explicitly do not discuss breaches or attacks with peers in the industry
- 50% of all respondents report a distinct lack of cross industry information sharing about managing incidents, which stands in stark contrast to the weaponized collaborative culture of modern hackers
Whilst undoubtedly driven by multiple factors, this suppression of knowledge sharing seems exacerbated by how these incidents might impact their reputation. 36% said they were worried that sharing information about incidents that took place ‘on their watch’ – with peers, colleagues or prospective employers – could adversely impact their career.
Darren Thomson, CTO, Symantec EMEA, adds: “My advice to CEOs is to see a cyber professional with a breach on their CV as a strength, rather than a weakness. Clearly, it’s an incredible learning experience, but the positive impact on a candidate’s character is just as valuable – they’re less emotionally-charged, better at dealing with pressure and more likely to mentor others.”

Never waste a crisis
Almost half agree that a breach is inevitable, it’s just a matter of time. Cyber security professionals who have suffered a breach are more likely to have benefitted from the increased attention and board level prioritization of remediate measures.
“My advice to fellow CISOs would be: Never waste a good crisis. Many businesses have the opportunity to create and roll out improved practices and services as a result of a breach,” says Ben King, CSO, Symantec EMEA.
“It’s a situation that helps a whole range of stakeholders relate to the challenges the security teams face – and backs up their requests for budgetary and organizational support. Especially in the private sector, if security leaders can use security incidents to get CEO buy-in, they can mobilize change in a way that’s often not possible when it’s business as usual”.