Technologies in all layers of the cloud stack are at risk
As breaches and hacks continue, and new vulnerabilities are uncovered, secure coding is being recognized as an increasingly important security concept — and not just for back-room techies anymore, Accurics reveals.
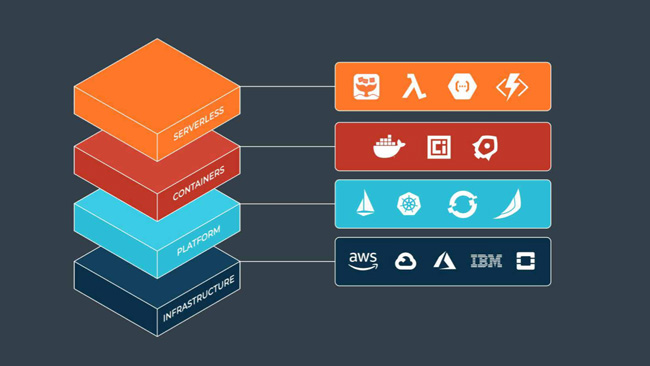
Cloud stack risk
“Our report clearly describes how current security practices are grossly inadequate for protecting transient cloud infrastructures, and why more than 30 billion records have been exposed through cloud breaches in just the past two years,” said Sachin Aggarwal, CEO at Accurics.
“As cloud stacks become increasingly complex, with new technologies regularly added to the mix, what’s needed is a holistic approach with consistent protection across the full cloud stack, as well as the ability to identify risks from configuration changes to deployed cloud infrastructure from a baseline established during development.
“The shift to infrastructure as code enables this; organizations now have an opportunity to redesign their cloud security strategy and move away from a point solution approach.”
Key takeaways from the research
- Misconfigurations of cloud native technologies across the full cloud native stack are a clear risk, increasing the attack surface, and being exploited by malicious actors.
- There is a significant shift towards provisioning and managing cloud infrastructure through code. This offers an opportunity for organizations to embed security earlier in the DevOps lifecycle. However, infrastructure as code is not being adequately secured, thanks in part to the lack of tools that can provide holistic protection.
- Even in scenarios where infrastructure as code actually is being governed, there are continuing problems from privileged users making changes directly to the cloud once infrastructure is provisioned. This creates posture drift from the secure baseline established through code.
Infrastructure as code
The research shows that securing cloud infrastructure in production isn’t enough. Researchers determined that only 4% of issues reported in production are actually being addressed. This is unsurprising since issue investigation and resolution at this late stage in the development lifecycle is challenging and costly.
A positive trend identified by the research is that there is a significant shift towards provisioning and managing cloud infrastructure through code to achieve agility and reliability.
Popular technologies include Terraform, Kubernetes, Docker, and OpenFaaS. Accurics’ research shows that 24% of configuration changes are made via code, which is encouraging given the fact that many of these technologies are relatively new.
Infrastructure as code provides organizations with an opportunity to embed security earlier in the development lifecycle. However, research revealed that organizations are not ensuring basic security and compliance hygiene across code.
The dangers are undeniable: high severity risks such as open security groups, overly permissive IAM roles, and exposed cloud storage services constituted 67% of the issues. This is particularly worrisome since these types of risks have been at the core of numerous high-profile cloud breaches.
The study also shows that even if organizations implement policy guardrails and security assessments across infrastructure as code, 90% of organizations allow privileged users to make configuration changes directly to cloud infrastructure after it is deployed. This unfortunately results in cloud posture drifting from the secure baseline established during development.

Recommended best practices
- The importance of protecting the full cloud native stack, including serverless, containers, platform, and infrastructure
- Embedding security earlier in the development lifecycle in order to reduce the attack surface before cloud infrastructure is provisioned, as well as monitor for incremental risks throughout its lifecycle
- Most importantly, preventing cloud posture drift from the secure baseline established during development once infrastructure is provisioned