2020 vulnerability disclosures on track to exceed those from 2019
2020 vulnerability disclosures are on track to exceed 2019 despite a sharp decrease of 19.2% observed earlier in the year, according to Risk Based Security.

The team aggregated 23,269 vulnerabilities disclosed during 2020. Despite the initial disruption from COVID-19, the trend of total number of vulnerabilities suggests that business operations and routines have normalized as the gap has closed to 0.98%.
“2020 could be titled ‘The Great Catch-up’. We saw an incredible drop of 19.2% in Q1, but with each subsequent quarter that massive gap steadily closed,” commented Brian Martin, VP of Vulnerability Intelligence at Risk Based Security.
“The question now is how COVID-19 will impact the 2021 vulnerability landscape. Have we fully shaken off the disruption from the pandemic, or will we still see some lingering side-effects?”
CVE continues to fall behind in coverage
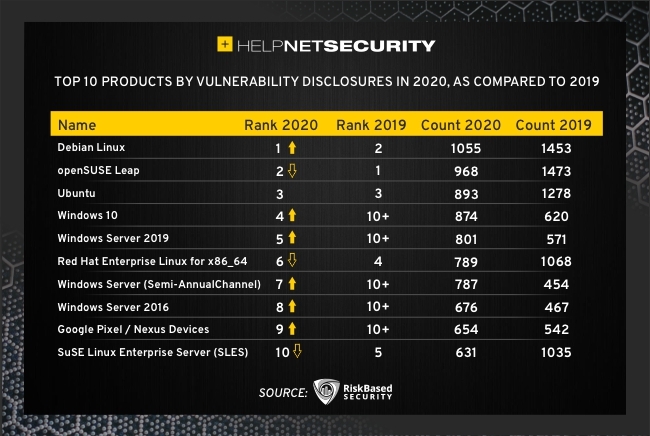
The report goes into further detail on how vulnerability disclosures caught up throughout the year. In the midst of the pandemic we experienced three Vulnerability Fujiwhara events, a term adopted for the collision of patch releases from Oracle, Microsoft, and other major vendors on the same day. These Vulnerability Fujiwhara result in challenging workloads for vulnerability management teams, and made timely patching and remediation a difficult task for many organizations.
Adding to the difficulty is the fact that CVE continues to fall behind in coverage. CVE failed to report 29% of known vulnerabilities in 2020. Organizations relying on CVE/NVD may struggle to justify that gap to auditors and management.
“In 2020, CVE failed to report 29% of known disclosed vulnerabilities and organizations looking for those details can find those missing vulnerabilities in VulnDB,” Mr. Martin concluded.
“Our VulnDB team hit a major milestone of 80,000 aggregated vulnerabilities without a CVE ID. Now that it appears operations have mostly normalized, those who are wary or are struggling with current workloads may want to consider strengthening their vulnerability management programs with proper vulnerability intelligence.”