Sophos XDR: Threat hunting through the entire security ecosystem
Almost a decade ago, ransomware started becoming a prominent consumer problem, locking computers and threatening users with fines and jail time for supposedly downloading unlicensed software or images of child sexual abuse. Not long after that cyber criminals switched to ransomware that actually encrypted users’ files, and then pretty quickly realized that companies make for much more profitable victims than consumers.
As tech providers and security companies found ways to prevent the malware from being delivered via email, malicious downloads or similar methods, ransomware gangs’ next “big” adaptation was switching to deploying ransomware manually after breaching organizations and “planting” the malware far and wide across their network and endpoints.
This approach is so successful that it has become prevalent, despite companies improving their cyber hygiene, general defenses, and detection capabilities.
Still, I believe that the main reason why ransomware has become such a massive problem is that there will never be a shortage of potential targets and likely victims.
The public mostly hears about the ransomware attacks that affected huge enterprises, government and law enforcement agencies, or companies in critical sectors such as healthcare or energy, but ransomware gangs go after medium and small companies in a wide variety of industries with equal zeal (though they may ask for more reasonable – but still substantial – sums).
Consequently, that worn-out maxim about an(y) organization getting hit with a cyber attack being a matter of “when,” not “if,” has become a universal truth – especially when you add all the other types of cyber attacks in the mix.
Everyone’s a target, but not everybody has to become a victim
Defenders know that preventing each and every attack is impossible, so the additional goal is to minimize attackers’ dwell time, in the hope that the worst outcomes can be avoided.
The details of a recent engagement Sophos’ Rapid Response team was involved in is a good example of how defenders can gain the upper hand.
The (suspected ransomware) attackers compromised a large enterprise’s Exchange server using the recent ProxyLogon exploit, and over a two-week period, they stole Domain Administrator account credentials, moved laterally through the network, compromised domain controllers, established footholds on several machines, deployed a commercial remote access tool to retain access to them, and delivered malicious programs.
The attackers moved slowly, performing only a small number of actions each day in an effort to fly under the radar but, ultimately, their use of an unusual combination of commercial remote management tools is what made security products and the defenders take notice.
“It pays dividends to recognize the hallmarks of an active attack, even if the attackers are using tooling you’re unfamiliar with,” Andrew Brandt, Principal Researcher for Sophos, pointed out.
“Detecting the launch of Cobalt Strike in memory is just one such hallmark and helped convince the customer that a serious (potentially very costly) attack was actively underway even though we didn’t observe many of the other common indicators of an attack, such as widespread use of RDP over a prolonged period of time, which would have appeared in log entries.”
Sophos XDR: Widening the aperture for threat hunting
It goes without saying that red flags such as these are practically impossible for human security operators to notice without the right technological solutions in place.
Sophos’ Rapid Response team had, among other things, the new Sophos XDR solution at their disposal – an industry-first (and so far only) extended detection and response solution that synchronizes native endpoint, server, firewall, and email security.
Sophos XDR gathers relevant sensory information from the organization’s entire IT environment and security ecosystem and allows threat hunters to view the complete picture and detect and inspect clues that may otherwise go unnoticed.
The solution relies on the industry’s richest data set: Sophos’s cloud-based data lake, which host critical information collected from Intercept X (endpoint protection for workstations), Intercept X for Server (endpoint protection for servers), Sophos Firewall (firewalls with synchronized security built in), and Sophos Email (AI-powered cloud email security).
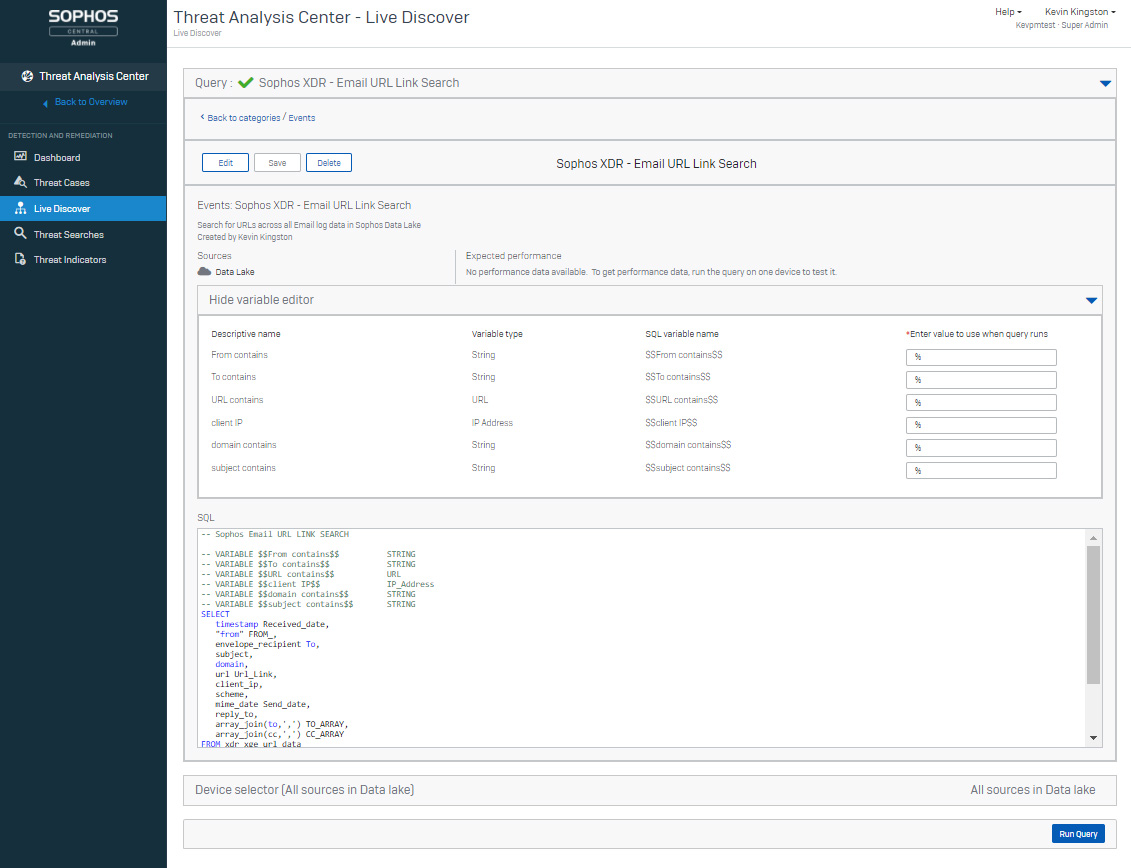
“Within that data lake, we enrich the collected data with threat intelligence (from Sophos Intelix), and we’re able to run AI models against that data to drive detections, as well as some automation. We deliver that information to security operators and practitioners, and we do that through a language we call Live Query,” Dan Schiappa, Chief Product Officer at Sophos, explained.
Testing to get it right
Before making Sophos XDR widely available, the company mounted an early access program purely through the APIs associated with it.
“Part of the Sophos XDR value proposition is that we don’t try and gather every bit of data, but instead only the right data – the data that helps the AI engines come to conclusions. By having that API-enabled early access, we were able to fine-tune that,” Schiappa shared.
Sophos XDR, Sophos EDR (which has been recently equipped with scheduled queries and customizable contextual pivoting capabilities), and the rest of its enterprise security solutions are inherently part of the company’s adaptive cybersecurity ecosystem (ACE), but the platform also has open APIs and powerful integrations so that third parties can participate in and take advantage of it, even if they don’t use Sophos’s products.
“They can pull data out of the data lake and they can provide data into the data lake. They can become part of an automated playbook for response that the security operators will have insight into,” he explained.
The data lake hosts 7 days of EDR-delivered data and 30 days of XDR-collected data. There is also 90 days of granular data stored on endpoints and servers, and this allows users to perform queries to see what’s happening in real-time on those devices.
Building a community of defenders
Sophos XDR can be used by seasoned security operators, but it’s also intuitive enough to be used by those who are just starting that journey or are an IT administrator and the designated security practitioner for a smaller company.
No matter their level of expertise, they can all take advantage of canned queries created by Sophos’s threat hunters, the queries created by threat hunters from other organizations participating in the ACE, and the solution’s query pivot capability.
“That’s one of the things that we’re really excited about: we have a community forum where customers can post queries that they found to be very helpful, and those can be simply cut and pasted into one’s product. The goal is to leverage the expertise of security practitioners and drive that into the community,” Schiappa added.
Finally, those who simply don’t have enough manpower or capabilities on their SOC team can outsource the work to the Sophos Managed Threat Response service, which leverages all the same capabilities.