Application level data protection hindered by misperceptions and complexities
Companies plan to take extensive actions in the next 12 months to address a broad concern for sensitive data being unprotected in use at the application layer, Entrust and Prime Factors reveal.
Results from a recent survey of 600 IT professionals across the US and the UK convey that most companies are taking a variety of actions related to data protection. However, many companies do not address data protection in the applications they control, instead relying on data-at-rest encryption techniques which generally do not protect data-in-use.
Companies broadly concerned with application level data protection
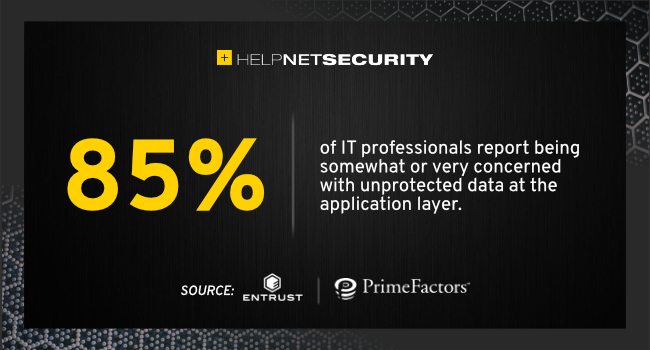
Most companies appear to be broadly concerned with protecting data beyond when it’s at rest, with 85% of respondents reporting being somewhat or very concerned with unprotected data at the application layer. Yet the survey finds that only 24% of companies are employing techniques that protect data in the applications they control.
Respondents did indicate considerable near-term action plans to address protecting data at the application layer – with 96% of respondents stating that they have plans to add application-level data protection functionality within the next twelve months. Encryption, data masking, security audit logging, and tokenization were among top solutions listed by respondents.
However, respondents also expressed broad concern for the complexity of implementing these types of data protection. When asked to list their top three challenges in implementing application-level data protection, no single answer was chosen by a majority of respondents, with answers ranging across seven different challenges reaching at least a 25% response rate.
Cryptographic key management as the highest challenge
Overall, the highest ranked challenge in applying data protection in applications was related to cryptographic key management. When asked what about cryptographic key management was most challenging, the number one answer was ‘generating and storing cryptographic keys securely’. Furthermore, 98% cite using Hardware Security Modules (HSMs) to support encryption in applications.
“Organizations can no longer afford to underestimate or poorly implement application-level encryption,” said John Grimm, VP of Strategy at Entrust.
“Whether organizations are managing fully automated, high-volume applications or tightly supervised, low-volume applications, it’s imperative that business leaders and IT teams prioritize deploying application-level encryption and data protections.”
“Companies tend to focus on securing data-at-rest, because it’s traditionally been easier to implement,” said Justin Teitt, COO of Prime Factors.
“However, these solutions are not designed to address protecting data once it leaves its storage location. This is clearly an area of growing concern, however the perception that protecting data at the application layer is too challenging still lingers.”