Manage and monitor third-party identities to protect your organization
SecZetta shared a research that demonstrates a clear misalignment between the strategies organizations currently use and what is actually required to protect them from cyberattacks due to third-party vulnerabilities.
Monitor third-party identities and non-human workers
At a time when cyberattacks are increasing in size, frequency, and impact, this research found most organizations are not taking the necessary steps to manage and monitor the lifecycle of their third-party identities, making them more vulnerable to cyber incidents. To strengthen cybersecurity programs and better manage identity lifecycles, including third-party and non-human workers, organizations need stronger third-party identity management strategies and solutions.
The research found 78% of organizations report it’s likely or extremely likely they have multiple identity records for a single third-party individual or organization. As a result, organizations may find themselves relying on inaccurate, outdated, or conflicting data, with third-party workers associated to projects they are no longer working on and to which they no longer have legitimate access needs. The existence of multiple active identities jeopardizes an organization’s compliance posture and increases susceptibility to security breaches.
A majority of organizations are concerned about over-permissioned and under-used identities, with 73% being highly or moderately concerned with third-party individuals, service accounts or administrators that have unnecessarily high, static, or standing permissions and authorization levels. This concern is justified given these permission-and entitlement-related threats are known to be leveraged in actual attacks and breaches. Reevaluation of access is typically triggered by a change in role, per project or on a time-based cadence.
When it comes to processes that mitigate third party individual and vendor risks, 53% of organizations are identity proofing and verifying third-party individuals and organizations before granting them access to company assets, reinforcing the need for organizations to invest in third-party identity risk solutions that provide a single identity authority prior to granting access.
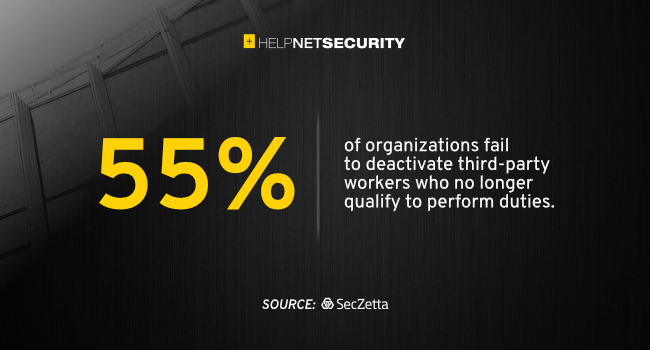
But once you’re in, you’re in… an alarming 55% of respondents fail to deactivate third-party workers who no longer qualify to perform duties. Access to data and systems for this high-risk population often extends beyond project assignments or contract employment with an organization. The implications of this finding are huge since most breaches are found to be the result of compromised credentials. In many ways this equates to “leaving the doors and windows unlocked.”
The importance of risk scoring third-party individuals
Over 92% of organizations believe it is critical or very important to risk score third-party individuals and 89% believe the same for third party organizations, relying upon traditional HR processes like background screening designed to onboard new employees. These tools are ineffective at managing their growing number of third-party non-employees, which includes non-human worker identities such as bots, RPAs and IoT devices, which oftentimes can outnumber an organization’s full-time employee base.
Surprisingly, only 20% of organizations plan to increase spend in the area of third parties, reinforcing the disconnect between the recognized need for improvements in their third-party identity management programs and actions to mitigate risk and reduce exposure to cyberattacks and breaches.
“The biggest security blind spot for the majority of organizations is the network of agencies, partners, suppliers, contractors and companies with whom they not only do business, but who are given access to data and systems,” said David Pignolet, CEO of SecZetta.
“It is an essential security best practice to apply the same level of diligence to the third-party worker population as organizations do their full-time employees. Organizations need to execute risk-based third-party identity management strategies at every stage of the worker lifecycle from proper onboarding to verification and routine auditing, to the eventual offboarding and deprovisioning of a third party’s access.”
The complexities of identity management require increased investment in the right tools and services, like third-party identity lifecycle management, to improve the operational efficiencies and reduce the cost and risk of managing the dynamic, higher-risk relationships with third-party individuals and organizations.