ThreatModeler 7.0 brings AI to threat modeling
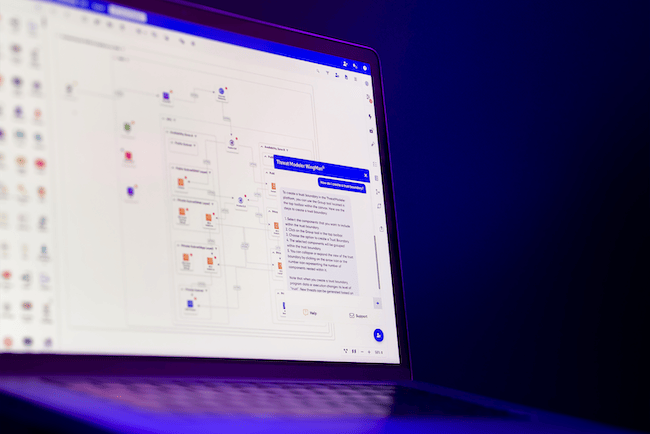
ThreatModeler released ThreatModeler, Version 7.0, bringing several new capabilities, including ThreatModeler WingMan (AI assistant), to help streamline the threat modeling process for software security and DevOps teams.
ThreatModeler 7.0 enables faster and more consistent threat modeling with features such as intelligent embedded machine learning and AI, increased real-time collaboration, customizable risk analysis and a raft of enterprise-grade features for organizations with complex multi-tier environments and large developer and security teams.
Introducing ThreatModeler WingMan. Key patented advances in technology include the integration of AI directly into the toolset, which builds on the vision of “one-click” threat modeling. ThreatModeler WingMan, a new AI assistant, is now embedded directly into the ThreatModeler platform. It leverages ThreatModeler’s patented rules engine and learning module and can include organizational customizations.
WingMan was designed as a way of making Threat Modeling more user-friendly using probabilities and the dynamics of the app being modeled, thereby freeing up time for developers and security teams to focus on more strategic security analysis and process development.
ThreatModeler 7.0 also brings real-time collaboration to DevSecOps teams. Modern DevSecOps practices within large organizations focus on integrating security into a continuous cycle of integration, delivery, and deployment in complex multi-tier environments that include applications, cloud infrastructure, and cloud deployments.
Together, the ThreatModeler platform, IaC-Assist, and Cloud Modeler tools allow any organization to collaborate, review, and ensure they have a complete view of their active threat surface — in real-time. The level of automation and integration into code repositories such as GitHub ensures the most up-to-date security requirements, mitigations, and controls are in place, as well as full audit and compliance capabilities.
ThreatModeler’s IaC-Assist tool allows developers to see changes and updates to GitHub-committed threat models as they progress through the design phases and further revisions — saving time and resources that would otherwise be spent checking differences manually.
Alongside several new enterprise-grade features, ThreatModeler 7.0 introduces a unique Custom Risk Calculation capability. This feature allows software dev and security teams to make more informed assessments of their threat models at a singular and global level, giving complete flexibility to ensure they triage and prioritize their entire attack surface using their organizational criteria.
Additionally, active features such as real-time version control spanning the entire multi-tier environment allow for comparison between different versions of threat models to see how the attack surface has evolved and whether threats are increasing or decreasing — giving a true, real-time view of threat drift.
“ThreatModeler 7.0 sets the bar higher by bringing AI to threat modeling,” said Archie Agarwal, CEO of ThreatModeler. “Our WingMan technology makes it so much easier for developers, with little or no knowledge of security, to build their threat models and incorporate security at the design phase. The platform also provides real-time collaboration and enterprise features to achieve the level of scalability, automation and integration to build more than 100,000 threat models with over 10,000 concurrent users. This is unique to ThreatModeler and essential for teams working toward secure-by-design principles across the whole of their multi-tiered environments.”
With the combination of the technical capabilities of IaC-Assist and collaborative enhancements of Version 7.0, ThreatModeler is further advancing secure-by-design principles to provide actionable insights through continuous monitoring so DevOps teams can detect and remediate security flaws before they become code vulnerabilities.
By enabling developers to understand the full scope of their code, ThreatModeler’s capabilities simultaneously minimize risk and ensure sufficient compliance and governance protocols post-deployment.