Acrobat Reader zero-day exploited in the wild for many months
Unknown attackers have exploited a zero-day Adobe Acrobat Reader vulnerability since November 2025 and possibly even earlier, security researcher Haifei Li has discovered.
PDF files carry the exploit
Haifei Li is one of the creators of EXPMON, a sandbox-based cybersecurity system for detecting advanced file-based exploits. It does so by analyzing suspicious files submitted through its public web interface or API.
“Just few weeks ago, on March 26, someone submitted a PDF sample to EXPMON. The sample, while named as ‘yummy_adobe_exploit_uwu.pdf’ by the [unknown] submitter, triggered one of EXPMON’s advanced ‘detection in depth’ features,” Li explained in a post published on Tuesday.
The same sample was submitted a few days before to VirusTotal, he noted. Another security researcher flagged a variant of the sample on VirusTotal, as well, and that one was first submitted on November 28, 2025.
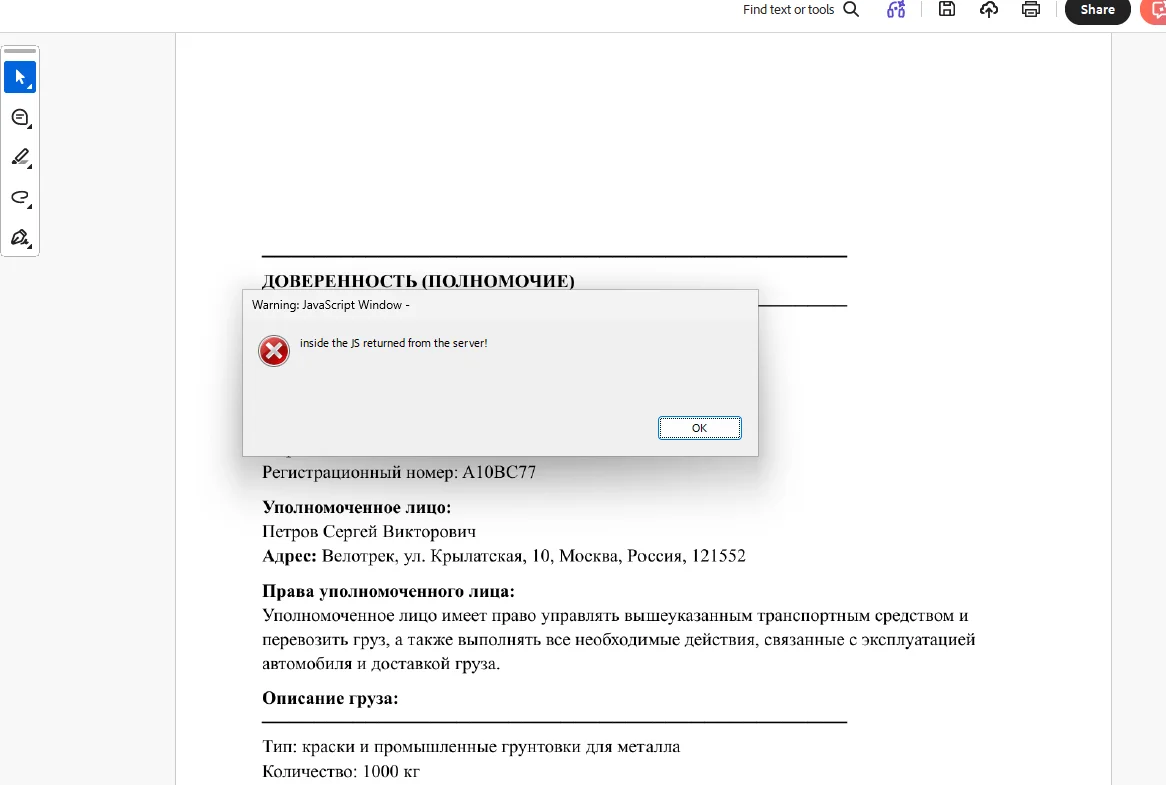
Li’s analysis of the first PDF sample revealed that once opened, the file attempts to execute the heavily obfuscated JavaScript code included in the file.
The script collects various information from the local system (language settings, OS version, the Adobe Reader version number, and the local path of the PDF file) and sends it to an attacker-controlled remote server.
It’s also capable of delivering and launching additional remote code execution or sandbox escape exploits fetched from the attacker-controlled remote server. Unfortunately, when Li analyzed the sample, the server did not deliver any exploit.
“This could be due to several factors: for instance, the attacker’s server might have ‘blocked’ my IP address, or perhaps I needed to provide specific local information to satisfy the server’s conditions. This strongly resembles an advanced fingerprinting attack,” he pointed out.
Test proved that the remote server can deliver and launch additional exploits (Source: Haifei Li)
Malware researcher Giuseppe Massaro analyzed both samples, and noted that both PDFs display Russian-language documents (rendered as images) as visual decoys, and the content – gas supply disruption and emergency response – suggests that the intended targets are Russian-speaking, likely in government, energy sector, or infrastructure organizations.
What to do until a fix is released
Li says that the booby-trapped PDF files will launch the exploit when opened, and confirmed that it works on the latest Acrobat version available.
He notified Adobe of his findings, but the company has yet to push out security updates that fix the exploited vulnerability.
In the meantime, users should avoid opening PDF files sent by untrusted parties. Security teams can block the two attacker-controlled servers/IP addresses (169.40.2.68 and 188.214.34.20). Better yet, they should block all http/https traffic that has the “Adobe Synchronizer” string in the User Agent field, Li advised.
Massaro also advised security teams to monitor for specific changes/actions performed on endpoints (e.g., the AdobeCollabSync.exe making external network connections, and PDF JavaScript calling the RSS.addFeed() or util.readFileIntoStream() APIs).
We’ve reached out to Adobe for more information, and we’ll upate this article when we hear back from them.

Subscribe to our breaking news e-mail alert to never miss out on the latest breaches, vulnerabilities and cybersecurity threats. Subscribe here!