Intruder expands cloud security with agentless container image scanning
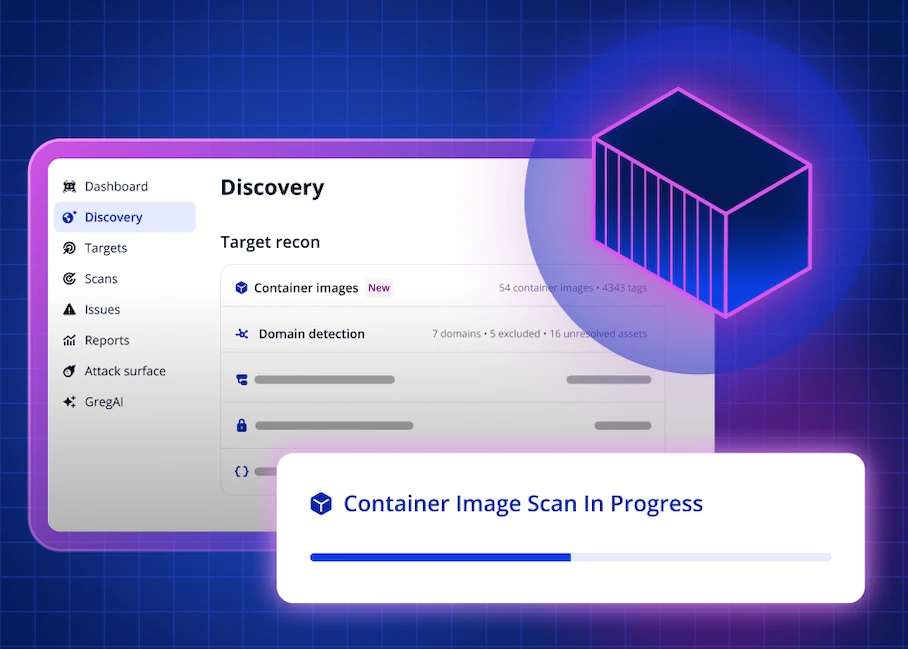
Intruder has announced the release of Container Image Scanning, a new upgrade to its cloud security capabilities that automatically scans container images for vulnerabilities, granting customers actionable insight into container risk without deploying and maintaining scanning agents across their estates.
Leveraging existing integrations with major cloud providers, Intruder supports Amazon Web Services Elastic Container Registry, Google Cloud Artifact Registry and Azure Container Registry. New images and updated versions are scanned daily for vulnerabilities, and users can view results in a single, prioritized list alongside other vulnerabilities, attack surface issues and misconfigurations detected by Intruder.
The update is available for all platform users across Cloud, Pro and Enterprise tiers as well as in the free trial. New customers will require additional setup when adding cloud integrations.
Key benefits include:
- No agents required: Using registry level integrations with cloud providers, customers won’t have the operational overhead associated with deploying agents to nodes, maintaining and debugging them.
- Detection before execution: Unlike agent based approaches, registry level scanning allows customers to detect issues before the image runs in production.
- Noise reduction: Rather than scanning every image in a registry, Intruder uses tags to focus on images that are actually in use across your cloud environments — cutting out noise from old, unused, or deprecated images and surfacing only the risks that matter.
- Coverage across all environments: Agent-based configurations are commonly used in environments like Kubernetes, but containers are also used across many components in cloud infrastructures, such as Functions as a Service (AWS Lambdas), Containers as a Service (AWS ECS), or directly inside virtual machines that also need to be scanned to avoid risks.
- Managed service image scanning: Coverage extends to images deployed to managed container services, where customers don’t have access to the underlying nodes with those services and as a result, couldn’t previously deploy an agent.
As part of the wider shift to cloud infrastructures, a large and growing proportion of digital workloads now occur on containerized, cloud-native platforms with the total market growing 33.5% per year (Grand View Research). However, those workloads face unique security challenges that leave them vulnerable.
Businesses building and deploying applications in containers often have limited visibility into vulnerabilities inside their container images. This means issues such as vulnerable open source packages, outdated dependencies, and known Common Vulnerabilities and Exposures (CVEs) are often left undetected. This leaves a major gap in attack surface coverage for modern, containerized environments. The problem is only growing worse as containerized infrastructure becomes more common while outdated, agent-based solutions are often complex to configure and maintain.
“Containerized environments are everywhere and security solutions need to adapt accordingly,” said Andy Hornegold, vice president of product at Intruder. “Containerized environments are a big, complicated attack surface and this release extends our attack surface and cloud coverage into one of the most critical parts of modern infrastructure, giving teams continuous visibility into container vulnerabilities with minimal effort and strong signal-to-noise control.”