Phishers sneak through using GitHub and Jira’s own mail delivery infrastructure
Attackers are abusing the notification systems of SaaS platforms like GitHub and Jira to send phishing and spam emails, Cisco Talos researchers are warning.
“Because the emails are dispatched from the platform’s own infrastructure, they satisfy all standard authentication requirements (SPF, DKIM, and DMARC), effectively neutralizing the primary gatekeepers of modern email security,” they note.
“By decoupling the malicious intent from the technical infrastructure, attackers successfully deliver phishing content with a ‘seal of approval’ that few security gateways are configured to challenge.”
Exploiting GitHub
On GitHub, the attackers are abusing the service’s notification system to deliver malicious payloads.
Since GitHub notifies collaborators of repository activity, by pushing a commit on an existing project, the attackers trigger an automatic email notification to all collaborators. “Because the content is generated by the platform’s own system, it avoids security flags,” researchers noted.
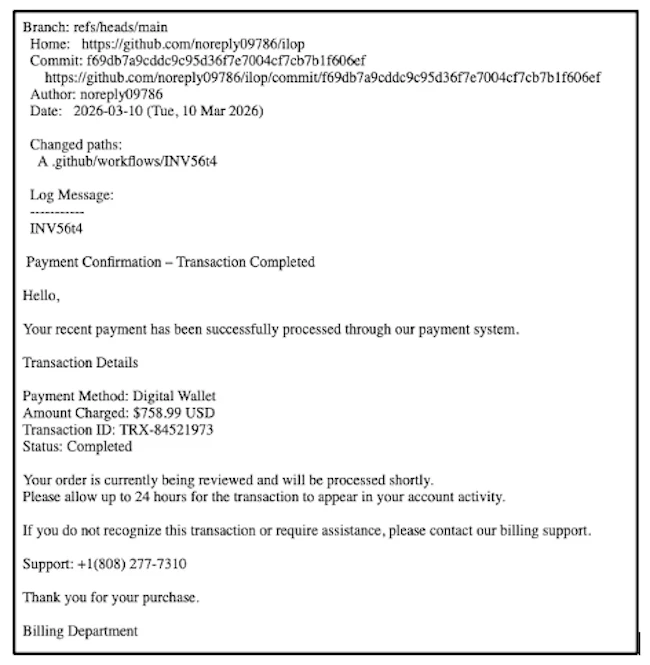
The body of the message (Source: Cisco Talos)
When users create a commit, GitHub provides two text fields: a short summary and a longer description.
The short summary appears first in notification emails, so attackers use it to display a convincing message that grabs attention. The main scam content, such as fake billing details or phishing links, is included in the longer description.
On one observed peak day, about 2.89% of emails sent from GitHub were linked to this type of abuse.
Exploiting Jira
Instead of triggering notifications through repository activity, attackers use Jira’s “Invite Customers” feature to send phishing emails that will bypass email security protections.
They register a Jira account, create a new Service Management project and set a legitimate looking name for it, then place their malicious content (e.g., a fake alert) into the Welcome Message or Project Description field.
The attackers then use Jira’s built-in Invite Customers feature, enter the victims’ email addresses, and Atlassian’s backend assembles the email by injecting the attacker’s field values into its own trusted template. The result is a professionally formatted “Service Desk” notification, complete with Atlassian’s own branding footer.
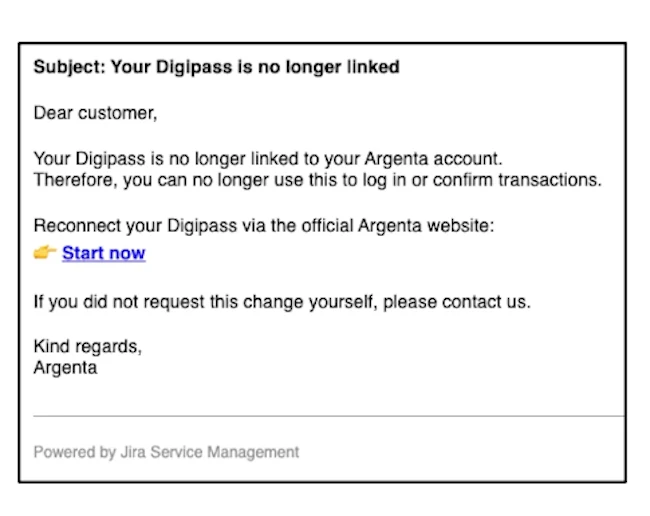
The malicious Jira “notification” (Source: Cisco Talos)
By placing malicious content in fields such as the welcome message or project description, it is automatically included in system-generated emails.
Because the malicious message is sent within Atlassian’s cryptographically signed templates, they are less likely to be flagged by email security solutions. Also, as Cisco Talos pointed out, Jira notifications are expected in corporate environments (including by employees) and rarely blocked.