A study of 1,000 Android apps finds a privacy policy logging gap
Android developers write log statements for the same reasons they always have: debugging crashes, tracing performance issues, and understanding how features behave in production. Legal and privacy teams, working from templates and regulatory checklists, draft policies describing what the app collects from users. These two workflows rarely intersect inside the same company. A new study of 1,000 Android apps shows what that disconnect looks like at scale, and the gap has implications for GDPR and CCPA exposure.
What the researchers found
Researchers from Rochester Institute of Technology, Ontario Tech University, and the University of Waterloo analyzed privacy policies and runtime logs from 1,000 Android apps across 43 categories. Most apps published a privacy policy. Fewer than one in three of those policies mentioned logging practices at all. Among policies that did reference logging, roughly a quarter used vague or generic language that gave users little sense of what data was being captured.
The alignment numbers are where the story gets uncomfortable for compliance teams. Out of 1,000 apps, just four had privacy policies whose disclosures matched the types of sensitive data found in their logs. For IP addresses, around three-quarters of observed leakages were undisclosed in the corresponding privacy policy. For device manufacturer and model identifiers, the figure climbed to nearly all of them.
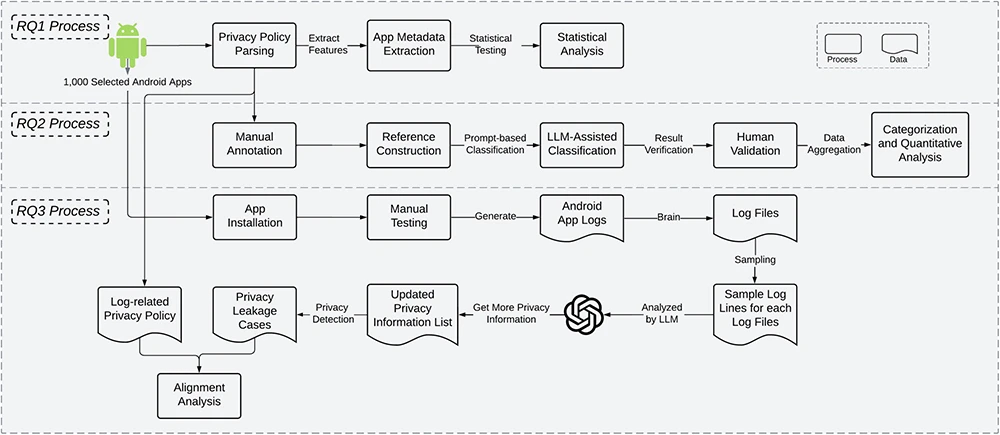
Overview of the study
An engineering and legal workflow problem
The study points to a pattern worth attention. Debugging and maintenance were cited as the purpose behind roughly a quarter of log-related policy statements. Diagnostic data appeared as a disclosed content type far less often. Teams acknowledge logging for debugging purposes in the abstract, yet rarely enumerate what diagnostic data actually gets written.
This reflects how the work is divided in most organizations. Engineers add log statements during feature development and bug fixes, often using third-party SDKs for crash reporting, analytics, and ad attribution. These SDKs pipe log data to external servers by default. Legal teams drafting privacy policies work from abstract data categories and regulatory language. The path from a new Log.d() call to a policy update passes through no formal review gate in most shops.
Why this matters under GDPR and CCPA
Log data routinely contains IP addresses, device identifiers, email addresses, location coordinates, and user names. Under GDPR, these qualify as personal data, which triggers notice obligations under Articles 13 and 14. CCPA imposes similar disclosure requirements for categories of personal information collected. A privacy policy that omits logging practices leaves the organization exposed when regulators or plaintiffs ask what data left the device and where it went.
The third-party dimension compounds the risk. Crash reporting services, analytics providers, and advertising SDKs are often the downstream consumers of log streams. Each represents a processor relationship that requires disclosure. When the log pipeline is invisible to the privacy team, those relationships go undocumented.
Practical steps for IT and compliance teams
A few controls close much of the gap:
Audit log output at the CI stage. Simple pattern matching for email formats, IP addresses, coordinates, and known identifier fields catches most high-risk leakage before release. The study found that even basic keyword detection, extended with LLM-assisted expansion, surfaced widespread exposure.
Include logging in privacy impact assessments. PIAs focused only on database schemas and API payloads miss the log pipeline entirely. Add a review step that examines what the logging framework captures in production builds.
Inventory third-party SDKs by data type. For each SDK that receives log data, document the categories of information transmitted and confirm those categories appear in the privacy policy.
Apply retention limits and redaction to log streams. Many logged identifiers serve no operational purpose after a short debugging window. Automated scrubbing at the collection layer reduces both compliance exposure and incident response scope.