FreeScout vulnerability enables unauthenticated, zero-click RCE via email (CVE-2026-28289)
A newly discovered vulnerability (CVE-2026-28289) in the open-source help desk platform FreeScout could allow attackers to take over vulnerable servers by sending a specially crafted email to a FreeScout mailbox.
CVE-2026-28289 exploitation
FreeScout is a free, open-source help desk and shared inbox system used by businesses or teams to manage customer support conversations in one place.
It is built with PHP (Laravel) and MySQL, and it’s designed to be self-hosted – either on-premises, on a cloud server, or a virtual private server.
CVE-2026-28289 is a bypass of the patch for CVE-2026-27636, which was fixed in FreeScout v1.8.206 and stemmed from its file upload restriction list not including .htaccess or .user.ini files.
(.htaccess files are configuration file used on Apache-based web servers to manage website behavior on a per-directory basis, and .user.ini files allow users to change the configuration of PHP on a per-app and per-directory basis.)
“On Apache servers with AllowOverride All (a common configuration), an authenticated user can upload a .htaccess file to redefine how files are processed, enabling Remote Code Execution,” it’s been explained.
OX Security researchers found that the fix for CVE-2026-27636 attempts to prevent dangerous file uploads by appending an underscore to the file extension when a filename either uses a restricted extension or begins with a period (‘.’).
“During code review, we found a way to bypass this filename validation by prepending a Zero-Width Space character (Unicode U+200B) to the filename,” they shared.
“Because U+200B is not treated as visible content during the initial check, it allows a filename to bypass the validation that blocks names starting with ‘.’ Later in the processing chain, the U+200B character is stripped, causing the file to be saved as a true dotfile, despite having passed the earlier validation.”
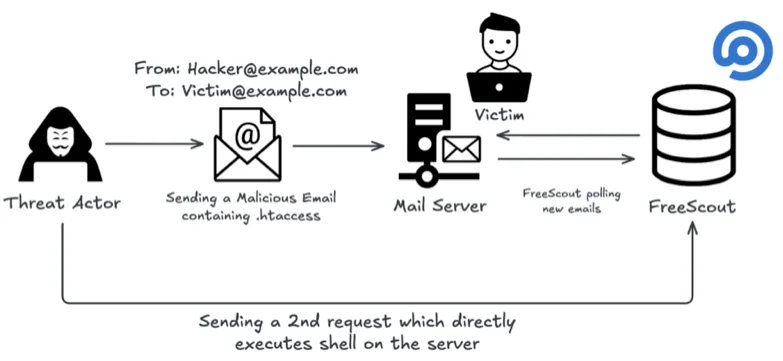
They also devised a way to exploit CVE-2026-28289 remotely, without authentication or any required user interaction, by simply sending an email carrying a malicious .htaccess file and a webshell to a mailbox configured in FreeScout.
How the attack unfolds (Source: OX Research)
The malicious payload is written to disk on the FreeScout server and, since the location where it’s saved is predictable, attackers can access it on the server’s web GUI and use it to execute commands remotely.
What to do?
According to OX Security researchers, the Shodan search engine currently shows around 1100 publicly exposed FreeScout instances. Whether all of them are vulnerable to CVE-2026-28289 is unknown.
But those that are risk system takeover and data exfiltration (helpdesk tickets, mailbox content, etc.). Attackers could also use the compromised system to move laterally through the same network.
“Our investigation confirmed exposed FreeScout deployments across public health institutions, technology providers, financial services platforms, and news organizations. We are intentionally withholding identifying details to avoid increasing risk to affected parties,” the researchers added.
If you’re using FreeScout for your help desk needs, are running the instance on Apache Server, and you have not updated your instance since last week, you should get on it right away and upgrade to v1.8.207.
The researchers also advise disabling AllowOverrideAll in the Apache configuration on the FreeScout server.

Subscribe to our breaking news e-mail alert to never miss out on the latest breaches, vulnerabilities and cybersecurity threats. Subscribe here!