Cybercriminals scale up, government sector hit hardest
Government agencies faced the highest volume of cyberattack campaigns in 2025, according to new findings from HPE Threat Labs, which tracked 1,186 active campaigns over the course of the year. The data covers activity observed between January 1 and December 31, 2025, and reflects a broad mix of sectors and attack types.
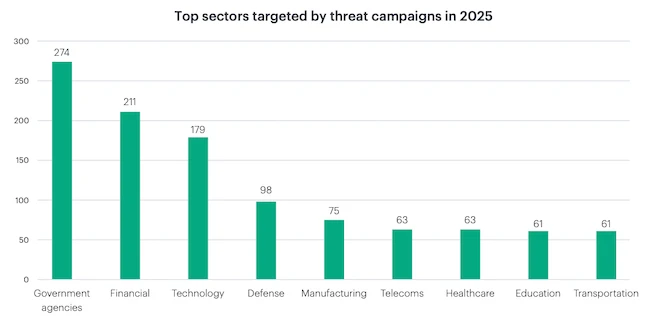
Top sectors targeted by threat campaigns in 2025 (Source: HPE)
AI and automation drive faster, more powerful cyberattacks
Government agencies were targeted in 274 campaigns, the largest share among all industries. Financial services followed with 211 campaigns, while technology companies accounted for 179. Defense saw 98 campaigns, and manufacturing recorded 75. Telecommunications and healthcare each logged 63 campaigns, while education and transportation each recorded 61.
The activity was spread across industries that handle sensitive data, critical infrastructure, or large-scale operations.
Attackers have also introduced new methods to boost speed and impact. Some campaigns relied on automated, assembly line workflows, often coordinated through platforms like Telegram, to extract stolen data in real time.
Others used GenAI to create synthetic voices and deepfake videos for targeted vishing attacks and executive impersonation scams. In one case, an extortion group even conducted market research on VPN vulnerabilities to refine its intrusion tactics.
Ransomware leads threat activity
Ransomware accounted for 22% of campaign types. Infostealer activity represented 19%, followed by phishing at 17%. Remote Access Trojans (RAT) made up 11%, while malware accounted for 9%.
Researchers identified 147,087 malicious domains and 65,464 malicious URLs, along with 57,956 malicious files and 47,760 IP addresses tied to threat activity. Attackers also exploited 549 distinct vulnerabilities during the year.
Telemetry from a global deception network recorded 44.5 million connection attempts from 372,800 unique source IP addresses. Of those, 36,600 requests matched known attack signatures, originating from 8,200 distinct source IPs and targeting five destination IPs.
Attack pattern data showed a focus on exposed services and known weaknesses. Digital video recorder (DVR) Shell remote code executions (RCEs) appeared 4700 times, followed by Huawei router exploits at 3490 and Docker application programming interface (API) abuses at 3400.
PHP unit and TP-Link command injections accounted for 3100, while Printer enumeration (IPP) and Realtek UPnP abuses appeared 2700 times.
The most frequently exploited vulnerabilities included CVE-2017-17215, CVE-2023-1389, CVE-2014-8361, CVE-2017-9841, and CVE-2023-26801.