Your APIs are under siege, and attackers are just getting warmed up
Internet-facing systems are handling sustained levels of malicious traffic across APIs, web applications, and DDoS channels. Akamai’s State of the Internet security report places these patterns within the same operating environment, with activity increasing across each area through 2025.
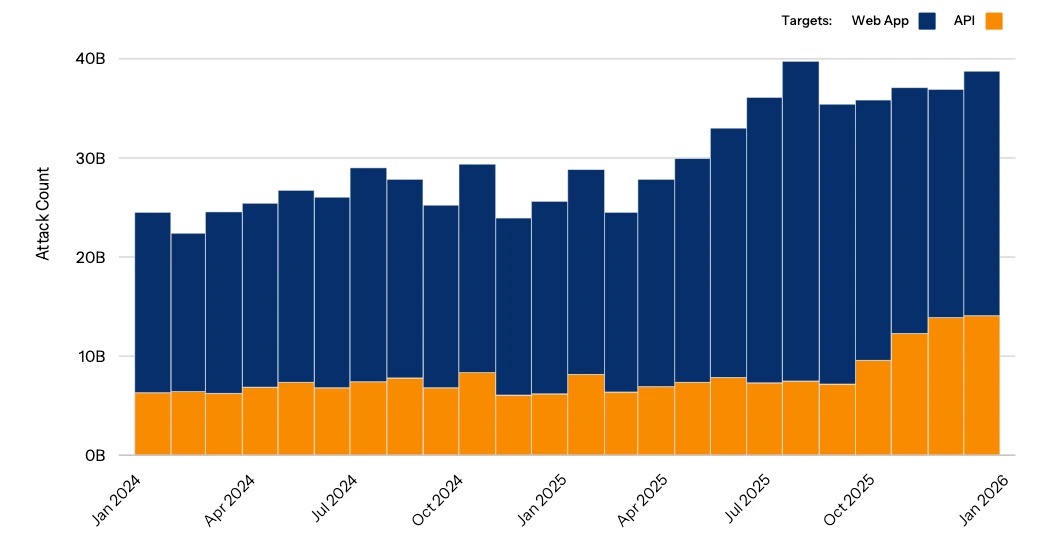
The number of web attacks against apps and APIs continued an upward trajectory from January 2024 to December 2025, demonstrating their prevalence as a major threat to organizations (Source: Akamai)
API activity centers on how applications behave
API traffic continues to expand, and attack activity is rising with it. The average number of API attacks per enterprise per day reached 258 in 2025, compared with 121 in 2024.
Most organizations reported at least one API-related security incident during the year. This places API security within routine operations for many teams.
Attack activity is shifting toward how applications behave during normal use. Behavior-based threats now account for a larger share of API traffic. These threats focus on how requests move through workflows and how systems respond to those requests.
Common weaknesses in APIs remain tied to configuration and access control. Security misconfiguration appears most often in vulnerability data, followed by authorization and authentication issues. Incident data reflects similar patterns, with unsafe API consumption and authentication problems appearing frequently.
“Attackers increasingly focus on degrading performance, driving up infrastructure costs, and exploiting AI-driven automation at scale, rather than seeking headline-grabbing campaigns,” said Patrick Sullivan, CTO of Security Strategy at Akamai. “Automation and AI are making these sophisticated campaigns cheap, repeatable, and fast. And as enterprises invest heavily in AI transformation, attackers are targeting the APIs that power that transformation.”
These conditions place API security within everyday application behavior. Requests that appear normal at first can still expose weaknesses when systems process them.
Sensitive data remains part of API exposure
API environments include large volumes of sensitive data. Each customer manages thousands of APIs that handle this type of information. A portion of these APIs contains security weaknesses, and some of those weaknesses involve sensitive data exposure.
The number of APIs exposing sensitive data has increased over time. This reflects how APIs are used to connect systems and move data between services.
Organizations also report uneven visibility into their API environments. Many maintain an inventory of APIs, and fewer can identify which APIs return sensitive data. This gap places sensitive data within systems that are still being mapped and understood.
Sensitive data exposure remains tied to how APIs are configured and maintained. These conditions extend across development and production environments.
DDoS activity spans multiple layers
DDoS activity continues across application and network layers. Attack campaigns include Layer 3, Layer 4, and Layer 7 traffic within the same operations. This reflects how attackers move across different parts of the stack during a single campaign.
Layer 7 DDoS activity has increased over time, placing pressure on application-facing systems. Network-layer activity continues alongside it, contributing to overall traffic volume during attacks.
Botnet activity supports these campaigns. Variants such as Aisuru and Kimwolf infect large numbers of IoT and Android devices. These devices contribute to the traffic used in DDoS activity.
Industry targeting data places software and SaaS among the sectors receiving sustained DDoS activity across both application and network layers. These environments rely on continuous availability, which places them within the flow of ongoing attack activity.
Web application attacks remain steady
Web application attacks are increasing alongside API activity. Attack volume has grown since 2023, with injection-based techniques remaining part of observed activity. These attacks target application inputs and how systems process data. They remain part of routine traffic across many environments.
Regional data shows continued pressure in APAC, where web application and API attacks reach into the tens of billions over the course of a year. DDoS activity in the region includes both application-layer and network-layer traffic.
These conditions show that attack activity spans regions and systems. Application traffic and network traffic operate within the same environment.