ShipSec Studio brings open-source workflow orchestration to security operations
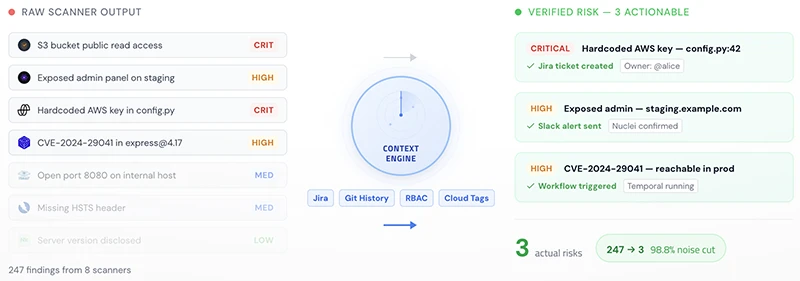
Security teams have long relied on a mix of shell scripts, cron jobs, and loosely connected tools to chain reconnaissance and vulnerability scanning work together. ShipSec Studio, an open-source security workflow automation platform from ShipSec AI, aims to replace that arrangement with a dedicated orchestration layer built specifically for security operations.
What the platform does
ShipSec Studio provides a visual, no-code workflow builder that lets operators connect security tools into automated pipelines without writing glue code. The builder compiles those visual graphs into an executable domain-specific language that a separate worker runtime then executes.
The platform ships with native support for a set of commonly used security tools. On the reconnaissance side, it integrates Subfinder, DNSX, Naabu, and HTTPx for subdomain discovery and service enumeration. For vulnerability and secret detection work, it includes Nuclei and TruffleHog.
Beyond tool execution, the platform includes several orchestration-level features that distinguish it from a straightforward task scheduler. Workflows support a human-in-the-loop pause mechanism that halts execution and waits for operator approval, form input, or manual validation before proceeding. Operators can also embed LLM nodes into workflows to run AI-assisted analysis on tool output, with support for MCP providers as a standardized integration layer. Native CRON scheduling handles recurring scans. A REST API exposes workflow triggering and monitoring for external integration.
Architecture
The platform separates concerns across three planes. A NestJS-based management plane handles workflow compilation, secrets management using AES-256-GCM encryption, and identity. An orchestration plane built on Temporal.io manages workflow state, concurrency, and persistent wait states, providing durability across failures and restarts. A stateless worker plane pulls tasks from Temporal and executes them inside ephemeral containers with per-run volume isolation.
A real-time telemetry pipeline delivers terminal output, events, and logs over server-sent events. The infrastructure stack includes PostgreSQL, MinIO, Redis, Loki, and Redpanda for messaging. The frontend is built on React 19, ReactFlow for the visual canvas, and xterm.js for terminal rendering.
MCP integration extends to a built-in library of servers. AWS CloudTrail, CloudWatch, and filesystem access ship out of the box. AI agents running within workflows can automatically discover and invoke MCP tools through a standardized discovery mechanism.
Deployment
Teams can run the platform entirely on their own infrastructure. A one-line installer handles dependency checks, Docker configuration, and service startup. The project also documents a self-hosted Docker path suited for teams with data residency requirements or air-gapped environments.
Development documentation covers multi-instance setups that allow engineers to run parallel isolated environments on a single machine, each with its own database and Temporal namespace.
ShipSec Studio is available for free on GitHub.

Must read:
- 40 open-source tools redefining how security teams secure the stack
- Firmware scanning time, cost, and where teams run EMBA

Subscribe to the Help Net Security ad-free monthly newsletter to stay informed on the essential open-source cybersecurity tools. Subscribe here!
