TrueConf zero-day vulnerability exploited to target government networks
Suspected China-nexus attackers have leveraged a zero-day vulnerability (CVE-2026-3502) in the TrueConf client application to distribute malware within government networks in Southeast Asia, Check Point researchers discovered.
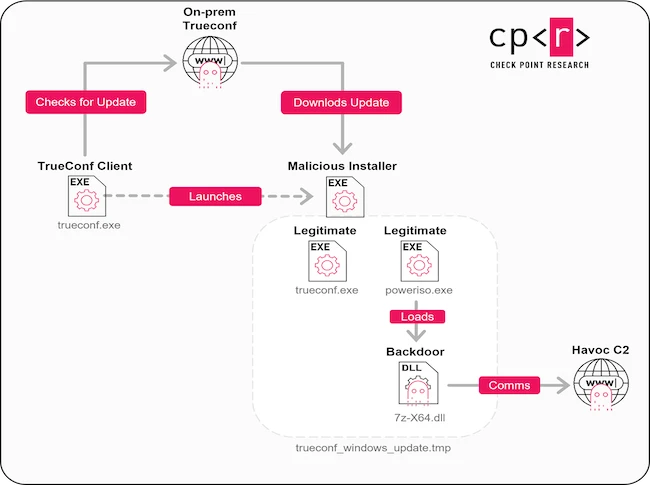
Malicious client update attack chain (Source: Check Point)
Trusted update mechanism turned into attack vector
TrueConf is a videoconferencing platform designed to run on private local networks (LANs) without internet access, which makes it attractive to government departments, defense institutions, and critical infrastructure operators. Consequently, the solution is an attactive target to nation-state threat actors, as well.
This attack campaign did not rely on phishing emails or exposed services. Instead, the attackers sought to compromise software already deployed inside government environments.
CVE-2026-3502 makes the TrueConf client application download updates from a centralized, on-premises server and apply them without verifying the integrity of update packages. Attackers were able to weaponize this by gaining control of the TrueConf servers of some government entities in Southeast Asia.
“The infections began when TrueConf client application launched, probably by a link sent to the target from the attacker. This link launched the already installed TrueConf client and presented an update prompt claiming that a newer version was available,” Check Point researchers explained.
“Prior to the victim’s interaction, the attacker had already replaced the update package on the TrueConf on-premises server with a weaponized version, ensuring that the client retrieved a malicious file through the normal update process,” they noted.
In observed cases, attackers used the update channel to deliver malicious payloads, which were then used to deploy the Havoc open-source post-exploitation framework. Once installed, it enabled reconnaissance, persistence, and communication with command-and-control infrastructure.
Attribution and mitigation
Check Point believes, with moderate confidence, that Operation TrueChaos is linked to a Chinese-nexus threat actor, based on overlaps in tactics, infrastructure, and targeting.
CVE-2026-3502 has been patched in TrueConf Windows client version 8.5.3, released in March 2026. Organizations running earlier versions remain exposed.
Researchers advise organizations to review systems for signs of compromise by focusing on suspicious update behavior and related artifacts.