Apple Intelligence flaw kept stolen tokens reusable on another device
Apple claims that Apple Intelligence, a GenAI service provided on its operating systems, is designed with an extra focus on user security and privacy through a two-stage authentication and authorization system using anonymous access tokens.
However, researchers from The Ohio State University have identified vulnerabilities in this design, demonstrated on macOS 26.0 (Tahoe), that allow attackers to steal and reuse these tokens.
Service infrastructure
The system offloads complex requests to cloud servers using Private Cloud Compute (PCC). This framework utilizes two types of credentials following the Privacy Pass protocol. A device first contacts an identity service to prove it is authentic Apple hardware, which issues a long-lived Token Granting Token (TGT).
This TGT is later redeemed for batches of single-use One-Time Tokens (OTTs) to authorize individual AI requests. To protect privacy, traffic proxies through an Oblivious HTTP (OHTTP) relay that hides metadata such as IP addresses from Apple.
The researchers also found that PCC nodes have TGT validation code, but it is gated behind a flag that defaults to off, so invalid TGTs do not cause requests to be rejected. Apple’s documentation had described this check as reserved for future abuse mitigation.
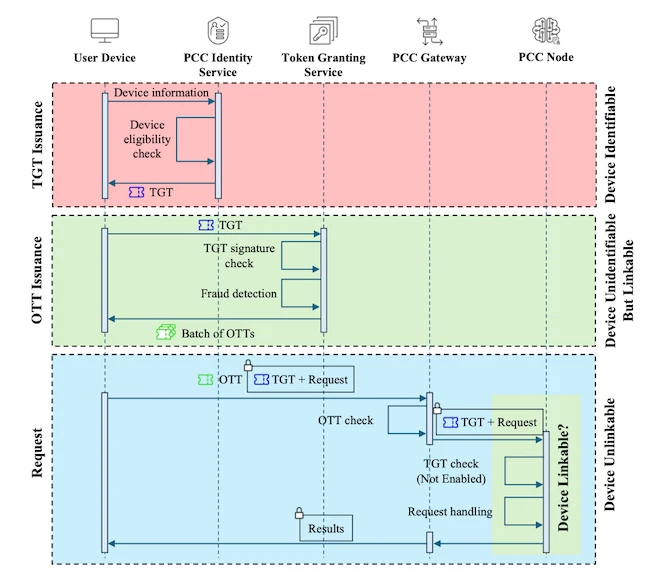
Authentication protocol of Apple Intelligence (Source: Research paper)
Identified vulnerabilities
An investigation into macOS 26.0 revealed that TGTs and OTTs reside in the login keychain in plaintext. This database remains accessible to any application running with standard user permissions. The design prioritizes anonymity by detaching tokens from physical hardware.
Because the system possesses no method to verify which device originally received a token, the credentials function as “bearer tokens.” A person possesses no way to revoke these tokens if a compromise occurs, leaving them valid until they expire several days later.
The Serpent attack
Researchers developed an attack called Serpent to exploit these architectural gaps. This technique breaks the “intended non-transferability of Apple Intelligence credentials” through two distinct phases.
During the extraction phase, malware on the victim’s Mac queries the keychain using the SecItemCopyMatching API or the /usr/bin/security tool. This triggers a system prompt asking the user to “Allow” access. The authors assume the user grants this permission, noting that such prompts are common in normal macOS usage and may appear routine.
Once the malware exfiltrates the tokens to an attacker-controlled server, the disguise phase begins. The attacker overwrites their local keychain with the victim’s tokens. Their device then operates as the victim for subsequent service requests.
Impact and demonstrations
Practical tests on macOS 26.0 confirmed that the Serpent attack bypasses device-level security controls. Researchers used one Mac to send prompts until the service reached its daily rate limit and issued a ban. By importing a victim’s tokens, the banned Mac instantly regained service access.
The study also demonstrated a DoS attack where an attacker consumes a victim’s entire daily allowance. An attacker can repeatedly redeem OTTs using a stolen TGT and discard them without sending an actual prompt. This exhausts the victim’s quota and causes their device to display a warning stating that “Apple Intelligence is currently not available.”
“For an ordinary consumer, this looks more like a service interruption rather than that it has been attacked,” researchers wrote.
Because the OHTTP relay hides IP addresses, the service provider cannot trace this activity back to the attacker. The findings show that the vulnerability makes it possible to create automated clients on platforms such as Linux, potentially enabling the resale of Apple Intelligence as a generic AI service.
Patches and mitigations
Apple assigned CVE-2025-43509 and awarded a bounty following the disclosure of these findings. The macOS 26.2 update moved tokens from the login keychain to the iCloud keychain. Access to this area requires specific permissions that the system kernel checks to block unauthorized applications.
While this change increases the difficulty of token theft but is not a complete fix. The researchers showed the entitlement check can still be bypassed through kernel extensions or memory debugging, and Apple is working on additional patches. They argue that anonymizing identity does not by itself guarantee a secure service and advocate for cryptographic hardware binding as the fundamental solution.