Help Net Security

What CISOs need to do about post-quantum migration in the next 24 months
In this Help Net Security video, Garfield Jones, SVP Global Strategy and Research, QuSecure, lays out what CISOs should do over the next 24 months. A recent Google paper moved …
Why you need BAS and autonomous pentesting together
Most security teams know the drill: A new autonomous penetration testing tool gets deployed, and the first run is genuinely impressive. The dashboard surfaces critical …

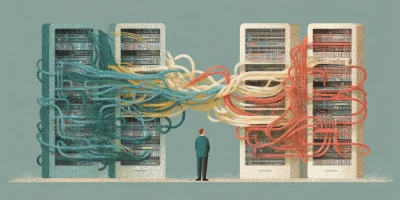
Governing shadow AI without killing innovation
In this Help Net Security video, Alan Snyder, CEO at NowSecure, talks about governing shadow AI without stopping innovation. He frames the problem as two opposing forces. …

Week in review: Infostealer dropped via FortiClient EMS flaw, exploited Trend Micro Apex One flaw
Here’s an overview of some of last week’s most interesting news, articles, interviews and videos: Coinflow CISO on crypto payments security under AI pressure Crypto payment …

Building a risk-based vulnerability management program that scales
In this Help Net Security video, Shankar Somasundaram, CEO at Asimily, explains how to build a risk-based vulnerability program. He notes that vulnerabilities are exploding by …

The alert economy is driving security analyst burnout
In this Help Net Security video, Ido Livneh, CEO of Jazz, explains why security analysts burn out and what leaders can do about it. The cause, he argues, is not long hours but …

Manage machine identities: The hidden privileged access layer you need to manage
Why are machine identities becoming the majority of “things with access”? Every automation, integration, and workload needs a way to authenticate and the right permissions to …

Lessons for organizations from the Verizon 2026 Data Breach Investigations Report
This is my favourite time of the year, not just because spring is here and the promise of summer is on the way. But also, because one of my must reads each year gets …

Boards want cyber risk in dollars, not CVE counts
In this Help Net Security video, Ziv Levi, SVP of Technology at CYE, explains why translating cyber risk into dollars is one of the most pressing tasks for security leaders. …

Week in review: GitHub breached via poisoned VS Code extension, critical NGINX flaw exploited
Here’s an overview of some of last week’s most interesting news, articles, interviews and videos: GitHub, Grafana Labs breaches traced back to TanStack supply chain compromise …

Keepnet contributes voice and SMS phishing data to the 2026 Verizon DBIR
Keepnet, an Extended Human Risk Management (xHRM) platform, today announced that its voice and SMS phishing simulation data contributed to the 2026 Verizon Data Breach …

7 hard truths security pros should know: 2026 DevOps Threats Report
In 2025, trusted Git hosting platforms became a playground for cyber criminals. This is the main conclusion from the latest “DevOps Threat Unwrapped Report 2026” by …
Featured news
Resources
Don't miss
- Critical Ivanti Sentry flaw allows root-level remote code execution (CVE-2026-10520)
- Record Microsoft Patch Tuesday, fresh zero-day
- Every set of AI guardrails can be broken by the right prompt
- The security in smartphones is helping send them to landfills
- Product showcase: Staying ahead of the threat horizon with Aunoo