identity management
Oracle issues emergency fix for pre-auth RCE in Identity Manager (CVE-2026-21992)
Oracle has released an out-of-band patch for a critical and easily exploitable vulnerability (CVE-2026-21992) in Oracle Identity Manager and Oracle Web Services Manager. The …

Why workforce identity is still a vulnerability, and what to do about it
Most organizations believe they have workforce identity under control. New hires are verified. Accounts are provisioned. Multi-factor authentication is enforced. Audits are …

AI agents behave like users, but don’t follow the same rules
Security and governance approaches to autonomous AI agents rely on static credentials, inconsistent controls, and limited visibility. Securing these agents requires the same …

Why boards must prioritize non-human identity governance
Boards of Directors (BoDs) do three things exceptionally well when cyber is framed correctly. They set risk appetite, they allocate capital, and they demand evidence that the …
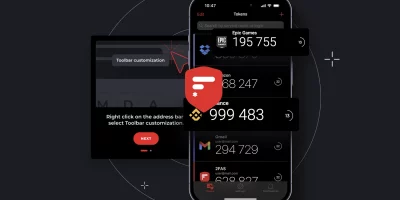
Product showcase: 2FAS Auth – Free, open-source 2FA for iOS
Online accounts usually rely on a password, but passwords alone can be weak if they’re reused, easily guessed, or stolen. Two-factor authentication (2FA) adds a second layer …

AI is flooding IAM systems with new identities
Most organizations view AI identities through the same lens used for other non-human identities, such as service accounts, API keys, and chatbots, according to The State of …

The next big IT security battle is all about privileged access
Leostream predicts changes in Identity and Access Management (IAM) and Privileged Access Management (PAM) in 2026 driven by new realities of cybersecurity, hybridization, AI, …

Passwordless is finally happening, and users barely notice
Security teams know the strain that comes from tightening authentication controls while keeping users productive. A new report from Okta suggests this strain is easing. …

Product showcase: UserLock IAM for Active Directory
UserLock brings modern identity and access management (IAM) to Active Directory, adding granular multi-factor authentication (MFA), contextual access controls, single sign-on …

Treating MCP like an API creates security blind spots
In this Help Net Security interview, Michael Yaroshefsky, CEO at MCP Manager, discusses how Model Context Protocol’s (MCP) trust model creates security gaps that many …

What zero trust looks like when you build it step by step
In this Help Net Security video, Jonathan Edwards, Managing Director at KeyData Cyber, walks us through what practical zero trust adoption looks like in stages. He explains …

The identity mess your customers feel before you do
Customer identity has become one of the most brittle parts of the enterprise security stack. Teams know authentication matters, but organizations keep using methods that …
Featured news
Resources
Don't miss
- ClickFix campaign delivers Mac malware via fake Apple page
- Poisoned “Office 365” search results lead to stolen paychecks
- What vibe hunting gets right about AI threat hunting, and where it breaks down
- Health insurance lead sites sell personal data within seconds of form submission
- Claude helps researcher dig up decade-old Apache ActiveMQ RCE vulnerability (CVE-2026-34197)