strategy
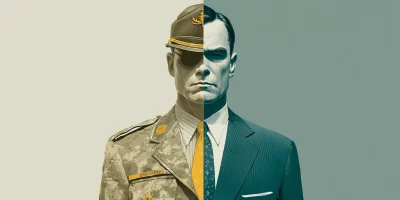
Why ex-military professionals are a good fit for cybersecurity
After years of working as part of a team, many military veterans look for work that still carries meaning, challenge, and purpose. Cybersecurity offers a new way to serve and …

Why cybersecurity hiring feels so hard right now
In this Help Net Security video, Carol Lee Hobson, CISO at PayNearMe, explores the realities behind the so-called cybersecurity “talent gap.” She explains why the issue is as …

Identifying risky candidates: Practical steps for security leaders
Effective insider threat defense begins with candidate vetting. Background checks and reference calls can confirm elements of an applicant’s history, but they rarely surface …

The solar power boom opened a backdoor for cybercriminals
Solar isn’t low risk anymore. Adoption has turned inverters, aggregators, and control software into attack surfaces capable of disrupting service and undermining confidence in …

Building a healthcare cybersecurity strategy that works
In this Help Net Security interview, Wayman Cummings, CISO at Ochsner Health, talks about building a healthcare cybersecurity strategy, even when resources are tight. He …

AI-generated images have a problem of credibility, not creativity
GenAI simplifies image creation, yet it creates hard problems around intellectual property, authenticity, and accountability. Researchers at Queen’s University in Canada …

From theory to training: Lessons in making NICE usable
SMBs may not have big budgets, but they are on the receiving end of many cyberattacks. A new study from Cleveland State University looked at how these companies could train …

Behind the screens: Building security customers appreciate
In this Help Net Security interview, Jess Vachon, CISO at PRA Group, discusses the company’s multi-layered defense against fraud and its commitment to protecting customer …

How to get better results from bug bounty programs without wasting money
The wrong bug bounty strategy can flood your team with low-value reports. The right one can surface critical vulnerabilities that would otherwise slip through. A new academic …

How to succeed at cybersecurity job interviews
Imagine this: you’ve made it through the résumé screen, your skills look solid on paper, and now it’s interview day. The next hour will decide whether you move forward or go …

When loading a model means loading an attacker
You probably think twice before downloading a random app or opening an unfamiliar email attachment. But how often do you stop to consider what happens when your team downloads …

Building a mature automotive cybersecurity program beyond checklists
In this Help Net Security interview, Robert Sullivan, CIO & CISO at Agero, shares his perspective on automotive cybersecurity. He discusses strategies for developing …
Featured news
Resources
Don't miss
- State-backed phishing attacks targeting military officials and journalists on Signal
- Poland’s energy control systems were breached through exposed VPN access
- CISA orders US federal agencies to replace unsupported edge devices
- Ransomware attackers are exploiting critical SmarterMail vulnerability (CVE-2026-24423)
- February 2026 Patch Tuesday forecast: Lots of OOB love this month