
Predicting DDoS attacks: How deep learning could give defenders an early warning
Distributed denial-of-service (DDoS) attacks remain one of the most common and disruptive forms of cybercrime. Defenders have traditionally focused on detecting these attacks …
The fight to lock down drones and their supply chains
Drones have already shown their impact in military operations, and their influence is spreading across the agricultural and industrial sectors. Given their technological …

U.S. Secret Service takes down network of devices threatening government officials
The U.S. Secret Service has broken up a network of electronic devices spread across the New York tristate area that officials say posed an imminent threat to national …
Cybercriminals are going after law firms’ sensitive client data
Regardless of their size, all law firms hold valuable data, including client communications, financial records, and confidential legal strategies. That data has never been …

The unseen side of malware and how to find it
Security teams rely on threat reports to understand what’s out there and to keep their organizations safe. But a new report shows that these reports might only reveal part of …

Old file types, new tricks: Attackers turn everyday files into weapons
Attackers are finding new ways to blend in with everyday business tools, hiding their activity inside formats and processes that workers and IT teams often trust. The latest …

Ransomware, vendor outages, and AI attacks are hitting harder in 2025
Ransomware, third-party disruptions, and the rise of AI-powered attacks are reshaping the cyber risk landscape in 2025. A new midyear analysis from Resilience shows how these …

New threat group uses custom tools to hijack search results
ESET Research has identified a new threat group called GhostRedirector. In June 2025, this group broke into at least 65 Windows servers, mostly in Brazil, Thailand, Vietnam, …

Attackers are turning Salesforce trust into their biggest weapon
Salesforce has become a major target for attackers in 2025, according to new WithSecure research into threats affecting customer relationship management (CRM) platforms. The …

Maritime cybersecurity is the iceberg no one sees coming
Maritime transport, the backbone of global trade, is adapting to shifting economic, political, and technological conditions. Advances in technology have improved efficiency, …

The new battleground for CISOs is human behavior
This article is no longer available. Check out our news from this week here: Week in review: Covertly connected and insecure Android VPN apps, Apple fixes exploited zero-day
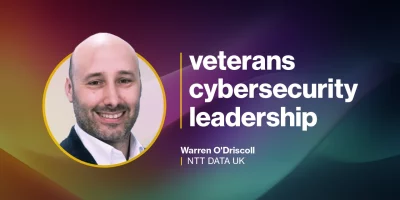
How military leadership prepares veterans for cybersecurity success
In this Help Net Security interview, Warren O’Driscoll, Head of Security Practice at NTT DATA UK and Ireland, discusses how military leadership training equips veterans …
Featured news
Resources
Don't miss
- $20 per zero-day is already the WordPress plugin reality
- Deleted Google API keys keep working for up to 23 minutes, researchers warn
- Meet Fractal, an OS made for microarchitecture reverse engineering
- Microsoft open-sources tools for designing and testing AI agents
- GitHub, Grafana Labs breaches traced back to TanStack supply chain compromise