Defense contractors, manufacturers targeted with malware-as-a-service infostealer
Information stealing FormBook malware is being lobbed at defense contractors, manufacturers and firms in the aerospace sector in the US and South Korea.
Delivery methods
The malware is delivered via high-volume spam campaigns and email attachments that take the form of:
- DOC/XLS files loaded with malicious macros that initiate the download of FormBook payloads
- Archive files containing FormBook executable files
- PDFs containing links to the tny.im URL-shortening service, which point to FormBook executables hosted on a staging server.

The emails are made to look like they are coming from FedEx and DHL (with the PDF attachment), as emails delivering invoices, price quotations or purchase orders (with the malicious-macros-carrying Office files), and payment confirmations and purchase orders (archive files containing malicious executables).
About the malware
“FormBook is a data stealer and form grabber that has been advertised in various hacking forums since early 2016,” FireEye researchers noted.
The malware injects itself into various processes and installs function hooks to log keystrokes, steal clipboard contents, and extract data from HTTP sessions.
It can execute commands from a C&C server, which include updating and removing itself, downloading and executing additional files, rebooting or shutting down the compromised system, clearing browser cookies, and more. It is also capable of taking screenshots, and grabbing passwords from browsers and email clients (Chrome, Firefox, IE, Opera, Thunderbird, Outlook).
It apparently works on all Windows versions, it’s not prone to crashing, and has considerable persistence and anti-malware analysis capabilities. Its communication with the C&C server is encrypted.
“The malware author does not sell the builder, but only sells the panel, and then generates the executable files as a service,” the researchers explained.
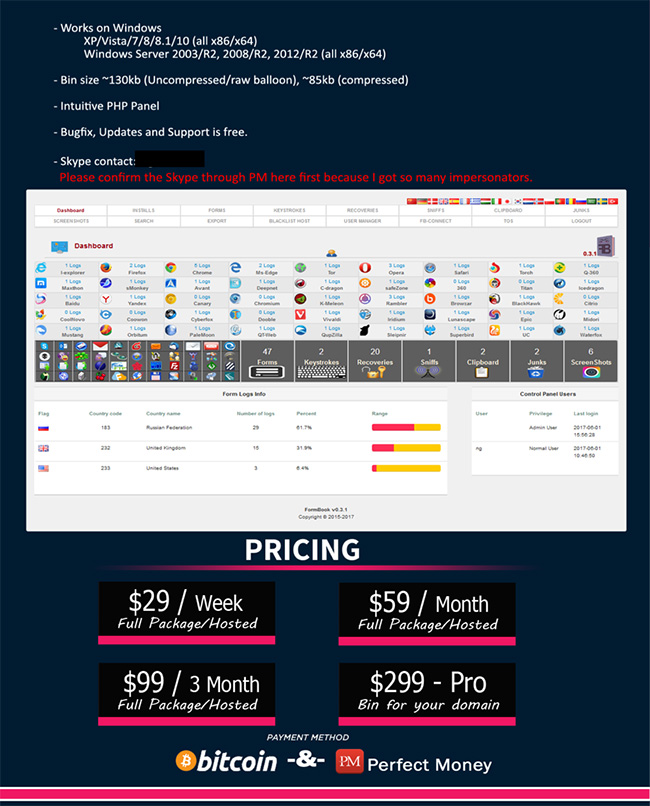
The ads show how costly its use is (i.e. not that costly):
“While FormBook is not unique in either its functionality or distribution mechanisms, its relative ease of use, affordable pricing structure, and open availability make FormBook an attractive option for cyber criminals of varying skill levels,” the researchers concluded.
“In the last few weeks, FormBook was seen downloading other malware families such as NanoCore. The credentials and other data harvested by successful FormBook infections could be used for additional cyber crime activities including, but not limited to: identity theft, continued phishing operations, bank fraud and extortion.”