Your Android phone says it’s fully patched, but is it really?
How do fully-maintained (i.e., patched) Android phones end up getting exploited? Searching for an answer to that question spurred security researchers to analyze thousands of Android firmwares for the presence of hundreds of patches.
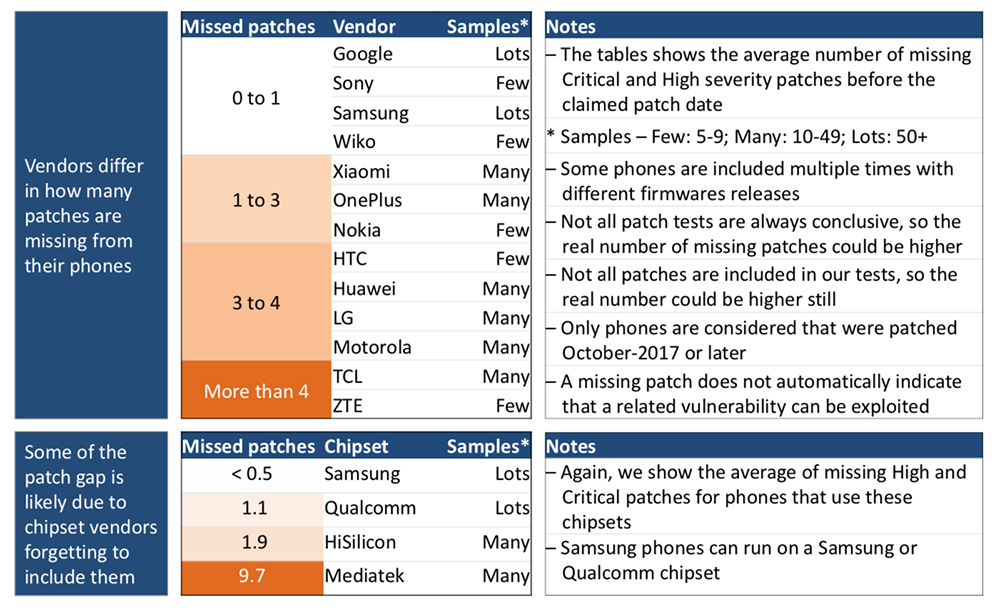
Their research led to an unwelcome discovery: most Android vendors regularly forget to include some patches in the security updates provided to users.
The research
Security Research Labs researchers Jakob Lell and Karsten Nohl explained how they went about making the analysis and revealed the results on Friday at the Hack in the Box Conference in Amsterdam.
They tested only devices operating on a recent patch level and, by applying a binary-only analysis technique (and limiting the probe to a limited number of patches for Critical or High severity bugs), they found that patching completeness varies widely for different phones.
Whether some of the patches are forgot or deliberately omitted is unknown, but the gap exists. And it’s difficult for users to be even aware of this problem, as their smartphones show just that a certain patch level has been achieved, but not what patches have actually been included.
To help them, the researchers released SnoopSnitch, a free app that measures the patch level of the Android device on which it is installed.
It has been pointed out in the past many times that Android mode vendors should push out patches more frequently, and many of them have improved in that respect and have started pushing out monthly security updates.
“Now that monthly patches are an accepted baseline for many phones, it’s time to ask for each monthly update to cover all relevant patches. And it’s time to start verifying vendor claims about the security of our devices,” the researchers noted.
At the moment, Google, Samsung, Sony lead the list of vendors with the most complete patch record, and TLC and ZTE are way down on it.
Android bug exploitation is difficult
The researchers made sure to point out that missing patch does not automatically indicate that a related vulnerability can be exploited.
In fact, the implementation of various defense mechanisms (exploit mitigation techniques, sandboxing, etc.) means that, more often than not, attackers have to chain together exploits for several vulnerabilities in order to hack the device.
Remote Android exploitation is, therefore, more much complicated than commonly thought.
“The criminal ecosystem seems to understand the challenges in hacking Android phones. Instead criminals focus on social engineering users into installing malicious apps, often from insecure sources, and then granting excessive permissions to these apps. In fact, hardly any criminal hacking activity has been observed around Android over the past year,” the researchers pointed out.
“That leaves state-sponsored and other persistent hackers, who usually operate stealthily. These well-funded hackers would typically resort to ‘zero day’ vulnerabilities but may also rely on known bugs to develop effective exploit chains. Patching these known bugs hence increases the effort for very determined hackers.”