Exfiltrating private keys from air-gapped cold wallets
Air-gapped cold wallets might be one of the safest options for keeping your cryptocurrency stash, but even they can be compromised. And, as demonstrated by security researchers from the Ben-Gurion University of the Negev, Israel, extracting private keys from such a wallet can be done relatively easily.
Pulling off the attacks
The attacks they demonstrated rely on the offline wallet being already compromised by malware, but once that’s achieved the keys can be sent to and received by a nearby smartphone equipped with software that receives the electromagnetic or ultrasonic signals carrying the information.
“The malware can be preinstalled or pushed in during the initial installation of the wallet, or it can infect the system when removable media (e.g., USB flash drive) is inserted into the wallet’s computer in order to sign a transaction,” the researchers explained.
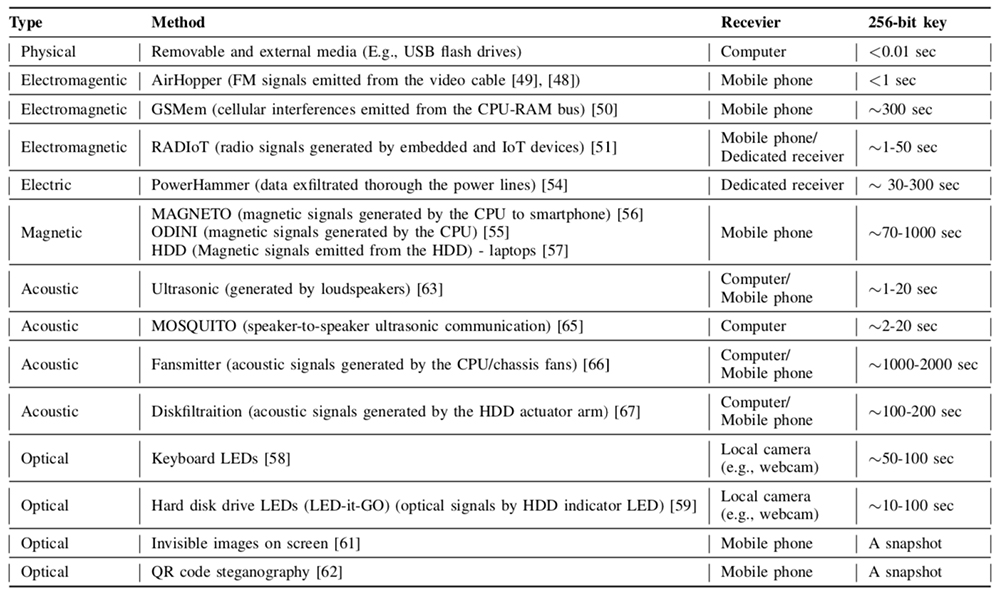
They’ve tested a number of covert ways to exfiltrate those private keys, using techniques they and others devised. Some are more effective than others, and some would not work at all.
For example, by using radio signals generated by the wallet an attacker can exfiltrate the key to the smartphone device in less than 15 seconds. And, as seen in the second demonstration video, doing it via ultrasonic signals can shorten that time to 3 seconds.
Countermeasures
There are ways for wallet owners to keep their devices safe from these types of attacks.
“A basic hardware-based countermeasure scheme involves shielding computers with metallic materials to prevent electromagnetic radiation from leaking from the shielded equipment. However, it is less suitable for private users due to the maintenance required and cost,” the researchers noted.
“When a highly valuable wallet is involved, a signal jamming approach might be taken. In this approach, a specialized hardware transmitter continuously generates random noises that interfere with potential transmissions from the wallet. Jamming is primarily used to block of electromagentic and acoustic signals.”